Browsing Category
Tutorials
112 posts
Penetration Testing Labs Online Course 2026
Hands-on Penetration Testing Labs plus OSINT, NMap, Nessus What is in Course Bundle? Hacking Web Applications & Penetration…
January 3, 2020
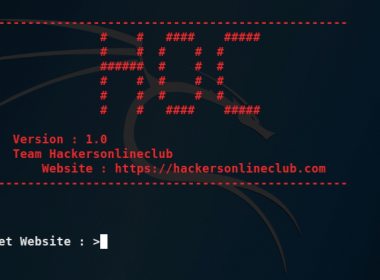
HOC IG – HackersOnlineClub’s Automatic Information Gathering Tool
Today, we are presenting our own Intelligence Information Gathering suite HOC IG – HackersOnlineClub’s Automatic Information Gathering Tool…
December 26, 2019
TheHarvester – OSINT Suite To Track Digital Footprints
Today, we are demonstrating tutorial on Open-source intelligence Information Gathering suite TheHarvester. Please check the POC Video at the end…
December 13, 2019
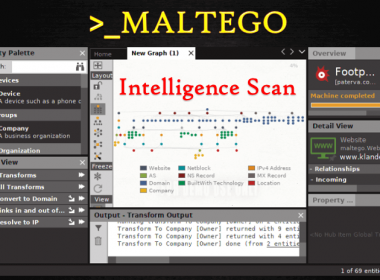
How To Run Maltego – Cyber Intelligence And Forensics Software
Today, we are working on Maltego – A Cyber Intelligence software. The basic use of the Maltego application…
December 11, 2019
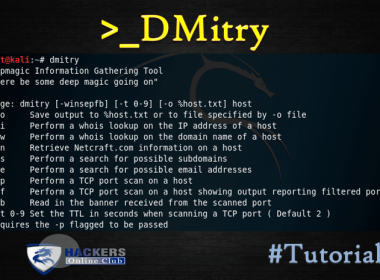
DMitry- Deepmagic Information Gathering Suite
Today, we are going to introduce you about Dimitri (Deepmagic Information Gathering Tool). DMitry has the ability to…
December 7, 2019
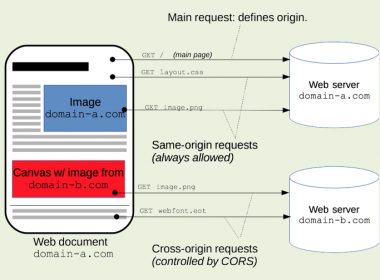
Cross Origin Resource Sharing CORS Misconfiguration Impact
The Cross Origin Resource Sharing CORS standard describes new HTTP headers which provide browsers a way to request…
December 6, 2019
BurpSuite Series | Payload Processing Rules- Part 2
In our previous article we have discussed about the “Payload Processing Rule in Burp Suite Series – (Part…
December 4, 2019
XML External Entity (XXE) Injection Payload Cheatsheet
XML External Entity (XXE) Injection Payload list In this article, we will explain what XML external entity injection…
December 3, 2019
BurpSuite Series- Payload Processing Rules – Part 1
Burpsuite Payload Processing Rules WORKING – Today, we are going to overview the Intruder feature “Payload Processing Rule”…
November 30, 2019
Black Friday Sale- Information Security Certificates Bundle
Learn to pass CEH, CISM, CISA and CISSP in one bundle! Enroll for 90% off on original price offer Course…
November 29, 2019