Burpsuite Payload Processing Rules WORKING – Today, we are going to overview the Intruder feature “Payload Processing Rule” option in the Burp Suite . It’s comes under the Intruder tab for advanced functionality Brute force attack on web application.
This is the FIRST Part of Burpsuite Payload Processing Rules working.
When payloads are generated using payload types, they can be manipulated or filtered using different processing rules and payload encoding.
- These rules are defined to perform different processing tasks before using each payload.
- These rules are executed in a sequence and can be used to help debug any problem in the configuration.
Payload processing rules are useful in situations where you have to produce different payloads, or when you want to wrap payloads in a wider structure or encoding scheme.
There are 12 types of Burpsuite payload processing rules available
- Add prefix
- Add suffix
- Match / Replace
- Substring
- Reverse substring
- Modify case
- Encode
- Decode
- Hash
- Add raw payload
- Skip if matches regex
- Invoke Burp extension
Also See – How To Use Runtime File Payload in BurpSuite
Add prefix
This processing rule adds a prefix before the payload.
First, ensure that Burp is correctly configured with your browser.
Follow the steps.
To configure Burpsuite Payload Processing demonstrate.
First Go to your browser settings and in the search box type proxy, then select open proxy settings > In connection tabs > Lan settings > Tick Use a proxy server for your LAN > (127.0.0.1 port number 8080) then Click ok.

You can see below Video to Setup Burp Suite in Windows OS
Now open the Burp Suite
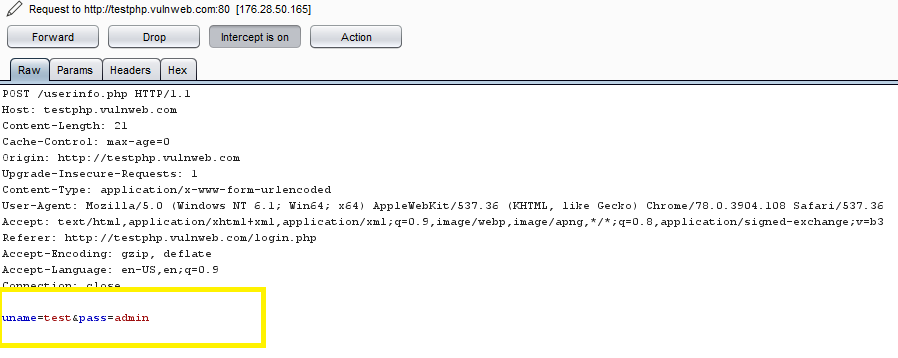
In the Burp Proxy tab, ensure “Intercept is off” and visit the login page of the application, which you are testing in your browser.

Turn on Intercept

Here we are demonstrating on testphp.vulnweb.com
In your browser, enter the default username and wrong password, then submit the request to intercept the browser request using a burp suite.
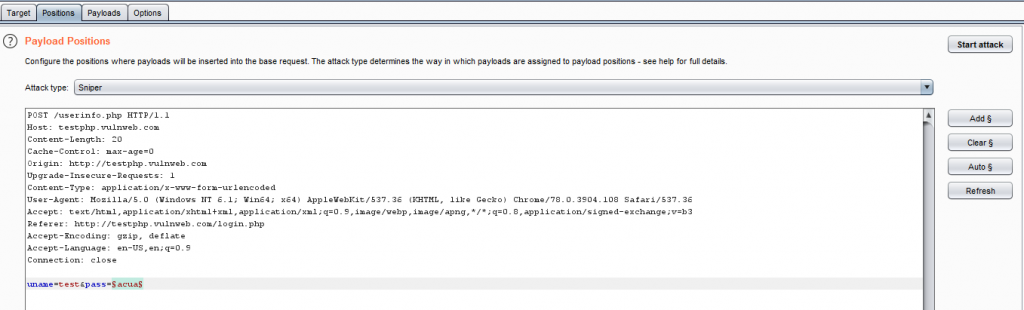
Right click on the request to bring up the context menu and click “Send to Intruder.”
- Click on the Clear button to the right of the window frame.
- Now we will select the fields where we want to attack and i.e. the password filed and click on Add button.
- Select the attack type as a sniper
- In the image below, we have selected a password which means we need a dictionary files for the password.
Go to the “Payloads” tab. In the “Payload sets” settings, ensure “Payload set” is “1” and “Payload type” is set to “Brute forcer” and select the min and max length in payload options.
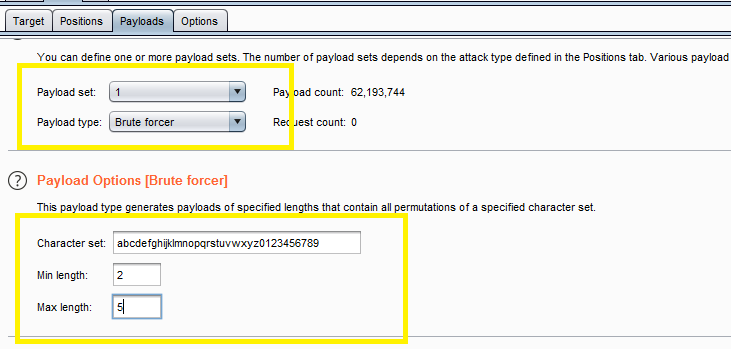
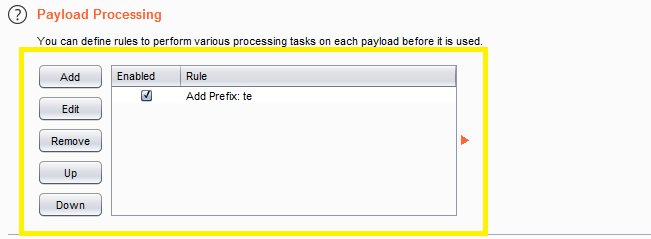
Before executing the attack we have added a payload processing rule to the payload type which is Add Prefix and we have given an input string “te” which is added as a prefix with every input strings in the dictionary, as shown in the result window of the attack.
After that Select Start Attack in the Intruder menu.
In the “Intruder attack” window, you can sort the results using the column headers. In this example sort by “Length” and by “Status.”
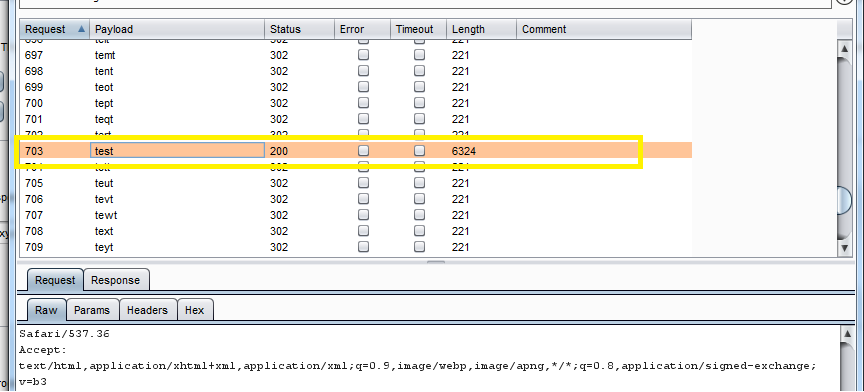
By viewing the response in the attack window, we can see that request 6324 is logged in as a “test.“
And to confirm the password matched, we will give the password in the testphp.vulnweb.com , which will successfully log us into the Test.
Add Suffix
This processing rule adds up a suffix after the payload.
Same as previous demonstration but added a payload processing rule to the payload type which is Add Suffix and we have given an input string “1234” which is added as a prefix with every input strings in the dictionary as follows:
- tast1234
- tbst1234
- tcst1234
- tdst1234
- test1234
Match / Replace
This processing rule is used to replace any part of the payload that match a specific regular expression, with a string.
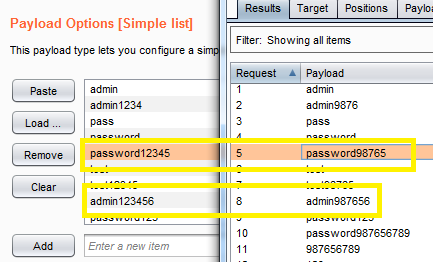
In a payload processing rule to the payload type establishing a Match/Replace and inputting a “1234” in the Match Regex, which matches the input given to the input strings in the dictionary. If there is a certain match than it will replace it with the input “9876” given in the Replace with as shown in the image.
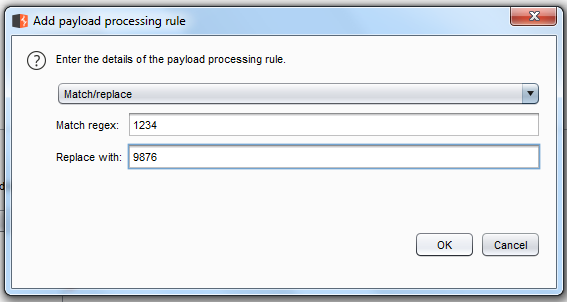
Now the Burp Suite finds the correct value and it changes the length value as shown in the figure.
Substring
This processing rule is used to capture a sub-part of the payload that starts from the specified offset to the specified length. Here the offset and length are calculated from the front.
The payload processing rule Substring we have given input “0” in the option, which specifies the offset and specifies the length of the input string in the “4” length option.
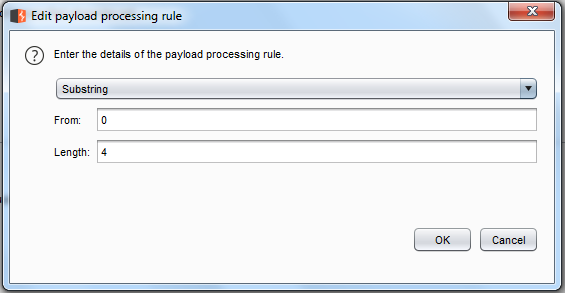
For example, “password” is a word in a dictionary and if we apply it on the filter it keeps the alphabet p = 0; a = 1; s = 2 and s = 3 so it will only pass from the whole word “password”.
Reverse Substring
This processing rule is used as the substring rule, but the payload counts from end to back end offset is specified and end is counted backwards from the offset.
The payload processing rule reverse substring for the payload type we have input “2” in the option, which specifies the offset and specifies the length of the input string “9” in the length option and they are the same as the substring rule but it operates from behind the offset and ends where the offset ends counted.
For example if “admin123456” is word in dictionary and we had applied above filter so it will place alphabet 4 = 0; 3 = 1 ; 2 = 2 ; 1 = 3 ; n = 4 ; i = 5 ; m = 6 ; d = 7 ; d = 8 ; a = 9 hence it will read only ‘admin1234’ from whole word “admin123456”.
Also See – BurpSuite Spider Feature Working
Modify Case
This processing rule can be used to modify the case of the payload if needed. This rule has the same options available for the Case Modification payload type
It allows you to configure a list of strings and apply various case modifications to each item on the list, and it is useful in password guessing attacks, for generating case variations on dictionary words.
The following case modification rules can be selected:
- No change – The item is used without being modified.
- To lower case – All letters in the item are converted to lower case.
- To upper case – All letters in the item are converted to upper case.
- To Proper name – The first letter in the item is converted to upper case, and the remaining letters are converted to lower case.
- To Proper Name – The first letter in the item is converted to upper case, and the remaining letters are not changed.
For example, if we select all the modification options, then the item “hackers online club” will generate the following payloads:
- Hackers Online Club
- hackers online club
- HACKERS ONLINE CLUB
- Hackers online club
For PART 2 – BurpSuite Series- Payload Processing Rules Working – Click here
Disclaimer: This tutorial is knowledge purpose only.