
Browser Security
- How Web Browsers Get Hacked?
- Learn How To Secure Browser?
- Open Source Privacy Focused Browser?
Today, the most popular desktop browsers are Chrome, Safari and Firefox and Opera. While most commonly used to access information on the web, a browser can also be used to access information hosted on Web servers in private networks.
It is the application of Internet security to web browsers in order to protect networked data and computer systems from breaches of privacy or malware. Security exploits of browsers often use JavaScript — sometimes with Cross-site scripting (XSS), sometimes with a secondary payload using Adobe Flash.
Security exploits can also take advantage of vulnerabilities (security holes) that are commonly exploited in all browsers (including Mozilla Firefox, Google Chrome, Opera, Microsoft Internet Explorer, and Safari).
Plugins and Extensions
Although not part of the browser per se, browser plugins and extensions extend the attack surface, exposing vulnerabilities in Adobe Flash Player, Adobe (Acrobat) Reader, Java plugin, and ActiveX that are commonly exploited.
Malware may also be implemented as a browser extension, such as a browser helper object in the case of Internet Explorer. Browsers like Google Chrome and Mozilla Firefox can block—or warn users of—insecure plugins.
By using Camera/Microphone usage
We need to block from running it automatically or have the browser ask you each time a website wants to use the camera or microphone. Only allow for trustworthy web or applications.
How Browser gets Hacked?
The Browser can be hacked through some Malware program activities which can modify your browser settings without your permission and redirects the user to other websites which includes malicious Ad campaigns.
It can change your browser homepage, search engine and install unknown toolbars which leads to illegitimate pop up advertisements.
The aim is to help the cyber criminal to generate money through fake advertisements. When users click on the search engine or Redirect URL the attackers gets paid. They will also know your browsing activities to sell private information to third parties.
Browser hacking malware might be installed Ransomware that encrypts your data and keeps hold until you pay the ransom money to the cyber criminal.
How To Secure Your Browser?
- Keep browser Updated.
- Always use Internet Antivirus, it includes your web browser security features.
- To check your browser add-ons, if you find any unknown add-on or plugin then immediately remove that from your browser.
- Before closing the Browser, delete your Browser history, cookies and cache.
- Do not click on unknown Link, attached mail.
- Use Ad block to block Pop-ups and Ad script.
- Never store your password, bank details, credit card details in the browser.
- NoScript or ScriptSafe: Popular programs that block scripts on websites until the user specifically enables them
- Flashblock: An add-on that prevents Flash ads from playing until the user specifically allows them
- HTTPS Everywhere: An add-on jointly created by the Electronic Frontier Foundation and The Tor Project that encrypts your web browsing traffic.
Browsers can use more secure methods of network communication to help prevent some of these attacks:
DNS: DNSSec and DNSCrypt, for example with non-default DNS servers such as Google Public DNS or OpenDNS.
HTTP: HTTP Secure and SPDY with digitally signed public key certificates or Extended Validation Certificates.
Open Source Browser
It’s a new way to browse the web with transparency, security, and freedom. A group of developers builds and maintains these browsers, collaborating and improving them.
It’s free for anyone to inspect and modify the code for open source browsers, so there are no hidden backdoors. Adding new features and improving performance is also easier because it makes it easier to find and fix security vulnerabilities.
Also, open source browsers tend to be more privacy-focused. Open source browsers put privacy first instead of proprietary ones, which are owned by companies that collect user data. Their online activities are less likely to be tracked, so they won’t store your personal information.
Here is a list of some of the most privacy-focused open source browsers:
-

Privacy Anonymity Mozilla Firefox – has a number of privacy features built in, such as private browsing mode, and the ability to block third-party trackers.
- Brave – blocks third-party ads and trackers by default, and offers a number of other privacy-focused features, such as HTTPS Everywhere and script blocking.
- Tor Browser – TOR routes your internet traffic through a network of volunteer nodes, providing a high level of privacy and security, and is especially well-suited for users who are concerned about online surveillance.
- Waterfox – prioritizes privacy and performance, and is designed to be highly customizable, allowing users to make further adjustments to their privacy settings.
- Falkon – a lightweight, fast, and user-friendly browser that is designed to be privacy-friendly.
- Gnuzilla – a version of Mozilla Firefox that is completely free of any trademarked technology or branding, and is designed to be as private and secure as possible.
- Midori – a fast and lightweight browser for Linux and other Unix-like systems, that focuses on speed and privacy, and includes features such as ad-blocking and cookie management.
Open source privacy browsers can help protect your online privacy while supporting a community of developers who strive to create better and more secure web tools. Despite the fact that these browsers provide privacy-focused features, there are always inherent risks associated with surfing the internet, so using them does not guarantee 100% privacy. But yes, using a VPN, avoiding public wireless networks, and being mindful of the information you share on the Internet are all ways to ensure your online privacy is protected to the extent of your ability.
Hardening Browser
Browsing the Internet as a least-privilege user account (i.e. without administrator privileges) limits the ability of a security exploit in a web browser from compromising the whole operating system.
Suspected malware sites reported to Google, and confirmed by Google, are flagged as hosting malware in certain browsers.
There are third-party extensions and plugins available to harden even the latest browsers, and some for older browsers and operating systems. Whitelist-based software such as NoScript can block JavaScript and Adobe Flash which is used for most attacks on privacy, allowing users to choose only sites they know are safe – AdBlock Plus also uses white-list ad filtering rules subscriptions, though both the software itself and the filtering list maintainers have come under controversy for by-default allowing some sites to pass the pre-set filters. Many of intelligence agencies recommend to blocking Flash using NoScript.
Need To Know?
Always check HTTPS for Top Websites. HTTPS is encryption layer used to secure against attackers with access to the network from changing the page contents en route.
For normal password usage on the WWW, when the user is confronted by a dialog asking for their password, they are supposed to look at the address bar to determine whether the domain name in the address bar is the correct place to send the password.
For example: If you are surfing Bank websites, always check HTTPS sign-on system (used on e.g. anybank.com), the user should always check that the address bar says “https://anybank.com” before entering your password id.
Browser Security Chrome
Avoid dangerous websites
Chrome technology protects you from a range of deceptive and dangerous sites and downloads that might steal passwords or infect your machine. If we think something seems suspicious, you’ll see a warning.
Chrome automatically updates every six weeks so that you always have the latest security features and fixes. For important security bugs, we’ve pushed out a fix within 24 hours – no effort from you required.
Chrome Advanced technology such as site isolation, sandboxing and predictive phishing protection keep you safe from security threats.
Browser Security Safari
Safari warns you if the site you’re visiting is a suspected phishing website. Phishing is a fraudulent attempt to steal your personal information, such as usernames, passwords and other account information.
A fraudulent website masquerades as a legitimate one, such as a bank, financial institution or email service provider. Before you visit a website, Safari may send information calculated from the website address to Google Safe Browsing to check if the website is fraudulent.
How To Prevent cross-site tracking in Safari on Mac
Some websites use third-party content providers. You can stop third-party content providers from tracking you across websites to advertise products and services.
- Open Safari app on your Mac, choose Safari > Preferences, then click Privacy.
- Select “Prevent cross-site tracking”.
- Unless you visit and interact with the third-party content provider as a first-party website, their cookies and website data are deleted.
Social media sites often put Share, Like or Comment buttons on other websites. These buttons can be used to track your web browsing — even if you don’t use them. Safari blocks that tracking. If you still want to use the buttons, you’ll be asked for your permission to allow the site to see your activities on the other websites.
To See who was blocked from tracking you in Safari on Mac
You can see who’s been blocked from tracking you when you visit a website.
- In the Safari app on your Mac, enter the page’s name or URL in the Smart Search field.
- Click the Privacy Report button in the toolbar.
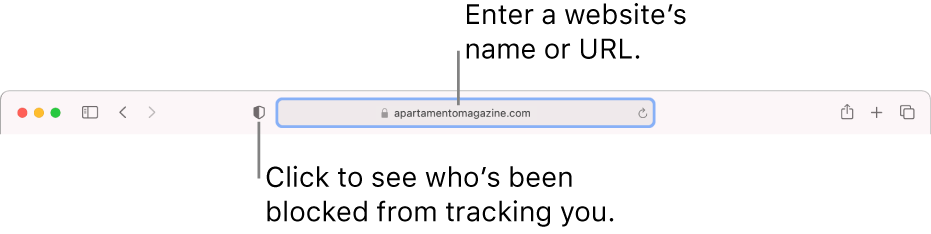
For a Privacy Report that shows a list of known trackers who’ve been blocked from tracking you, choose Safari > Privacy Report.




