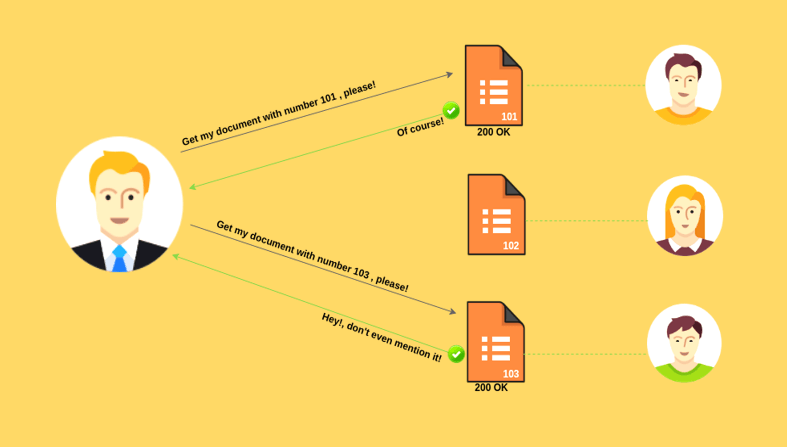
Insecure Direct Object References (IDOR) Vulnerability allows attackers to bypass authorization and access resources directly by modifying the value of a parameter to point directly to an object.
-
IDOR Examples
-
IDOR Working
-
IDOR Preventions
You can see the Authentication Video Example at the end of the article.
Such resources can be database entries belonging to other users, files in the system, and more. This is caused by the fact that the application takes user-supplied input and uses it to retrieve an object without performing sufficient authorization checks.
IDOR occurs when an application provides direct access to objects based on user-supplied input. As a result of this vulnerability, attackers can bypass authorization and access resources in the system directly, for example database records or files.
IDOR Example Attack Scenarios
The application uses unverified data in a SQL call that is accessing account information:
String query = "SELECT * FROM accts WHERE account = ?";
PreparedStatement pstmt = connection.prepareStatement(query , ... );
pstmt.setString( 1, request.getParameter("acct"));
ResultSet results = pstmt.executeQuery();
The attacker simply modifies the ‘acct’ parameter in their browser to send whatever account number they want. If not verified, the attacker can access any user’s account, instead of only the intended customer’s account.
http://example.com/app/accountInfo?acct=notmyacct
IDOR Working
Requirements
- Burpsuite for temper the request
- Web For Pentester II for testing
- Python for Script running
Also See – How to Install Web for Pentester II
Examples:
Once you installed Web for Pentester > Authentication > Example 3 ,
Here you can log in as user1. Your goal is to get logged in as admin. To do so, you need to carefully look at the response sent back by the server.

Its a cookie manipulation exploit, when you login the server will set up a cookie named user1 with a value user1.
For cookie manipulation just right click > inspect

In the Application tab, click cookies and edit the value user1 to admin
application > cookies and edit “value”


Just re-enter example 3 and we are enter as a admin.

Example :-
Now do the same thing as above, go to Web for Pentester > Authentication > Example 4.
This example is the same as the previous one cookie manipulation exploit only the difference, it’s value is encrypted.

By decrypting the value we get ‘user1’

By encrypting the admin we get

Now we have to replace the user1 encrypted value with admin encrypted value and re-enter example 4 and we can enter as admin.
Also Read- Exploiting Authentication Issues Of Web Application
IDOR Vulnerability Prevention
All the areas where the application makes direct reference to an internal object. Afterwards make a strict access control rules, validate all the user input and make sure it is validated both client and server side and at the end.
Preventing insecure direct object references requires selecting an approach for protecting each user accessible object (e.g., object number, filename):
Use per user or session indirect object references. This prevents attackers from directly targeting unauthorized resources.
For example, instead of using the resource’s database key, a drop down list of six resources authorized for the current user could use the numbers 1 to 6 to indicate which value the user selected. The application has to map the per-user indirect reference back to the actual database key on the server.
OWASP’s ESAPI includes both sequential and random access reference maps that developers can use to eliminate direct object references.
Each use of a direct object reference from an untrusted source must include an access control check to ensure the user is authorized for the requested object.