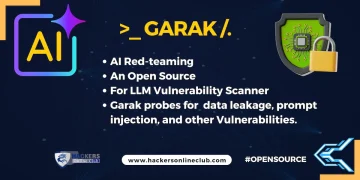
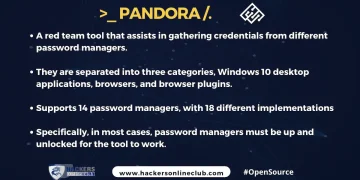
Open Source
TUTORIAL
Netdiscover – To Scan Live Hosts In Network
September 15, 2023
How to Find Web Server Vulnerabilities With Nikto Scanner
August 17, 2023
How To Use PING Command?
April 9, 2024
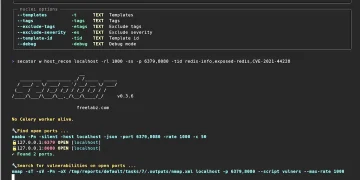
NETCAT- To Scan Open Ports
June 12, 2021