Advance Operating System is an interface between the software applications and hardware with level of packaging.
What is the best operating system for hacking?
The best operating system for hacking depends on your needs and goals. Take a look at these popular options:
Linux: The open-source nature of Linux and powerful command-line interface make it a popular choice for hackers and security pros. Many popular hacking tools and utilities are designed to work with Linux, and the operating system is known for its flexibility and customization options.
macOS: While not as widely used as Linux, macOS is another popular operating system among hackers. It is known for its security and reliability, and offers a range of powerful tools and utilities for hacking and security testing.
Windows: While not as popular among hackers as Linux or macOS, Windows is still a commonly used operating system for hacking. It has a large user base and is widely supported, making it a good choice for those who are new to hacking and want an operating system that is easy to use and access.
Ultimately, the best operating system for hacking will depend on your specific needs and goals. Linux, macOS, and Windows are all popular options, and each has its own strengths and limitations. It’s important to carefully consider your requirements and choose the operating system that is best suited to your needs.
6 Top Advance Operating System Designs For Security Testing and Anonymity
1. Kali Linux
Kali Linux is a Debian-derived Linux distribution designed for digital forensics and penetration testing. It is maintained and funded by Offensive Security Ltd.
Kali Linux has over 600 preinstalled penetration-testing programs, including Armitage (a graphical cyber attack management tool), Nmap (a port scanner), Wireshark (a packet analyzer), John the Ripper password cracker, Aircrack-ng (a software suite for penetration-testing wireless LANs), Burp suite and OWASP ZAP web application security scanners.
Kali Linux can run natively when installed on a computer’s hard disk, can be booted from a live CD or live USB, or it can run within a virtual machine. It is a supported platform of the Metasploit Project’s Metasploit Framework, a tool for developing and executing security exploits.
2. Parrot Operating System
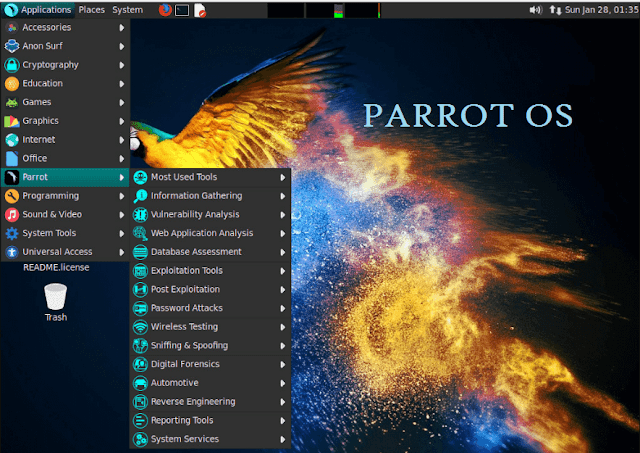
Parrot is a GNU/Linux distribution based on Debian Testing and designed with Security, Development and Privacy in mind. It includes a full portable laboratory for security and digital forensics experts, but it also includes all you need to develop your own software or protect your privacy while surfing the net.
Parrot Security is our complete all-in-one environment for pentesting, privacy, digital forensics, reverse engineering and software development.
3. BlackArch Linux
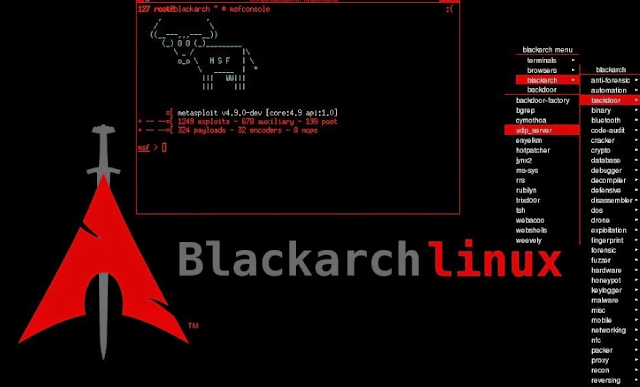
BlackArch Linux is an Arch Linux-based penetration testing distribution for penetration testers and security researchers. The repository contains 2082 tools. You can install tools individually or in groups. BlackArch Linux is compatible with existing Arch installs.
In the new BlackArch Linux ISOs and OVA image. For details see the ChangeLog below.
Here’s the new ChangeLog:
- added more than 150 new tools
- enabled wicd service by default
- removed dwm window manager
- removed wmii window manager
- added bactl package (script to config and setup BlackArch environment)
- included every tool of BlackArch except: cuda-/oclhashcat, vmcloak, theZoo
- included linux kernel 4.19.4
- included wordlistctl (https://github.com/BlackArch/wordlistctl))
- updated blackarch-installer to v1.0.3
- updated default ISO files (synced with archiso’s template)
- package QAs (runtime checks) were performed prior the ISO build
- updated all blackarch tools and packages including config files
- updated all system packages
- updated all window manager menus (awesome, fluxbox, openbox)
4. Whonix OS
Whonix is a free and open-source desktop operating system (OS) that is specifically designed for advanced security and privacy. Based on Tor, Debian GNU/Linux and the principle of security by isolation, Whonix realistically addresses common attack vectors while maintaining usability.

Online anonymity and censorship circumvention is attainable via fail-safe, automatic and desktop-wide use of the Tor network, meaning all connections are forced through Tor or blocked. The Tor network helps to protect from traffic analysis by bouncing communications around a distributed network of relays run by global volunteers.
Without advanced, end-to-end, netflow correlation attacks, an adversary watching an Internet connection cannot easily determine the sites visited, and those sites cannot discover the user’s physical location. Whonix uses an extensively reconfigured Debian base which is run inside multiple virtual machines (VMs) on top of the host OS
5. Qubes OS
Qubes is an open source operating system designed to provide strong security for desktop computing. Qubes is based on Xen, X Window System, and Linux, and can run most Linux applications and utilize most of the Linux drivers.
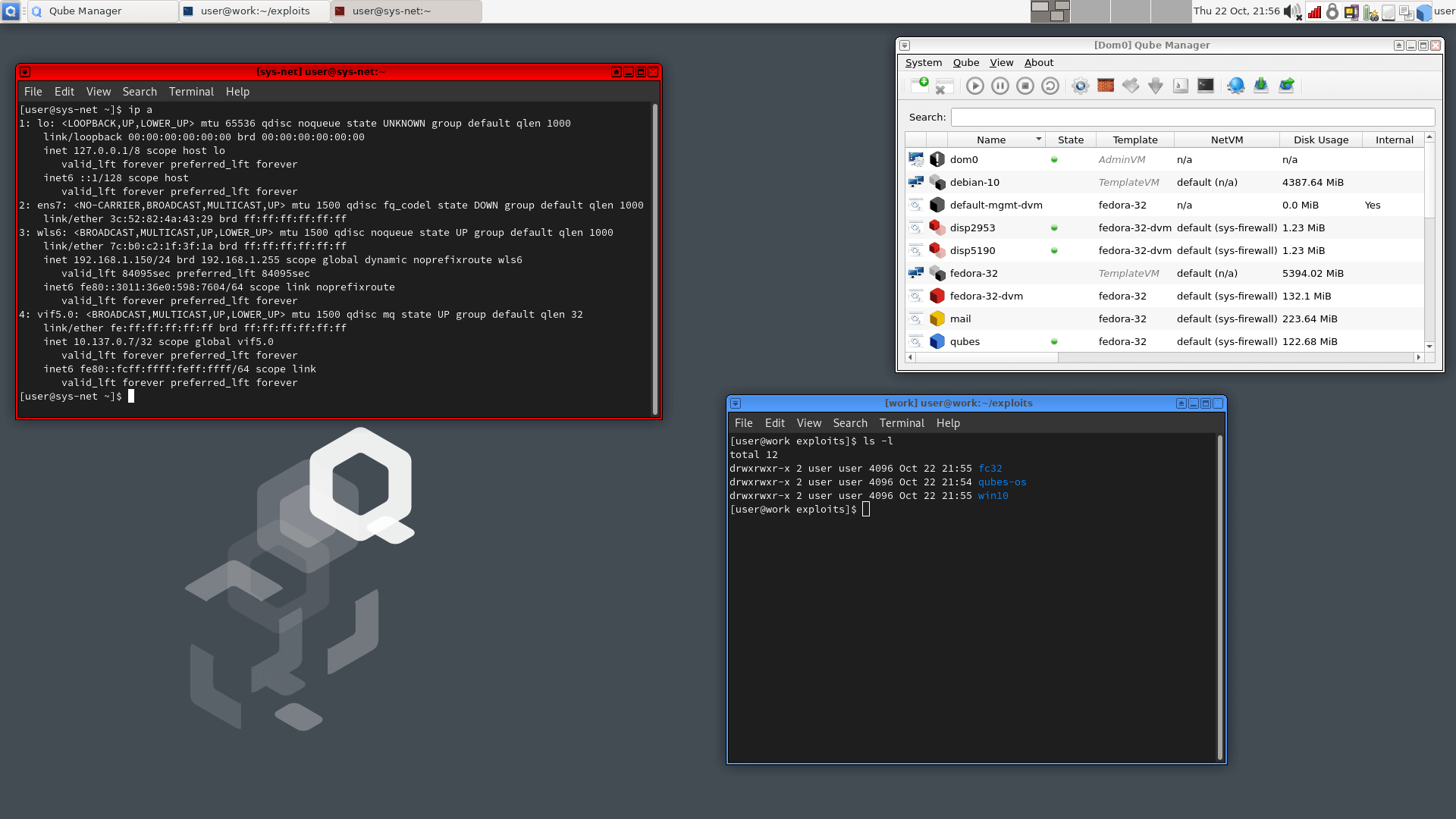
>> Key architecture features:
- Based on a secure bare-metal hypervisor (Xen).
- Networking code sandboxed in an unprivileged VM (using IOMMU/VT-d).
- No networking code in the privileged domain (dom0).
- All user applications run in “AppVMs”, lightweight VMs based on Linux.
- Centralised updates of all AppVMs based on the same template.
- Qubes GUI virtualization presents applications like if they were running locally.
- Qubes GUI provides isolation between apps sharing the same desktop.
- Storage drivers and backends sandboxed in an unprivileged virtual machine.
- Secure system boot based on Intel TXT.
6. Tails
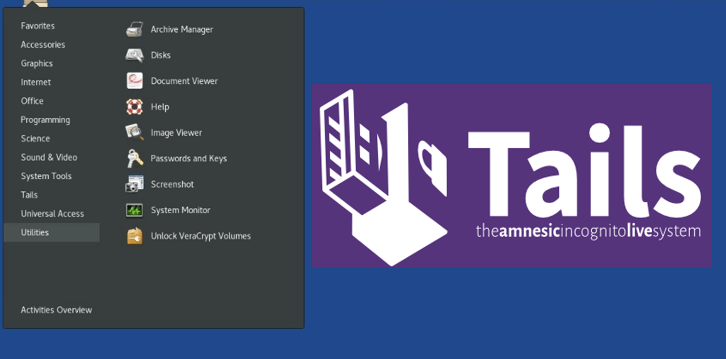
Tails is a Incognito Live Operating System that aims to preserve your privacy and anonymity. It helps you to use the Internet anonymously and circumvent censorship almost anywhere you go and on any computer but leaving no trace unless you ask it to explicitly.
It is a complete operating system designed to be used from a USB stick or a DVD independently of the computer’s original operating system. It is Free Software and based on Debian GNU/Linux.
Tails comes with several built-in applications pre-configured with security in mind: web browser, instant messaging client, email client, office suite, image and sound editor, etc.




