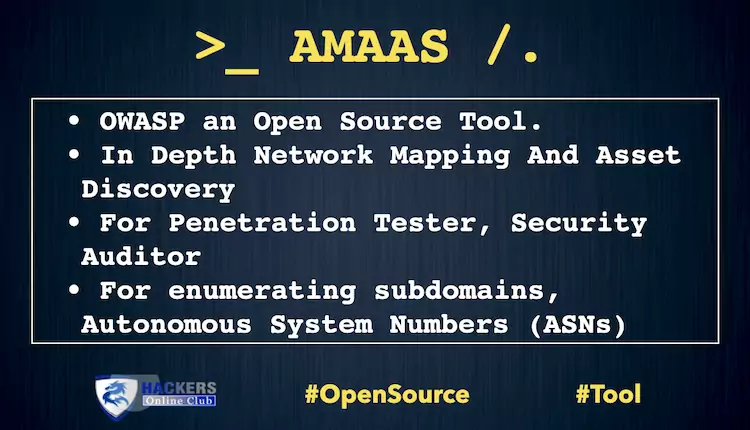
Introduction
Why OWASP Amass?
- amass intel — Discover targets for enumerations
- amass enum — Perform enumerations and network mapping
- amass viz — Visualize enumeration results
- amass track — Track differences between enumerations
- amass db — Manipulate the Amass graph database
Command-line Usage Information
Subcommand Description
- intel : Collect open source intelligence for investigation of the target organization
- enum Perform DNS enumeration and network mapping of systems exposed to the Internet
- viz Generate visualizations of enumerations for exploratory analysis
- track Compare results of enumerations against common target organizations
- db Manage the graph databases storing the enumeration results
- amass enum -list
- AlienVault,ArchiveIt,ArchiveToday,Arquivo,Ask,Baidu,BinaryEdge,Bing,BufferOver,Censys,CertSpotter,CIRCL,CommonCrawl,Crtsh,[…],ViewDNS,VirusTotal,Wayback,WhoisXML,Yahoo (full list here)
- Brute-force of subdomains using a domain name wordlists and alteration wordlists
- Identify subdomains by reading SSL/TLS certificates, performing DNS zone transfers or checking certificate transparency logs
- Recursive subdomain discovery on identified domains
- Hashcat-style masks for brute-force of subdomains (this can be very useful if you have internal information on naming conventions and so on)
- It can be configured using a configuration file which makes it easy to maintain, use or integrate with scripts
Amass Enum
Let’s move onto Amass enum, which is where most of Amass’ powerful capabilities live. Amass enum allows you to perform DNS enumeration and network mapping of the target in order to determine the attack surface exposed by organisations.
The enumeration findings are stored in a graph database, which will be located in Amass’ default output folder or the specified output directory with “-dir” flag. This is also the case with other Amass subcommands.
Amass Intel
The Amass intel subcommand, or module if you want, can aid with collecting open source intelligence on the organisation and allow you to find further root domain names associated with the organisation. To see the available options of this subcommand, simply type it at the terminal:
$ amass intel [...] Usage: amass intel [options] [-whois -d DOMAIN] [-addr ADDR -asn ASN -cidr CIDR] -active Attempt certificate name grabs -addr value IPs and ranges (192.168.1.1-254) separated by commas -asn value ASNs separated by commas (can be used multiple times) [...]
It is probably worth noting at this point that another great perk of Amass is that all the subcommands attempt to maintain argument consistency.
Amass Track
Amass Viz and Amass DB
$ amass db -dir amass4owasp -list
$ amass db -dir amass4owasp -d owasp.org -enum 1 -show
Amass Viz
$ amass viz -d3 -dir amass4owasp
Installation
Prebuilt Packages
- Simply unzip the package
- Put the precompiled binary into your path
- Start using OWASP Amass!
brew tap caffix/amass brew install amass
sudo snap install amass
Kali Linux
OWASP Amass is installed by default and can be managed like any other Kali package:
apt-get update apt-get install amass
- Install Go and setup your Go workspace
- Download OWASP Amass by running go install -v github.com/OWASP/Amass/v3/…@master
- At this point, the binary should be in $GOPATH/bin