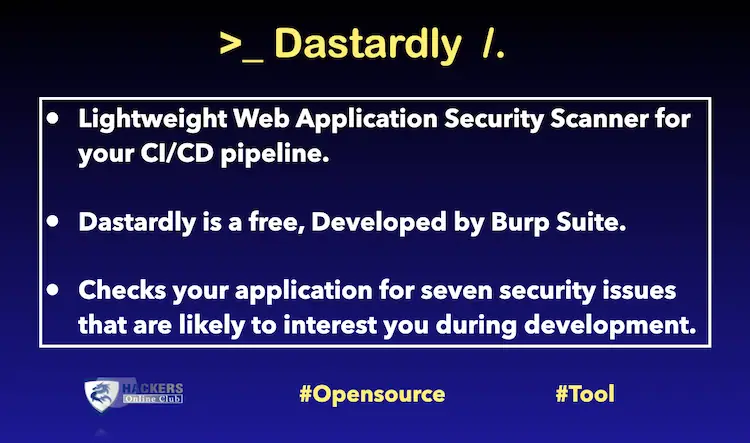
- Dastardly is a free, from Burp Suite.
- It is lightweight web application security scanner for your CI/CD pipeline.
- It is designed specifically for web developers, and checks your application for seven security issues that are likely to interest you during development.
- Runs a scan using Dastardly by Burp Suite against a target site and creates a JUnit XML report for the scan on completion.
This action runs a Dastardly vulnerability scan against a target site. On completion, a JUnit XML report is generated containing information about the vulnerabilities found, where they were located, additional information about the vulnerability and links to our learning resources with suggestions on how to fix them.
Burp Suite known as top security software used for penetration testing and web application security. Both a free and a paid version of the software are available. Dastardly is lightweight web application security scanner, and check seven most common web security issues.
Check BurpSuite Series Tutorials – Payload Processing Rules – Part 1 and Part 2
Scanning
Dastardly uses a Dynamic Application Security Testing (DAST) methodology to scan your target web application. This means that it scans your target application in a deployed state. This is unlike Static application security testing (SAST) scanning, which looks at application code before it is deployed.
When running a Dastardly scan, provide the seed URL you wish to scan. The seed URL is the point from which Dastardly scans your target web application. From here, Dastardly scans any URLs it finds below the seed URL in the hierarchy.
Scan length limit
Dastardly scans are capped at a maximum run time of ten minutes. This may not be enough time to scan larger or more complex web applications.
If your application is too large or complex for Dastardly to scan, you might want to try scanning with Burp Suite Enterprise Edition instead
Results
When your scan has finished, Dastardly outputs a report of its findings in JUnit XML format. This lists all vulnerabilities found during the scan. To help you pinpoint these issues, it also lists the requests Dastardly sent with the corresponding responses from your application.
Once you have identified and resolved any vulnerabilities, you can redeploy your build to perform another scan.
Build failures
To help keep your application secure, Dastardly fails your build if it detects any vulnerabilities with a severity level of LOW, MEDIUM, or HIGH.
Vulnerabilities with a severity level of INFO don’t trigger a build failure.
Dastardly system and network requirements
To run Dastardly, you need:
A machine with a minimum of 4 CPU cores and 4 GB of RAM. (Larger or more complex target applications may require more resources.)
A CI/CD build agent or node configured to:
- Run Docker containers.
- Access your target application.
- Access your target URL.
- Access PortSwigger’s public image repository (public.ecr.aws/portswigger/).
If you’re running Dastardly locally, or within a container, please make sure your network settings are configured correctly. Dastardly does not support any additional environment variables, such as proxies.
How To Use?
Inputs
target-url
Required The full URL (including scheme) of the site to scan.
output-filename
Optional The name of the output report file. This will be stored in the GITHUB_WORKSPACE (/github/workspace) directory.
Default dastardly-report.xml
You can check Live example on Github.
Dastardly can help you find following issues.
- Cross-site scripting (XSS) (reflected)
- Cross-origin resource sharing (CORS) issues
- Vulnerable JavaScript dependency
- Content type is not specified
- Multiple content types specified
- HTML does not specify charset
- Duplicate cookies set
Dastardly does not check following web vulnerable applications
- SQL injection
- DOM-based XSS
- Client-side prototype pollution
- HTTP request smuggling