ESET Security researcher found DDOS Attacks Through Malicious Android App.
Some of the Cyber threat actors was targeting ESET’s website, after that the company security researchers were able to identify the malicious app, and report to Google. Google has been removed it from the Play Store.
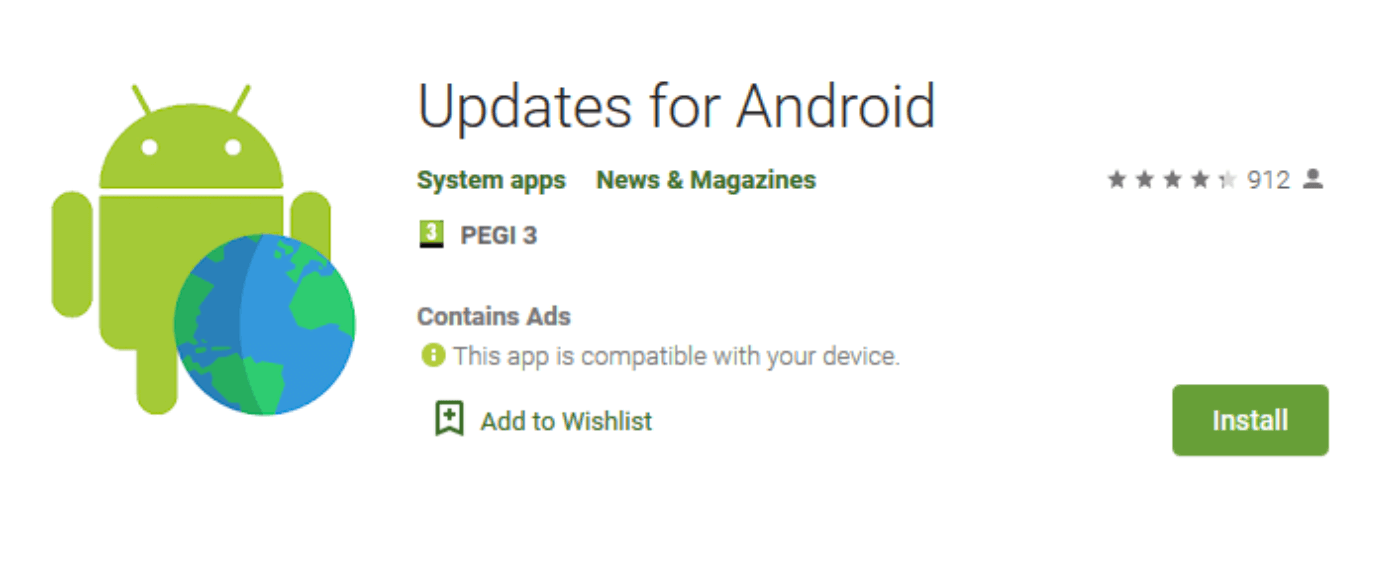
The malicious app called “Updates for Android”, it was active to the Play store since 9 September 2019. Also it promoted to Malwaretising.
According to Lukas Stefanko, Malware Researcher, ESET, the app’s original version lacked the functionality of loading JavaScript that was, ultimately, abused for carrying out the DDoS attack – it was added in the app’s most recent update two weeks prior to the attack.
The app reached over 50,000 installs; we don’t know how many instances of the app were installed after the update or were updated to the malicious version.
Working
The malicious android app has a corresponding website, i-updater[.]com, that promotes itself as “daily news updates”. (The website is still live; there are no grounds for any takedown effort as the website itself is not malicious.)
To avoid suspicion, the app displays some news; however, its main functionality is to receive commands from a pre-defined website that serves as the Command and Control server (C&C). The malware pings the C&C every 150 minutes and provides its device ID – a measure that allows for each device being controlled individually.
Based on the commands the app receives from the C&C, it can display ads in the user’s default browser (note: this functionality spans outside of the app), hide the presence of the app from the user by hiding the app’s icon, and execute arbitrary, remotely supplied JavaScript.
Based on the JavaScript code received by the app from its C&C, the device connects every second to the target website to flood it with traffic. This last functionality was used for carrying out the DDoS attack on the ESET website.
DDOS Attack
The DDoS attack starts with the compromised device receiving a command to load the attacker’s script that specifies the targeted domain. Once the script is loaded, the device starts making requests to the targeted domain until it is served with another script by the C&C server which may contain a different target domain.
Lukas said, since we started to monitor the website providing C&C functionality to the botnet, we witnessed another six scripts being served, each containing a different domain for the captive devices to attack.
Those were notable news and ecommerce sites, most of them in Turkey. Since February 2, the script is empty, meaning the attackers tried to serve their botnet until two days after Google put the end to (most of) it, Lukas added.
Indicators of Compromise (IoCs)
-
Package name: com.world.hello.myapplication
-
Hash: 34A6BD8B96729B6F87EC5E4110E02BEE1C76F5A9
-
Detection: Trojan.Android/Hiddad.AJN
Finally, the Google has removed the malicious app from the Android Play Store.