Browsing Category
Tutorials
110 posts
The Reliable Solutions To Resolve iPhone Stuck on Apple Logo Issue
Is your iPhone stuck on the Apple logo? Do you fear that you ruined your iPhone? Well, it…
December 12, 2018
Top 7 Hacks – How To Speed Up Your Android?
As much as you use your smartphone over time, it keeps slowing down and the reason behind that…
November 29, 2018
Guest Posting Basics- How To Know If A Website Is Safe?
Are you a blogger that’s looking to reach an audience that’s not typically your own? Have you looked…
November 22, 2018
Pretty Good Privacy (PGP) – A Program That Provides Data Encryption and Decryption
Pretty Good Privacy (PGP) For Data Encryption and Decryption. PGP is a program used for encrypting and decrypting…
November 18, 2018
How To Root Android Devices and Act As Administrator?
To root Android devices – We all love Android, but rooted devices can give you more privileges with…
November 17, 2018
7 Top Common Website Vulnerabilities You Should Know
Top Common Website Security Vulnerabilities and their Bug Bounty Reward. Any bug in a website that can be…
November 5, 2018
8 Top Software Programming For Cybersecurity And Ethical Hackers
Today, the Cyber security needs in the AI world. This article will explore the top 8 software programming…
October 27, 2018
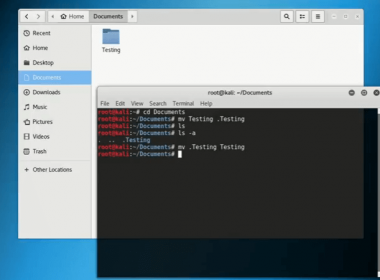
How To Hide Files In Kali Linux?
Hello friends, today we are going to show you, How To Hide Files in Kali Linux? So everyone…
October 21, 2018
IPtables Commands Cheatsheet – For Windows And Linux
Learn IPtables commands For Windows and Linux OS IPtables is a user-space utility program that allows a system…
September 26, 2018
What is Eavesdropping Network Attack?
Eavesdropping on an attack where cybercriminals try to steal your private information and transmitted through unsecured network communication.…
September 11, 2018