Kaushal Jangid
47 posts
Computer enthusiast, VAPT, Security Researcher. Also working with HOC to contribute as security research articles.
BurpSuite Series- Payload Processing Rules – Part 1
Burpsuite Payload Processing Rules WORKING – Today, we are going to overview the Intruder feature “Payload Processing Rule”…
November 30, 2019
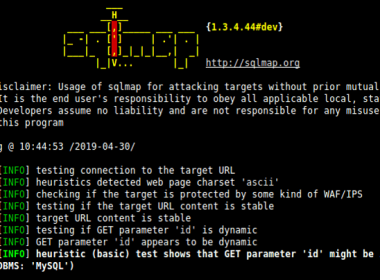
SQL Injection Testing Using SQLMAP
How to test Web application vulnerability SQL injection (SQLi) by using the SQLMAP (a Penetration Testing suite) in…
November 15, 2019
Zenmap- Free Open Source Information Gathering Suite
Today, we are publishing about Zenmap, a Free Open Source Information Gathering software, which is the graphical user…
November 12, 2019
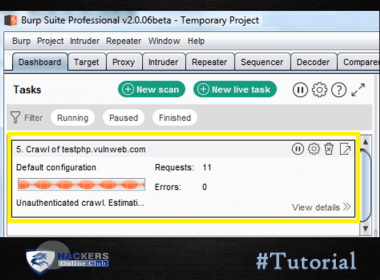
BurpSuite Spider Feature Working
The following tutorial is a beginner guide on the Burpsuite web application spider feature, which is using to…
November 11, 2019
DNSRECON- To Use DNS Information Gathering
Today, we are going to teach you about DNSRECON which is use for DNS Information gathering. It is…
November 7, 2019
Advanced Mobile Forensics Investigation Software 2023
Today, we are going to demonstrate a MOBILedit Forensic Express software for Advanced Mobile Forensics Investigation 2023. So,…
November 5, 2019
Top 10 Digital Forensics Software
Digital Forensics is becoming very important in today’s digital age where many cyber crimes are committed using digital…
November 1, 2019
How To Recover Deleted or Lost Files
The following tutorial about How to Recover Deleted or Lost Files? By using a PhotoRec utility software, it…
October 24, 2019
Burp Suite Series – Demonstrate Runtime File Payload
The following tutorial is a beginner guide on the Burp Suite. In our previous article we are discussing…
October 17, 2019
Exploiting Authentication Issues of Web Application
Following tutorial related to Exploiting Authentication Issues of a Web application. You can also check the POC Video…
October 11, 2019