Sigstore, a new project in the Linux Foundation that aims to solve this issue by improving software supply chain integrity and verification. It improves Software security.
What is Sigstore?
Sigstore will be a free to use non-profit software signing service that harnesses existing technologies of x509 PKI and transparency logs.
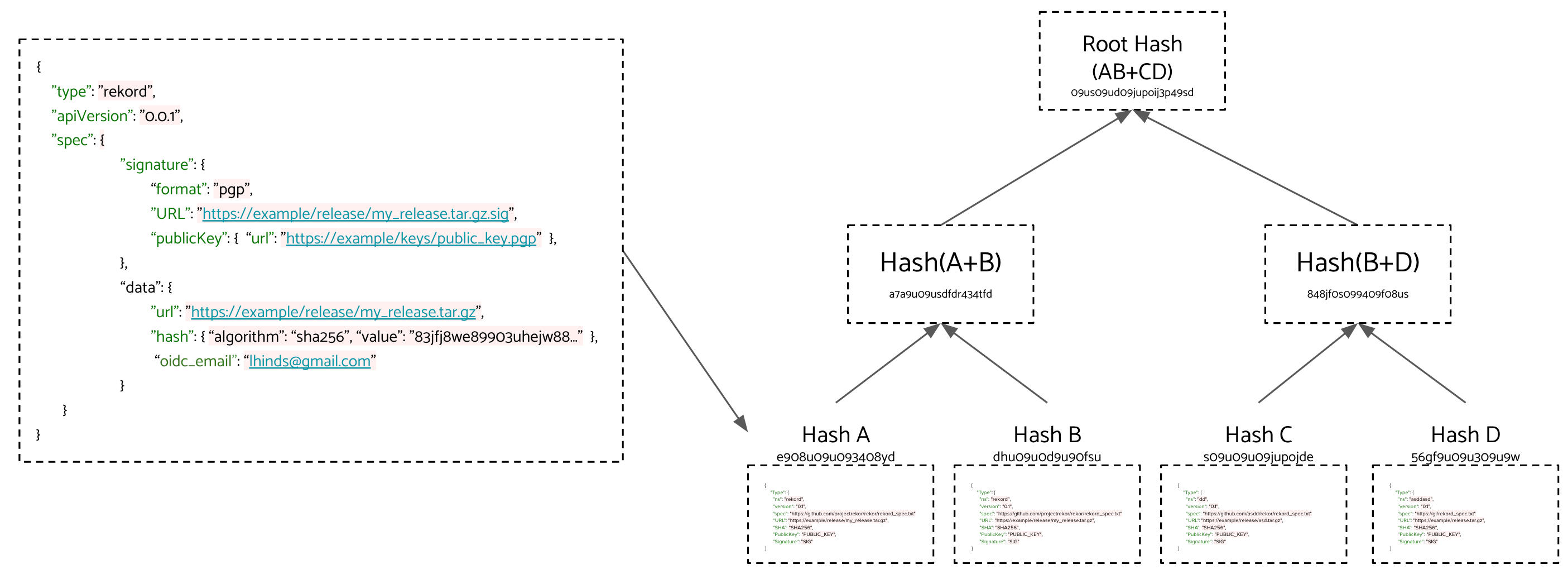
Users generate ephemeral short-lived key pairs using the sigstore client tooling. The sigstore PKI service will then provide a signing certificate generated upon a successful OpenID connect grant. All certificates are recorded into a certificate transparency log and software signing materials are sent to a signature transparency log. The use of transparency logs introduces a trust root to the users OpenID account.
Using OpenID connect identities allows users to take advantage of existing security controls such as 2FA, OTP and hardware token generators.
Sigstore’s transparency logs can act as a source of provenance, integrity, and discoverability. Being public and open anyone can monitor sigstore’s transparency logs for occurrences of their software namespace being used, perform queries using an artifact’s digest, return entries signed by a specific email address, public key, etc.
The mission of sigstore is to make it easy for developers to sign releases and for users to verify them. You can think of it like Let’s Encrypt for Code Signing. Just like how Let’s Encrypt provides free certificates and automation tooling for HTTPS, sigstore provides free certificates and tooling to automate and verify signatures of source code. It also has the added benefit of being backed by transparency logs, which means that all the certificates and attestations are globally visible, discoverable and auditable.
Designed with open source maintainers, for open source maintainers. We understand long-term key management is hard, so we’ve taken a unique approach of issuing short-lived certificates based on OpenID Connect grants. Sigstore also stores all activity in Transparency Logs, backed by Trillian so that we can more easily detect compromises and recover from them when they do occur. Key distribution is notoriously difficult, so we’ve designed away the need for them by building a special Root CA just for code signing, which will be made available for free.
Luke Hinds, one of the lead developers on sigstore and Security Engineering Lead at Red Hat says, “I am very excited about sigstore and what this means for improving the security of software supply chains. Sigstore is an excellent example of an open source community coming together to collaborate and develop a solution to ease the adoption of software signing in a transparent manner.” We couldn’t agree more.
“Securing a software deployment ought to start with making sure we’re running the software we think we are. Sigstore represents a great opportunity to bring more confidence and transparency to the open source software supply chain,” said Josh Aas, executive director, ISRG | Let’s Encrypt.