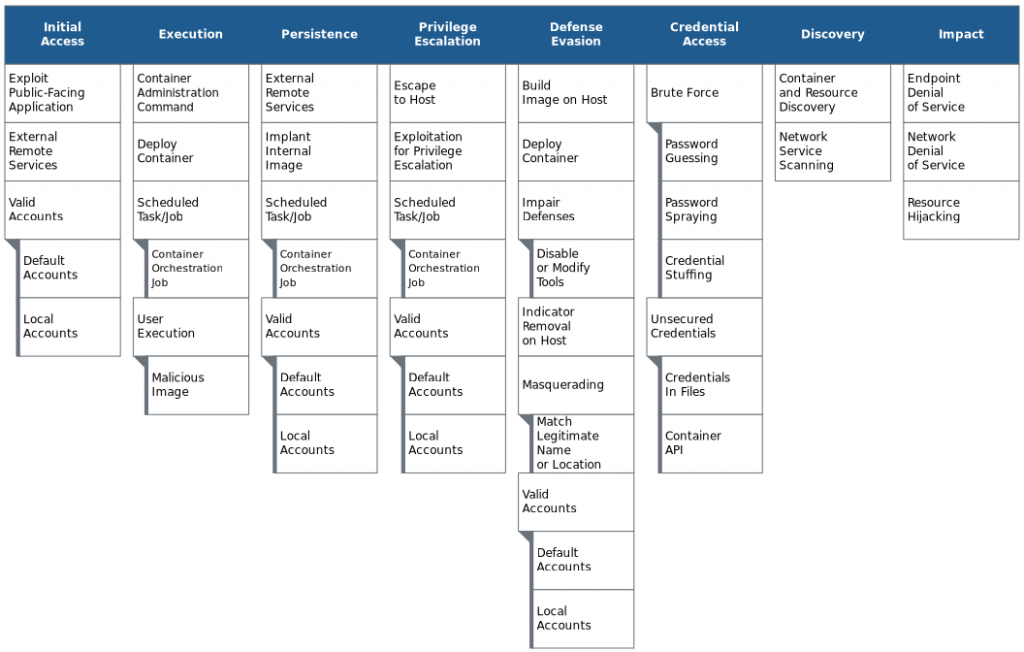
Mitre ATT&CK v9 release updates Techniques, Groups, and Software for Enterprise, Mobile, and ICS. The biggest changes are a change in how we describe data sources, the addition of the Containers and Google Workspace platforms, and the replacement of the AWS, GCP, and Azure platforms with a single IaaS (Infrastructure as a Service) platform.
An accompanying blog post describes these changes and additions in more detail, with a focus on the new structure of data sources.
This ninth version of ATT&CK for Enterprise contains 14 Tactics, 185 Techniques, and 367 Sub-techniques. Check updates here
This release marks the culmination of a Center for Threat-Informed Defense (Center) research project sponsored by Citigroup, JPMorgan Chase, and Microsoft that investigated the viability of adding container-related techniques into ATT&CK.
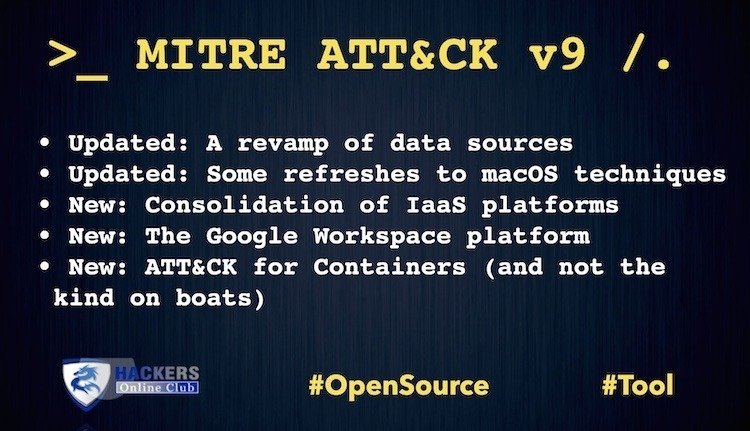
What’s New?
- Updated: A revamp of data sources
- Updated: Some refreshes to macOS techniques
- New: Consolidation of IaaS platforms
- New: The Google Workspace platform
- New: ATT&CK for Containers (and not the kind on boats)
ATT&CK For Containers
The ATT&CK for Containers builds on efforts including the threat matrix for Kubernetes developed by the Azure Security Center team for Azure Defender for Kubernetes. The Center for Threat-Informed Defense expanded on this initial framework by documenting real-world attacks, with Microsoft and other partners providing guidance and feedback throughout the process, said Microsoft.
“Building the ATT&CK for Containers matrix is helpful in understanding the risks associated with containers, including misconfigurations that are often the initial vector for attacks, as well as the specific implementation of attack techniques in the wild. This knowledge informs approaches for detecting threats, and thus helps in providing comprehensive protections, as more and more organizations adopt containers and container orchestration technologies like Kubernetes.”