To Configure Kali Linux on AWS Cloud
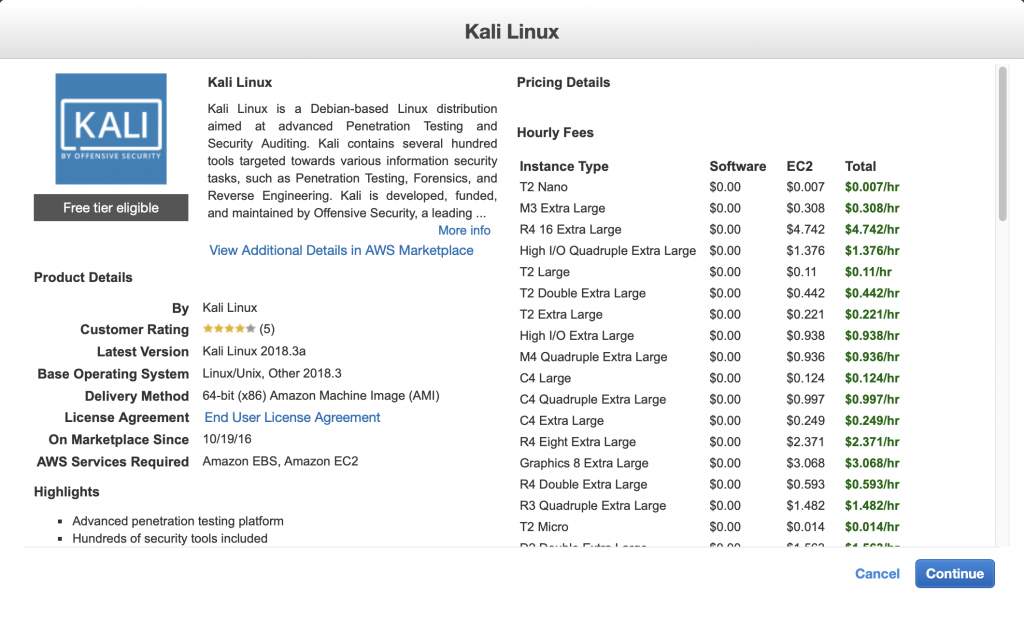
Kali Linux is a Debian-based Linux distribution aimed at advanced Penetration Testing and Security Auditing.
Kali contains several hundred tools targeted towards various information security tasks, such as Penetration Testing, Forensics, and Reverse Engineering.
Kali is developed, funded, and maintained by Offensive Security, a leading information security training company.
What is AWS (Amazon Web Services)
AWS is a subsidiary of Amazon.com that provides on-demand cloud computing platforms to individuals, companies and governments, on a paid subscription basis. The technology allows subscribers to have at their disposal a virtual cluster of computers, available all the time, through the Internet.
AWS Infrastructure
AWS Support is a one-on-one support channel that is staffed 24x7x365 with experienced support engineers. AWS Support offers four support plans: Basic, Developer, Business, and Enterprise. The Basic plan is free of charge and offers support for account and billing questions and service limit increases. The other plans offer an unlimited number of technical support cases with pay-by-the-month pricing and no long-term contracts, providing the level of support that meets your needs.
Kali Linux is user friendly operating system for Cyber Security experts. Kali linux is listed in Amazon EC2 Marketplace too. The good thing is, it is eligible for Free.
Requirement
1. Amazon (AWS) account.
2. 2GB of RAM, a condition if you want to run Metasploit as well.
Steps to follow-
First you need to require an Amazon Web Server (AWS) account https://aws.amazon.com
Provide your billing information, select your Free Tier for a limited time. You will get more detail about AWS free Tier here.
After Amazon Verification, you will select the plan and move forward to next step.
Navigate to Web Services dashboard as shown in the following screenshot. Go to EC2 Launch Instance:
Now you will need Amazon Machine Image (AMI)
An AMI is a template that contains the software configuration including operating system, application server required to launch your instance.
Now go to your AWS Marketplace and search Kali Linux instance. Select > Continue.
Now as per the following figure you need to select an instance type. Here t1.micro and t2.micro will be eligible for free tier. And if you want to run Metasploit then select the option t2.small or t2.medim according to your budget.
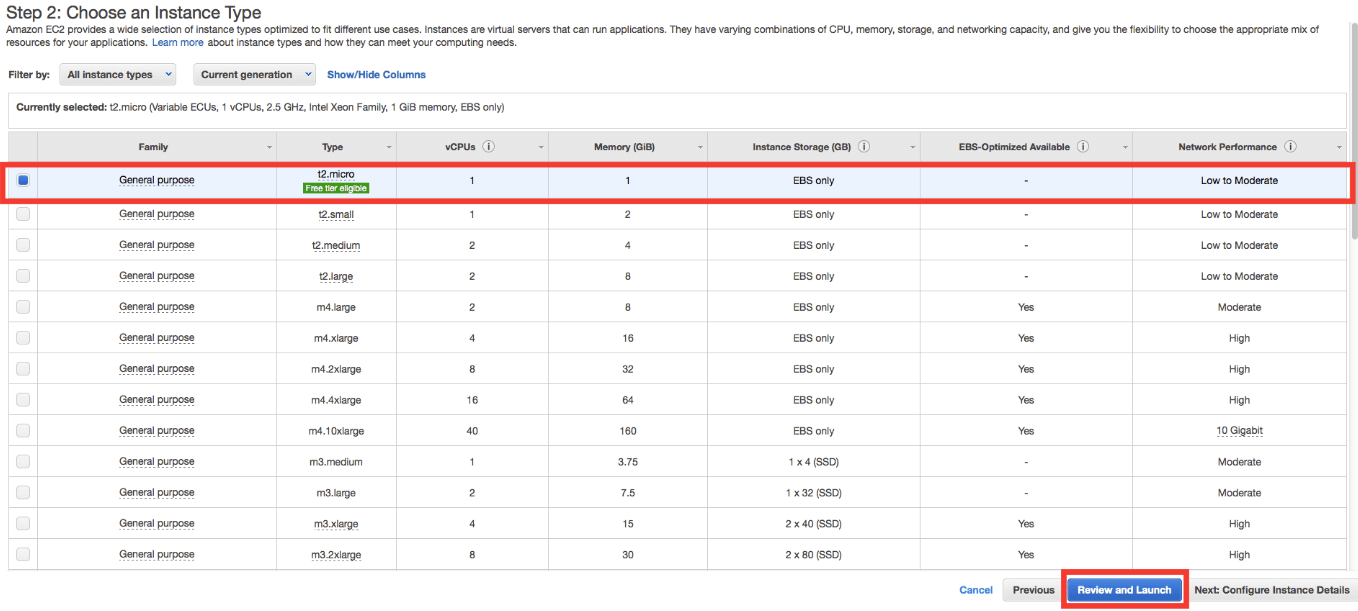
Click on ‘Review and Launch’. After that you will get popup window asking for Boot from general Purpose (SSD). Select “Make General purpose (SSD) the default volume for all instance launches from the console going forward”. > Click Next.
Here you reach directly at Step 7 with Warning “Improve your instance Security”. Here select the option 6 “Configure Security Group” on AWS console.
In the source section , select ‘My IP’. It will automatically detect your public IP range. Click on Review and Launch. If you have dynamic IP than you will need to login back to AWS console and allow your dynamic IP updated address.
If you have selected m2.medium than you are not eligible for free tier usage in 2GB RAM.
Now you will need SSH Key pairs to access Kali Linux from your host computers.
To generate your keys, go to Amazon AWS console, under the network and Security navigation click on Key pairs, > Select on ‘Create Key Pair’ option and give ‘Key pair name’.
The private key will be downloaded, and make sure to keep it secure. if you will lost the keys then you will not be able to generate it again.
Once you downloaded Key pair, click on ‘Launch Instances’.
Confirm your region before proceeding with instance. You can confirm the region from your AWS console account as shown in figure.
Now click on Launch with ‘1click’ button to configure.
Kali Linux configuration in AWS cloud has been successfully completed.