MVT is a mobile forensics software to look for signs of infection in smartphone devices.
The Amnesty International Security Lab is also releasing an open-source suite, the Mobile Verification Toolkit (MVT). MVT can be used to check a devices for potential signs of compromise with Pegasus spyware.
Also Read: What is Pegasus Spyware? How it Can Hack Android and iPhone?
Mobile Verification Toolkit (MVT) is a collection of utilities to simplify and automate the process of gathering forensic traces helpful to identify a potential compromise of Android and iOS devices.
It has been developed and released by the Amnesty International Security Lab in July 2021 in the context of the Pegasus project along with a technical forensic methodology and forensic evidence.
Mobile Verification Toolkit (MVT) is a collection of utilities designed to facilitate the consensual forensic acquisition of iOS and Android devices for the purpose of identifying any signs of compromise.
MVT’s capabilities are continuously evolving, but some of its key features include:
- Decrypt encrypted iOS backups.
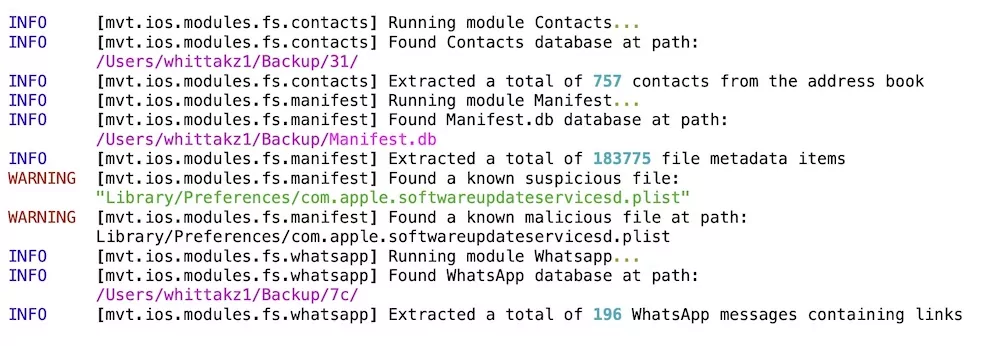
- Process and parse records from numerous iOS system and apps databases, logs and system analytics.
- Extract installed applications from Android devices.
- Extract diagnostic information from Android devices through the adb protocol.
- Compare extracted records to a provided list of malicious indicators in STIX2 format.
- Generate JSON logs of extracted records, and separate JSON logs of all detected malicious traces.
- Generate a unified chronological timeline of extracted records, along with a timeline all detected malicious traces.
Consensual Forensics
While MVT mobile forensics is capable of extracting and processing various types of very personal records typically found on a mobile phone (such as calls history, SMS and WhatsApp messages, etc.), this is intended to help identify potential attack vectors such as malicious SMS messages leading to exploitation.
Warning: MVT is a mobile forensics research tool intended for technologists and investigators. Using it requires understanding the basics of forensic analysis and using command-line tools. This is not intended for end-user self-assessment. If you are concerned with the security of your device please seek expert assistance.
How To Detect?
According to Techcrunch report, MVT will let you take an entire iPhone backup (or a full system dump if you jailbreak your phone) and feed in for any indicators of compromise (IOCs) known to be used by NSO to deliver Pegasus, such as domain names used in NSO’s infrastructure that might be sent by text message or email. If you have an encrypted iPhone backup, you can also use MVT to decrypt your backup without having to make a whole new copy.
MVT Mobile Forensics Installation
MVT can be installed from sources or conveniently using:
pip3 install mvt
You will need some dependencies, so please check the documentation.
Before proceeding, please note that mvt requires Python 3.6+ to run. While it should be available on most operating systems, please make sure of that before proceeding.
Dependencies on Linux
First install some basic dependencies that will be necessary to build all required tools:
sudo apt install python3 python3-pip libusb-1.0-0
libusb-1.0-0 is not required if you intend to only use mvt-ios and not mvt-android.
Dependencies on Mac
Running MVT on Mac requires Xcode and homebrew to be installed.
In order to install dependencies use:
brew install python3 libusb
libusb is not required if you intend to only use mvt-ios and not mvt-android.
Installing MVT
If you haven’t done so, you can add this to your .bashrc or .zshrc file in order to add locally installed Pypi binaries to your $PATH:
export PATH=$PATH:~/.local/bin
Then you can install MVT directly from pypi
pip install mvt
Or from the source code:
git clone https://github.com/mvt-project/mvt.git cd mvt pip3 install
You now should have the mvt-ios and mvt-android utilities installed.
Alternatively, you can decide to run MVT and all relevant tools through a Docker container.
Usage
MVT provides two commands mvt-ios and mvt-android with the following subcommands available:
mvt-ios:
- check-backup: Extract artifacts from an iTunes backup
- check-fs: Extract artifacts from a full filesystem dump
- check-iocs: Compare stored JSON results to provided indicators
- decrypt-backup: Decrypt an encrypted iTunes backup
mvt-android:
- check-backup: Check an Android Backup
- download-apks: Download all or non-safelisted installed APKs
Check out the documentation to see how to use them.
License
The purpose of MVT is to facilitate the consensual forensic analysis of devices of those who might be targets of sophisticated mobile spyware attacks, especially members of civil society and marginalized communities. We do not want MVT to enable privacy violations of non-consenting individuals. Therefore, the goal of this license is to prohibit the use of MVT (and any other software licensed the same) for the purpose of adversarial forensics.
In order to achieve this, MVT is released under an adaptation of Mozilla Public License v2.0. This modified license includes a new clause 3.0, “Consensual Use Restriction” which permits the use of the licensed software (and any “Larger Work” derived from it) exclusively with the explicit consent of the person/s whose data is being extracted and/or analysed (“Data Owner”).