A New Threat Emerges: Visual Studio Code as an Attack Vector
In a recent cyber threat development, hackers have found a novel way to exploit a legitimate feature of Visual Studio Code (VS Code), a popular code editor, to gain unauthorized remote access to systems and potentially steal sensitive data.
A recent cyber espionage campaign, Operation Digital Eye, highlights a growing sophistication in state-sponsored cyber threat.
Researchers from SentinelOne uncovered the campaign, attributed to a Chinese Advanced Persistent Threat (APT) group, targeting critical IT infrastructure in Southern Europe. The attackers used unconventional methods, making detection and mitigation particularly challenging.
Key Techniques
Cloud Infrastructure Misuse: By integrating with platforms like Microsoft Azure, the attackers disguised their activities, blending malicious traffic with legitimate operations.
Abuse of Visual Studio Code (VS Code) Tunnels: The attackers exploited VS Code’s built-in tunneling feature. This capability, signed by Microsoft and often used legitimately by developers, was weaponized to establish encrypted communication channels for command and control (C2) operations.
SQL Injection and Credential Exploitation: The campaign began with SQL injection attacks to infiltrate systems. They then leveraged pass-the-hash techniques to move laterally within compromised networks.
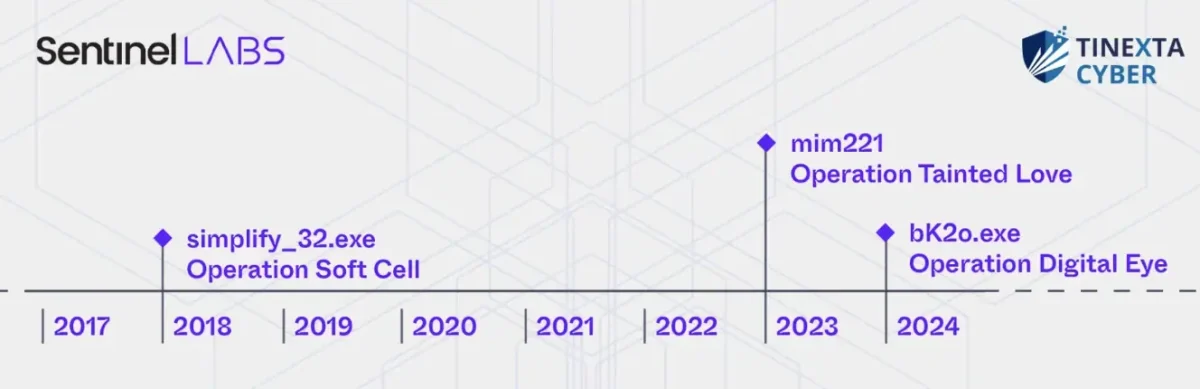
The threat actors used a pass-the-hash capability, likely originating from the same source as closed-source custom Mimikatz modifications observed exclusively in suspected Chinese cyberespionage activities, such as Operation Soft Cell and Operation Tainted Love. The malware and tooling used in these campaigns have been linked to several distinct Chinese APT groups. We collectively refer to these custom Mimikatz modifications as mimCN, Sentinal added.
How the Attack Works:
The attackers leverage VS Code’s Remote Development feature, designed to allow developers to work on codebases hosted on remote machines. By crafting malicious extensions or tricking users into installing compromised extensions, hackers can gain access to the victim’s system.
Once installed, the malicious extension can execute arbitrary code on the target machine, enabling attackers to:
- Steal sensitive data: Access and exfiltrate confidential information, including source code, credentials, and proprietary data.
- Deploy malware: Install additional malicious software to further compromise the system.
- Establish persistent backdoors: Gain long-term access to the system for future attacks.
Impact and Risk
Challenges in Detection: By leveraging tools like VS Code and cloud services, the attackers bypassed traditional monitoring mechanisms. The use of legitimate tools signed by trusted vendors further complicated detection.
Target Scope: The primary victims were business-to-business IT service providers, a strategic move that risks cascading impacts across interconnected systems.
Defensive Recommendations
- Monitor unusual usage of developer tools like VS Code in non-standard contexts.
- Employ deep packet inspection to identify encrypted C2 traffic.
- Harden supply chain cybersecurity, as attackers increasingly target service providers.
Mitigation Strategies:
To protect against this emerging threat, individuals and organizations are advised to take the following precautions:
- Exercise caution with extensions: Only install extensions from trusted sources and carefully review their permissions.
- Keep VS Code and extensions updated: Regularly update the software and extensions to address security vulnerabilities.
- Use strong, unique passwords: Employ strong, unique passwords for all accounts, including those used for VS Code and remote development.
- Enable two-factor authentication (2FA): Add an extra layer of security to your accounts.
- Be wary of phishing attacks: Avoid clicking on suspicious links or downloading attachments from unknown sources.
- Implement robust network security: Employ firewalls, intrusion detection systems, and other security measures to protect your network.
- Stay informed about the latest threats: Keep up-to-date on the latest cyber threats and vulnerabilities.
This campaign serves as a wake-up call for businesses to bolster defenses against state-sponsored threats employing novel and hard-to-detect tactics.
By adopting these measures, users can significantly reduce the risk of falling victim to this new attack vector. As the threat landscape continues to evolve, it is essential to remain vigilant and adapt security practices accordingly.