Browsing Category
Tutorials
110 posts
What is Endpoint Security?
How does Endpoint Security work? Endpoint Protection: Why It’s Important Today’s AI age, companies must protect their systems…
April 15, 2023
IPv4 vs IPv6: Understanding the Internet’s Addressing Evolution
The internet, as we know it, relies on IP addresses to connect devices. But with the explosion of…
April 15, 2023
What is Cloud Computing? Explain
The cloud computing revolution has revolutionized how individuals and organizations store, process, and share data. The use of…
April 3, 2023
What is A Side-Channel Attack?
Side-channel attack or side-stepping attacks occur when hackers use information from outside sources to access a system or…
March 2, 2023
Nexpose A Vulnerability Management Software
Nexpose is a vulnerability management software solution developed by Rapid7. It helps companies identify, assess, and prioritize vulnerabilities…
December 14, 2022
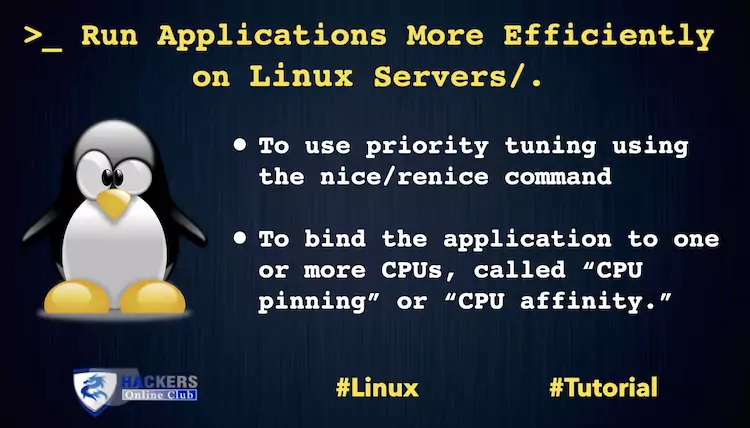
How To Run Applications More Efficiently on Linux Server
[ Editor’s note: There are known limitations to CPU pinning in some environments, so be sure to read…
July 19, 2021
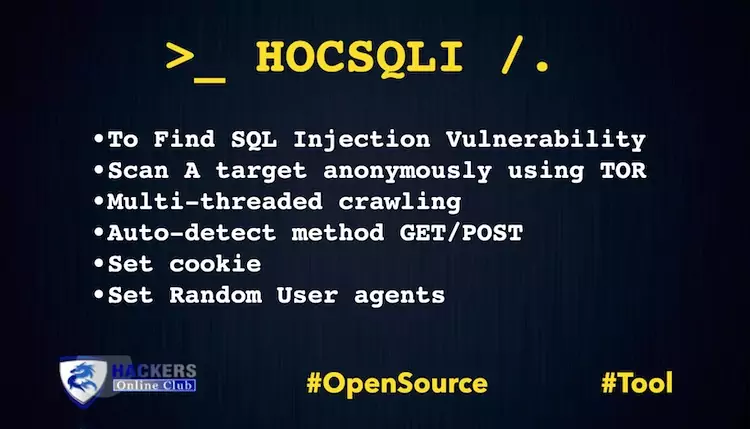
HOCSQLI Automatic SQL Injection Vulnerability Scanner
Today, we are presenting our own Cyber Intelligence suite HOCSQLI. An Automatic (SQL Injection) vulnerability scanner along with…
May 4, 2021
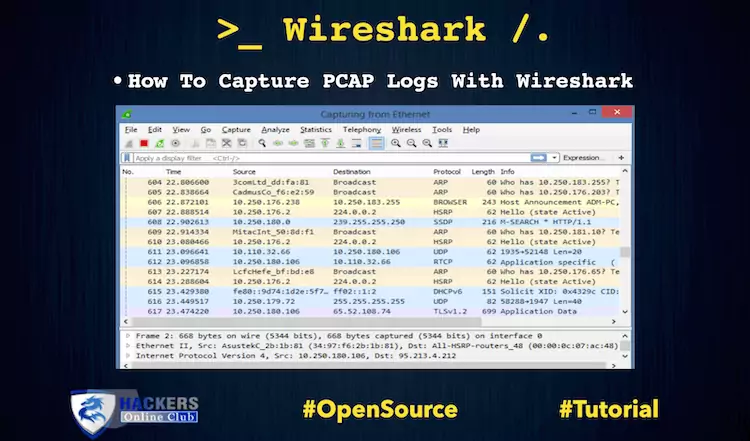
How To Capture PCAP Logs With Wireshark
Today, we are working to capture the PCAP LOGS with the help of Wireshark. Organization following logs are…
October 22, 2020
Metasploit Tutorial – How To Write Auxiliary Module?
Metasploit Tutorial Auxiliary module Metasploit is known for its free, open-source exploits – modules that pop shells. But…
July 30, 2020
RecoX: Scripts For Web Application Reconnaissance
RecoX, an open source software a collection of master scripts for Web Application Scanning. The script aims to…
June 12, 2020