RecoX, an open source software a collection of master scripts for Web Application Scanning.
The script aims to help in classifying vulnerabilities in web applications. The methodology RecoX is arising can spot weaknesses other than OWASP top ten. The script presents information against the target system. It gathers the information recursively over each subdomain, and IP address for a sophisticated attack.
RecoX automates several functions and saves a significant amount of time that requires throughout a manual penetration test.
Usage
git clone https://github.com/samhaxr/recox chmod +x recox.sh ./recox.sh
Paste the below command to run the tool from anywhere in the terminal.
mv recox.sh /usr/local/bin/recox
The deep scanner comprises many check-ups including subdomain takeover, A record, passive scan, active scan, CORS misconfiguration, zone transfer test, and web content discovery.
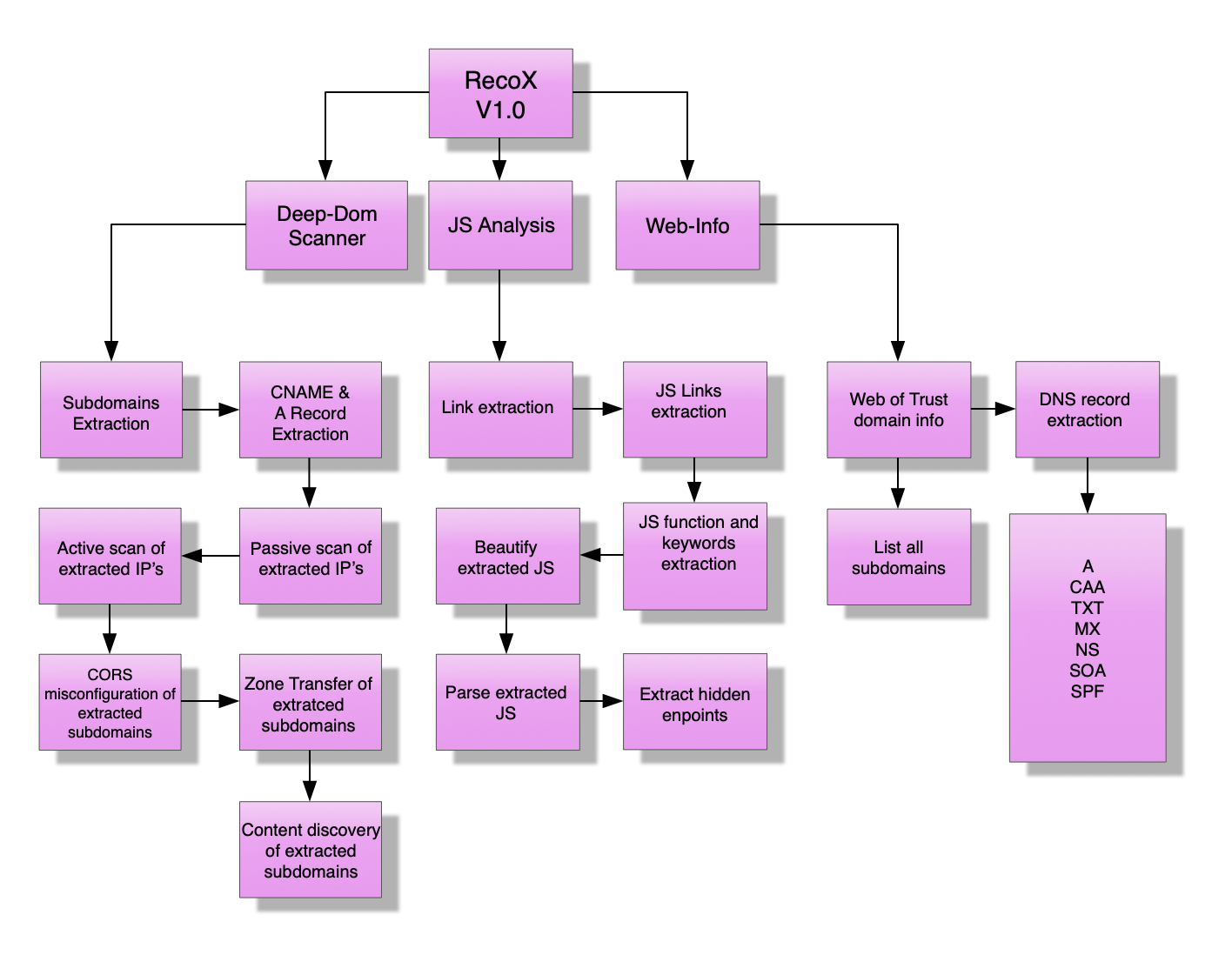
Deep-Dom Scanner
The deep scanner comprises many check-ups including subdomain takeover, A record, passive scan, active scan, CORS misconfiguration, zone transfer test, and web content discovery.
Subdomain Takeover
The subdomain takeover is a process in which a subdomain points to an external non-existing domain where attacker registers the non-existing domain to take over the subdomain. The DNS misconfiguration enables an attacker to gain full authority across subdomains leading to providers such as Heroku, Github, Bitbucket. The web becomes vulnerable if DNS entries pointed to an external service provider and are not in use.
The misconfiguration enables unverified users to claim the non-existing subdomain from an external service provider in order to serve content for personal and financial gain (Detectify Labs, 2014).
RecoX obtains all subdomains related to the main domain by using the VirusTotal API (Application Programming Interface). The script starts extracting CNAME record for each subdomain to check which external service the subdomain is pointing. It displays all the CNAME record for each subdomain and then asks is user want to check against subdomain takeover vulnerability
Passive Scan
Passive scanning is a process of detecting vulnerability which relies on the available information without direct interaction. The main advantage of passive scanning is that it does not leave a trail that could alert the admin to their activities (Rouse, 2017).
Shodan services have captured all the information for online devices and gathering information from Shodan is a passive scanning. The RecoX script uses Shodan API in order to obtain the relevant information related to the target.
The script uses those obtained IP addresses from the previous function and runs Shodan IP scan recursively against each IP address in order to expose the vulnerability in ports. The disadvantage of passive scanning is that some information may be false because the information might be changed and can be revealed in active scanning.
Active Scan
Active scanning detects services by sending packets to host, which mean this process is directly interacting with the target host. Active scanning gains all services and ports data where the host is running programs. The result can be affected by firewalls or other countermeasures by the host.
The result may be generic because of the scanning specific only to the protocol, not the application (Bartlett et al., n.d.).
The RecoX script performs the same recursive function it uses in passive scanning to discover the live record. The active scanning process directly interacts with the target host and retrieve the information, which may be different from the passive scan.
For example, the ports are closed shown in the passive scan, but active scanning shows that different ports are open. It is because it interacts directly to the target host and obtains current information from the target host.
The RecoX script uses Nmap to perform an active scan. The script operates recursively against the obtained IP addresses. While scanning the target host if it discovers the open web ports, then script tries to find the fingerprint to check how the web application is responding to each query.
CORS Misconfiguration
The JavaScript, which is running on one domain, can only read the data from much domain. If restrictions are not correctly in place, a small snippet of JavaScript can open another taband steal all the credentials, including chats and other personal information.
That is why the JavaScript must allow sending a request and read the data from the domain where the original request originates. It is possible to write the JavaScript code in order to avoid such mistakes. The JavaScript should request to the domain it is hosted on to read thedata. However, most API works this way. The JavaScript process the data instead of straight displaying it on the web page.
The RecoX script runs another python script by Jensvoid is based on James Kettle research. The script downloads a copy of python based CORS test script and runs against each subdomain. It then scans each subdomain and checks it against Access Control Allow Origin header and Access Control Allow Credential.
It will highlight those subdomains in red where Access Control Allow Credential is true. The domain may not be vulnerable if the header Access Control Allow Origin has no wildcard value.
The Deep JS Analysis function comprises of many check-ups which involve the extraction of source link and parameters inside the webpage. The script attempts to obtain the dot JS extension within the web page and pluck all of them and display in the terminal output so the tester can examine each of them for in-depth analysis.
There are two types of analysis.
• Static analysis (SAST)
• Dynamic analysis (DAST)
Static analysis finds vulnerabilities that dynamic analysis mises. It is because it can find the snippet that needs to execute in the appropriate circumstances. Static analysis results are false-positive and noisy because it seems some codes are executable when, in fact, they are not. It is because it does not understand the custom data validation logic.
Dynamic analysis has different aspects than static analysis. It is not noisy and does not have a false-positive result. It is because it processes suitable data from source to sink during execution. However, it may result in false-positive in a situation where injected data does not reach the destination (Dafydd Stuttard, 2018).
New Features
The new features include the testing of cloud security. There will be more functions in the next version of RecoX script. Those functions run recursively against the target domain. The new feature for the next version is ASN discovery and running a passive and active scan against each block of IP.
An Autonomous System Number (ASN) is a collection of one or more IP designations driven by one or more network administrators that manage a single and clear routing policy. Network administrators need ASNs to control routing within their networks and to switch routing data beside other Internet Service Providers (ISPs) (Arin.net, 2020).
The new feature obtains the ASN number form the target domain and extracts each block of IP within the ASNs. It then runs passive and active scan recursively against the block of IPs.