Background and Evolution
BloodAlchemy is identified as an evolved form of Deed RAT, which in turn is a successor of the infamous ShadowPad malware. ShadowPad first appeared in a 2017 supply chain attack and has been associated with various APT groups, including APT41, a research by ITOCHU Cyber Intelligence.
Deed RAT, used by the Space Pirates group, shares significant code similarities with ShadowPad. BloodAlchemy inherits these characteristics, suggesting ongoing development and adaptation by threat actors.
Infection and Mechanism
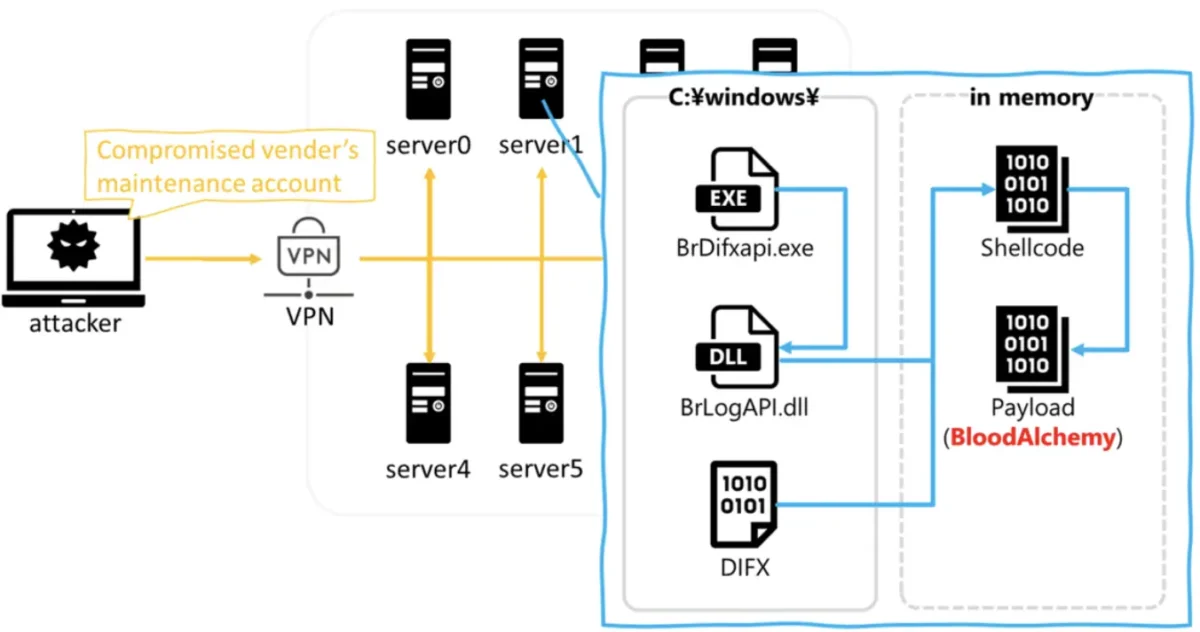
BloodAlchemy’s infection vector typically involves exploiting a maintenance account on VPN devices, deploying a malicious file set (BrDifxapi.exe, BrLogAPI.dll, DIFX). The execution process uses DLL side-loading to inject shellcode, decrypting and loading the main payload into memory without leaving a significant trace on disk, making it difficult to detect.
Technical Analysis
Malicious DLL and Shellcode:
- Uses AES128 for initial decryption.
- Custom decryption based on FNV-1a hash and lznt1 compression.
Payload Structure:
- Unique format resembling PE but custom-structured for specific functionalities.
- Run modes dictate behavior, ranging from communication with C2 servers to persistence and process injection.
Persistence and Evasion:
- Employs various persistence methods (services, startup entries, scheduled tasks).
- Anti-sandbox techniques and process injection (e.g., Early Bird Injection) to avoid detection.
Communication and Backdoor Commands:
- Up to 10 C2 servers supported.
- 15 backdoor commands for diverse control functions (e.g., updating configurations, launching processes).
Code Similarities and Implications
BloodAlchemy shows significant code similarities with Deed RAT in payload structures, exception handling, plugin management, and configuration encryption. This suggests it is a direct evolution, likely developed by the same or closely collaborating threat actors.
The increasing complexity and evolution of this malware show that these cyber attack groups are a constant threat. This means we need better ways to detect and defend against them.