An unpatched VMware Horizon server have been compromised by Iranian hackers exploiting the Log4Shell vulnerability.
According to U.S Cybersecurity and Infrastructure Security Agency (CISA), relate to incident response efforts undertaken by the authority between the midpoints of June and July of this year.
In February 2022, the cyber threat actors exploited Log4Shell for initial access to the organisation’s unpatched VMware Horizon server.
The Joint advisory statement released, From mid-June through mid-July 2022, CISA conducted an incident response engagement at a Federal Civilian Executive Branch (FCEB) organisation where CISA observed suspected advanced persistent threat (APT) activity.
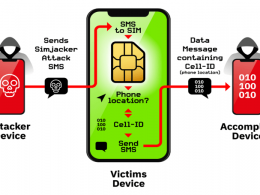
In the course of incident response activities, CISA determined that cyber threat actors exploited the Log4Shell vulnerability in an unpatched VMware Horizon server, installed XMRig crypto mining software, moved laterally to the domain controller (DC), compromised credentials, and then implanted Ngrok reverse proxies on several hosts to maintain persistence. CISA and the Federal Bureau of Investigation (FBI) assess that the FCEB network was compromised by Iranian government-sponsored APT actors.
By remotely exploiting Log4Shell allows attackers to move across breached networks to access internal systems with sensitive data stored on local or Internet-accessible servers.
CISA and FBI are releasing this Cybersecurity Advisory (CSA) providing the suspected Iranian government-sponsored actors’ tactics, techniques, and procedures (TTPs) and indicators of compromise (IOCs) to help network defenders detect and protect against related compromises.
CISA and FBI encourage all organizations with affected VMware systems that did not immediately apply available patches or workarounds to assume compromise and initiate threat hunting activities. If suspected initial access or compromise is detected based on IOCs or TTPs described in this CSA, CISA and FBI encourage organizations to assume lateral movement by threat actors, investigate connected systems (including the DC), and audit privileged accounts.
All organisations, regardless of identified evidence of compromise, should apply the recommendations in the Mitigations section of this CSA to protect against similar malicious cyber activity.
Recommend Advisory
- Install updated builds to ensure affected VMware Horizon and UAG systems are updated to the latest version.
- Keep all software up to date and prioritize patching known exploited vulnerabilities (KEVs).
- Minimise the internet-facing attack surface by hosting essential services on a segregated DMZ.
- Use best practices for identity and access management (IAM).
- Audit domain controllers to log successful Kerberos Ticket Granting Service (TGS) requests and ensure the events are monitored for anomalous activity.
- Secure accounts.
– Enforce the principle of least privilege. Administrator accounts should have the minimum permission necessary to complete their tasks.
– Ensure there are unique and distinct administrative accounts for each set of administrative tasks.
– Create non-privileged accounts for privileged users and ensure they use the non-privileged accounts for all non-privileged access (e.g., web browsing, email access).
– Create a deny list of known compromised credentials and prevent users from using known-compromised passwords.
Also See –