Infection Monkey- Open Source Data center Security Testing platform
The Infection Monkey is an open source security suite for testing a data center’s resiliency to perimeter breaches and internal server infection. The Monkey uses various methods to self propagate across a data center and reports success to a centralized Monkey Island server.
The Infection Monkey is comprised of two parts:
- Monkey – A platform which infects other machines and propagates to them.
- Monkey Island – A dedicated server to control and visualize the Infection Monkey’s progress inside the data center.
Main Features
The Infection Monkey uses the following techniques and exploits to propagate to other machines.
Multiple propagation techniques:
- Predefined passwords
- Common logical exploits
- Password stealing using Mimikatz
Multiple exploit methods:
- SSH
- SMB
- WMI
- Shellshock
- Conficker
- SambaCry
- Elastic Search (CVE-2015-1427)
- Weblogic server
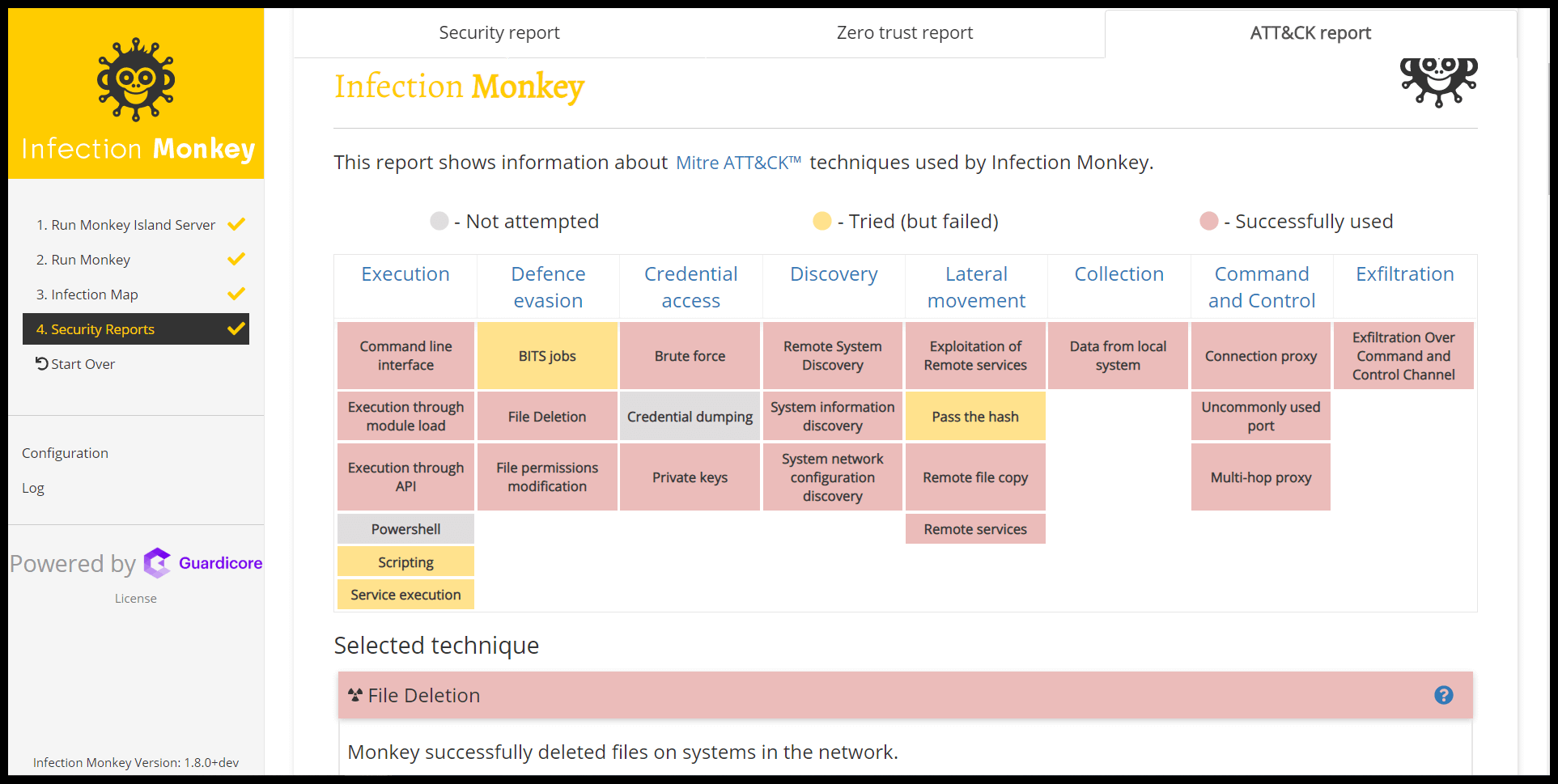
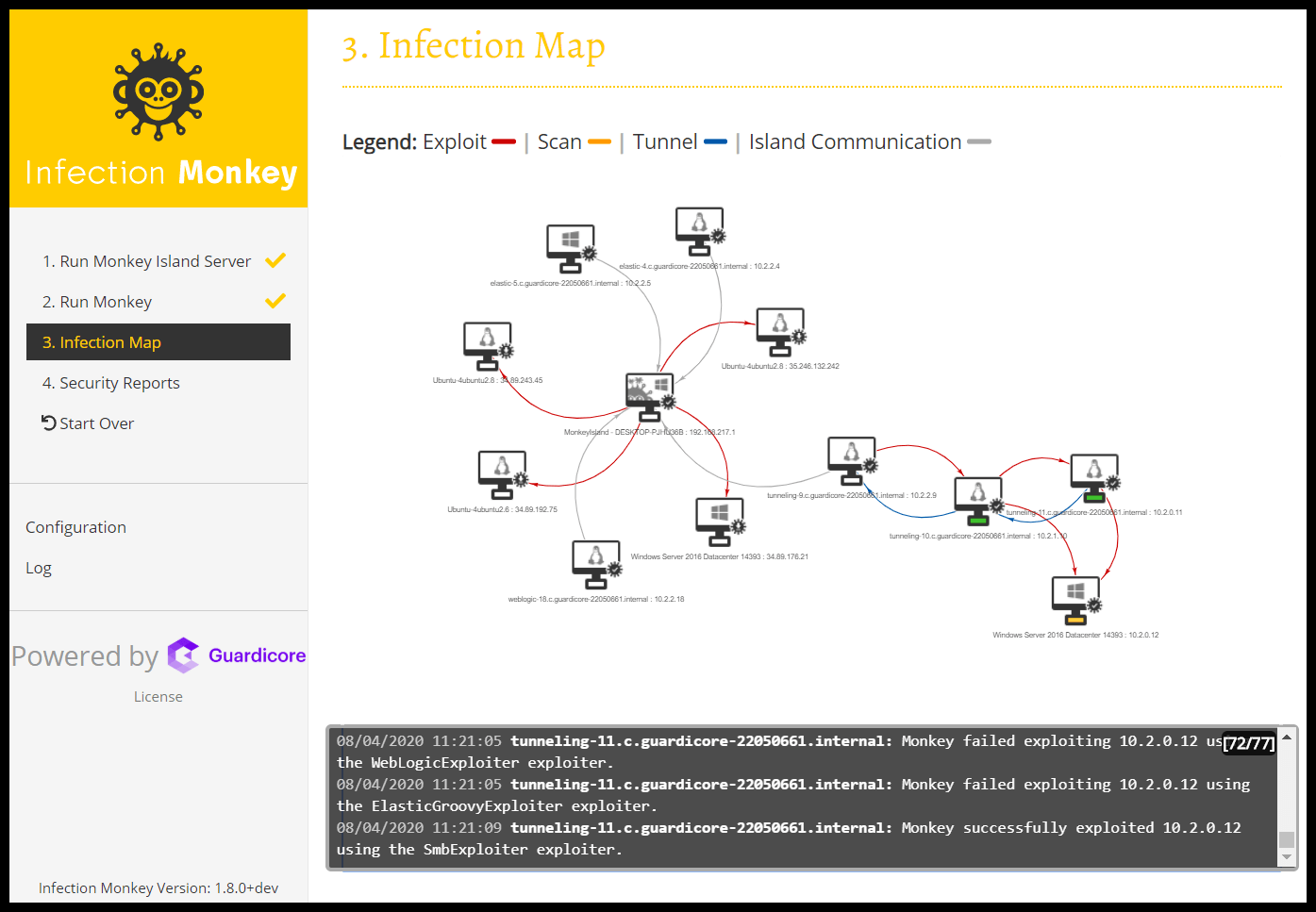
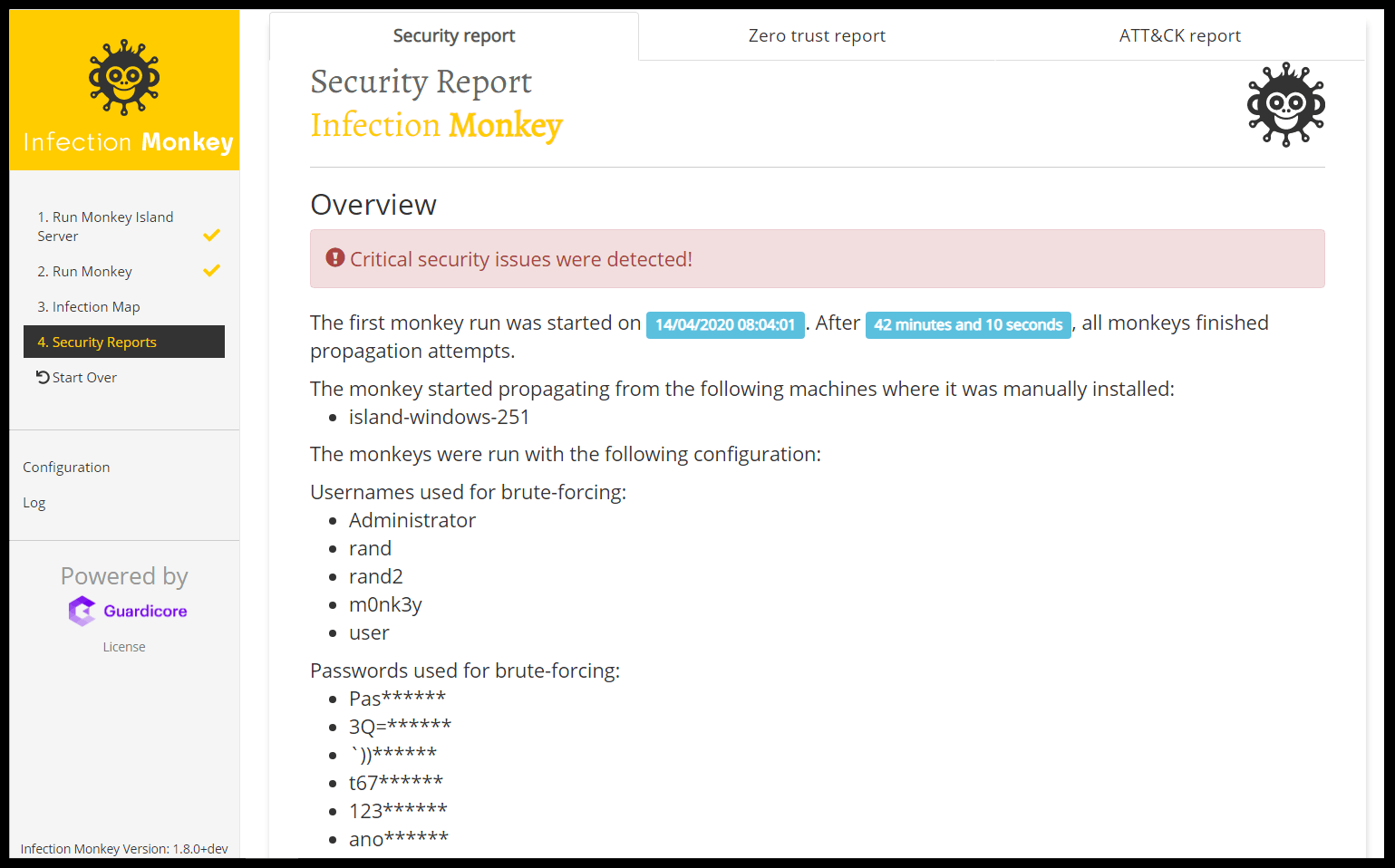
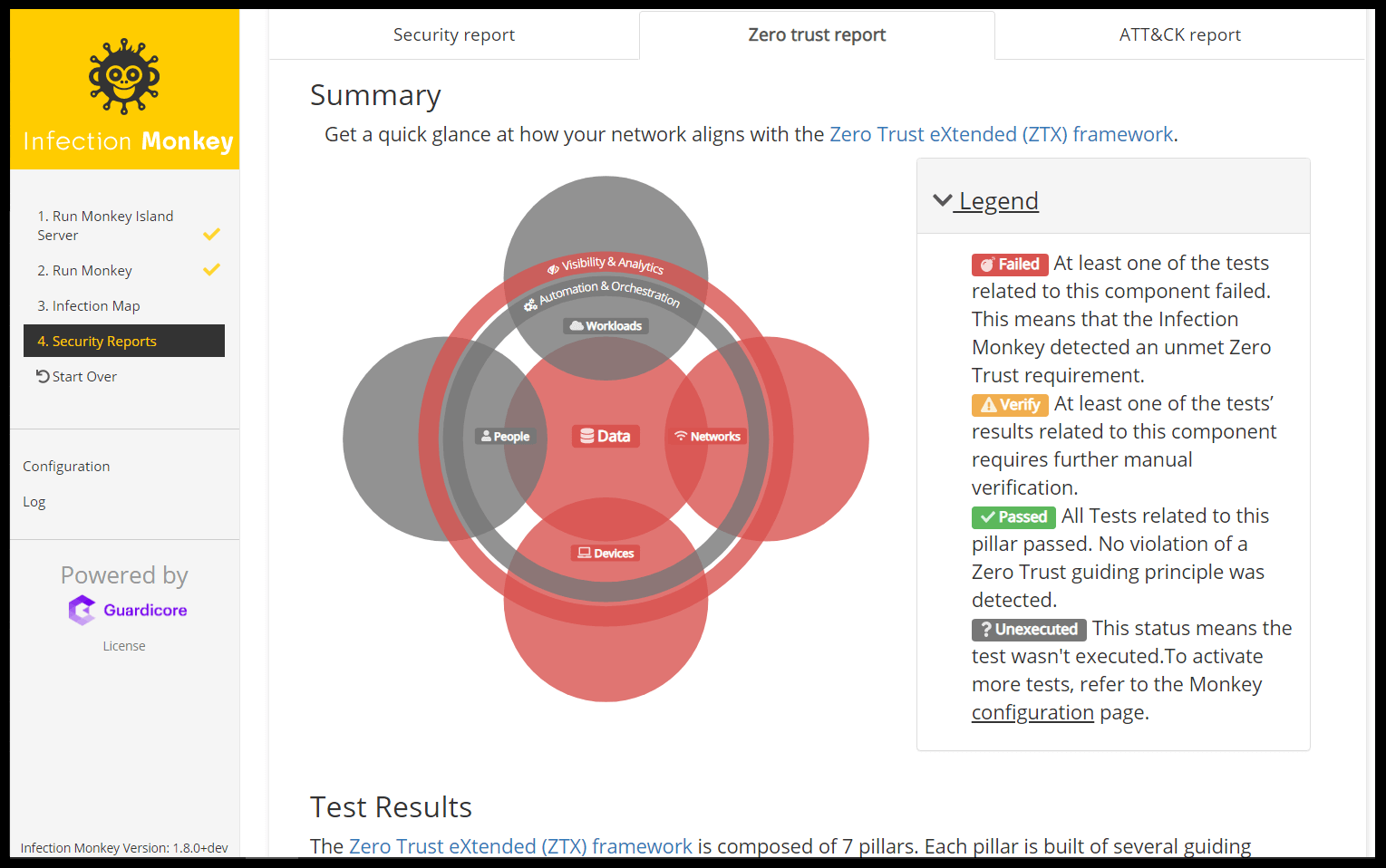
Screenshots
How To Setup?
Setup documentation here
Unit Tests
In order to run all of the Unit Tests, run the command python -m pytest in the monkey directory.
To get a coverage report, first make sure the coverage package is installed using pip install coverage.
Run the command coverage run -m unittest in the monkey directory and then coverage html. The coverage report can be found in htmlcov.index.
Blackbox tests
In order to run the Blackbox tests, refer to envs/monkey_zoo/blackbox/README.md
Monkey Operating System Supports
The Monkey itself (the agent) has been tested to run on the following operating systems (on x64 architecture)
Linux
Compatibility depends on GLIBC version (2.14+)1. By default these distributions are supported:
- Centos 7+
- Debian 7+
- Kali 2019+
- Oracle 7+
- Rhel 7+
- Suse 12+
- Ubuntu 14+
Windows
- Windows 2012+
- Windows 2012_R2+
- Windows 7/Server 2008_R2 if KB2999226 is installed.
- Windows vista/Server 2008 should also work if the same update is installed, but this wasn’t tested.
Island support
The Monkey Island (control server) runs out of the box on:
- Ubuntu 18.04
- Debian 9
- Windows Server 2012
- Windows Server 2012 R2
- Windows Server 2016
Scanners
The Infection Monkey agent has two steps before attempting to exploit a victim, scanning and fingerprinting, it’s possible to customize both steps in the configuration files.
Scanning
Currently there are two scanners, PingScanner and TcpScanner both inheriting from HostScanner.
The sole interface required is the is_host_alive interface, which needs to return True/False.
TcpScanner is the default scanner and it checks for open ports based on the tcp_target_ports configuration setting.
PingScanner sends a ping message using the host OS utility ping.
Fingerprinting
Fingerprinters are modules that collect server information from a specific victim. They inherit from the HostFinger class and are listed under finger_classes configuration option.
Currently implemented Fingerprint modules are:
- SMBFinger – Fingerprints target machines over SMB. Extracts computer name and OS version.
- SSHFinger – Fingerprints target machines over SSH (port 22). Extracts the computer version and SSH banner.
- PingScanner – Fingerprints using the machines TTL, to differentiate between Linux and Windows hosts.
- HTTPFinger – Fingerprints over HTTP/HTTPS, using the ports listed in HTTP_PORTS in the configuration. Returns the server type and if it supports SSL.
- MySQLFinger – Fingerprints over MySQL (port 3306). Extracts MySQL banner info – Version, Major/Minor/Build and capabilities.
- ElasticFinger – Fingerprints over ElasticSearch (port 9200). Extracts the cluster name, node name and node version.
Adding a scanner/fingerprinter
To add a new scanner/fingerprinter, create a new class that inherits from HostScanner or HostFinger (depending on the interface). The class should be under the network module and should be imported under network/__init__.py.
To be used by default, two files need to be changed – infection_monkey/config.py and infection_monkey/example.conf to add references to the new class.
At this point, the Monkey knows how to use the new scanner/fingerprinter but to make it easy to use, the UI needs to be updated. The relevant UI file is monkey_island/cc/services/config.py.