Advertisements and marketing are inseparable concepts. Numerous online services do not charge customers only because they use different e-commerce and ad platforms that allow them to earn money. Many websites follow fair-play rules and do not show aggressive and repeated ads.
They also thoroughly select the advertisers and allow only tested and safe products to be advertised. In the end, both website visitors and service providers are happy. However, this is an ideal situation which can be easily disrupted.
Adware that injects horrible and sometimes dangerous ads into websites or hijacks one’s browser may greatly influence and diminish your online experience.
Here we should note a very important fact about rogue ads caused by adware and regular website advertisements. The latter is shown by the legit ad server while the former is caused by the infection that resides locally on a specific computer.
Evil ads are not bound by laws or regulations. They often get surplus and can cover the whole webpage. Adware-caused ads include banners, coupons, price charts, rogue software updates, full-page pop-ups and pop-unders, text ads that imitate Google Adwords. This diversity of forms allows cyber crooks to get the maximum amount of money from ad clicks. Sad but infected home users have to suffer big time.
First things first
If you already infected with adware the below tips will help you remove uninvited guests but before we start our story, I want to stress the importance of prevention techniques intended to keep adware away in the first place:
- First of all, please install any free software with caution. A lot of adware pieces penetrate your PC using bundling selling technique. When you install popular useful software which is completely safe, some unwanted tools can go in the same package. During the setup process, you can select Custom Installation and spot dangerous extras, which often can be overlooked.
- P2P protocol can be used to perform so-called Torrent Poisoning that is another method of adware distribution.
- Install a reliable VPN client that will encrypt and protect all your traffic. Useful VPN reviews can be found on the cooltechzone website.
- Do not install software recommended by popups or other suspicious alerts.
- Do not click on suspicious web links or spam email attachments.
For some users, the adware removal process may be kind of a challenge. Below I provide several simple methods that help to remove nasty adware from your PC.
Use the Windows uninstall function
This often comes as a starting point. Windows can help remove any unwanted software in just one click utilizing its built-in uninstall feature. Users can visit the Control Panel and find the Apps & features section. There, you can click the necessary entry and then hit the Uninstall button. Sophisticated adware may not be listed in Apps & features as malware creators use obfuscation techniques. In this case, users should proceed with other removal methods.
Perform manual removal
Often, removing adware manually from your browser is an efficient strategy when it comes to quick troubleshooting. It is the web browser that often stores the adware infection. The most important prerequisite of a successful cleaning is identifying and removing the malicious add-on or extension. Some adware can survive by adding a scheduled task to restore itself after the cleanup process. So, removing any bad extension is not as sufficient as running a full browser reset.
In Chrome, this option can be found in Advanced Settings. In Firefox, you have to click Help, then – Troubleshooting Information and click Refresh Firefox. For Edge, you can go to Apps & features in Windows, find Edge and press Reset. You should remember that all personal data is going to be removed after full browser reset.
Registry cleaning
A lot of adware samples create registry entries to stay longer on infected machines. This way malicious executables can automatically launch together with the routine system startup process. Go to Windows search and type Regedit. Then click Edit and select the Find button. Type the known adware name or its possible nicknames and press Enter. To be sure about the adware name, you can examine some ads that disturb you. Some ads provide an inscription like “Ads by Lyrics”.
Clean the Temp folder
After attacking your machine, potentially unwanted programs (PUAs) try also downloading additional files to the Temp folder, located under AppData > Local. It is easy to find this folder, just type AppData in the Windows search box. You should delete all entries there thus removing all traces of the virus.
Enable “Show Hidden Files” option
Many adware pieces hide their folders to thwart the removal process. Sometimes malicious files get placed inside AppData directory or Program Files folder. To be able to spot rogue files\folders, click Windows button + E, then click the View button in the top menu. Find the Hidden Items checkbox and check it. Carefully review Temp folder as well as Program Files folder and try to find recently added suspicious folders. In case adware is found – delete that folder completely.
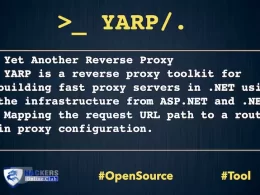
Use special software tools
It is strongly recommended to use special software that scans computers and removes all traces of known adware strains. This step is necessary because even if you thoroughly delete the infection manually, some fragments may still be present across scattered system folders. There are a lot of adware removal suites that can efficiently remove nasty software. AdwCleaner and Malwarebytes are free and reliable tools. They can scan PCs and delete all adware completely.