Cloud Sniper is a platform designed to manage Security Operations in cloud environments. It is an open platform which allows responding to security incidents by accurately analyzing and correlating native cloud artifacts.
It is to be used as a Virtual Security Operations Center (vSOC) to detect and remediate security incidents providing a complete visibility of the company’s cloud security posture.
With this platform, you will have a complete and comprehensive management of the security incidents, reducing the costs of having a group of level-1 security analysts hunting for cloud-based Indicators of Compromise (IOC). These IOCs, if not correlated, will generate difficulties in detecting complex attacks.
At the same time Cloud Sniper enables advanced security analysts integrate the platform with external forensic or incident-and-response tools to provide security feeds into the platform.
The cloud-based platform is deployed automatically and provides complete and native integration with all the necessary information sources, avoiding the problem that many vendors have when deploying or collecting data.
Cloud Sniper releases
1. Automatic Incident and Response
- WAF filtering
- NACLs filtering
- IOCs knowledge database.
- Tactics, Techniques and Procedures (TTPs) used by the attacker
2. Security playbooks
NIST approach
3. Automatic security tagging
4. Cloud Sniper Analytics
Beaconing detection with VPC Flow Logs (C2 detection analytics)
Cloud Sniper receives cloud-based and third-parties feeds and automatically responds protecting your infrastructure and generating a knowledge database of the IOCs that are affecting your platform. This is the best way to gain visibility in environments where information can be bounded by the Shared Responsibility Model enforced by cloud providers.
To detect advanced attack techniques, which may easily be ignored, the Cloud Sniper Analytics module correlates the events generating IOCs. These will give visibility on complex artifacts to analyze, helping both to stop the attack and to analyze the attacker’s TTPs.
Cloud Sniper is currently available for AWS, but it is to be extended to others cloud platforms.
Automatic infrastructure deployment (for AWS)
How it works
Cloud Sniper – AWS native version
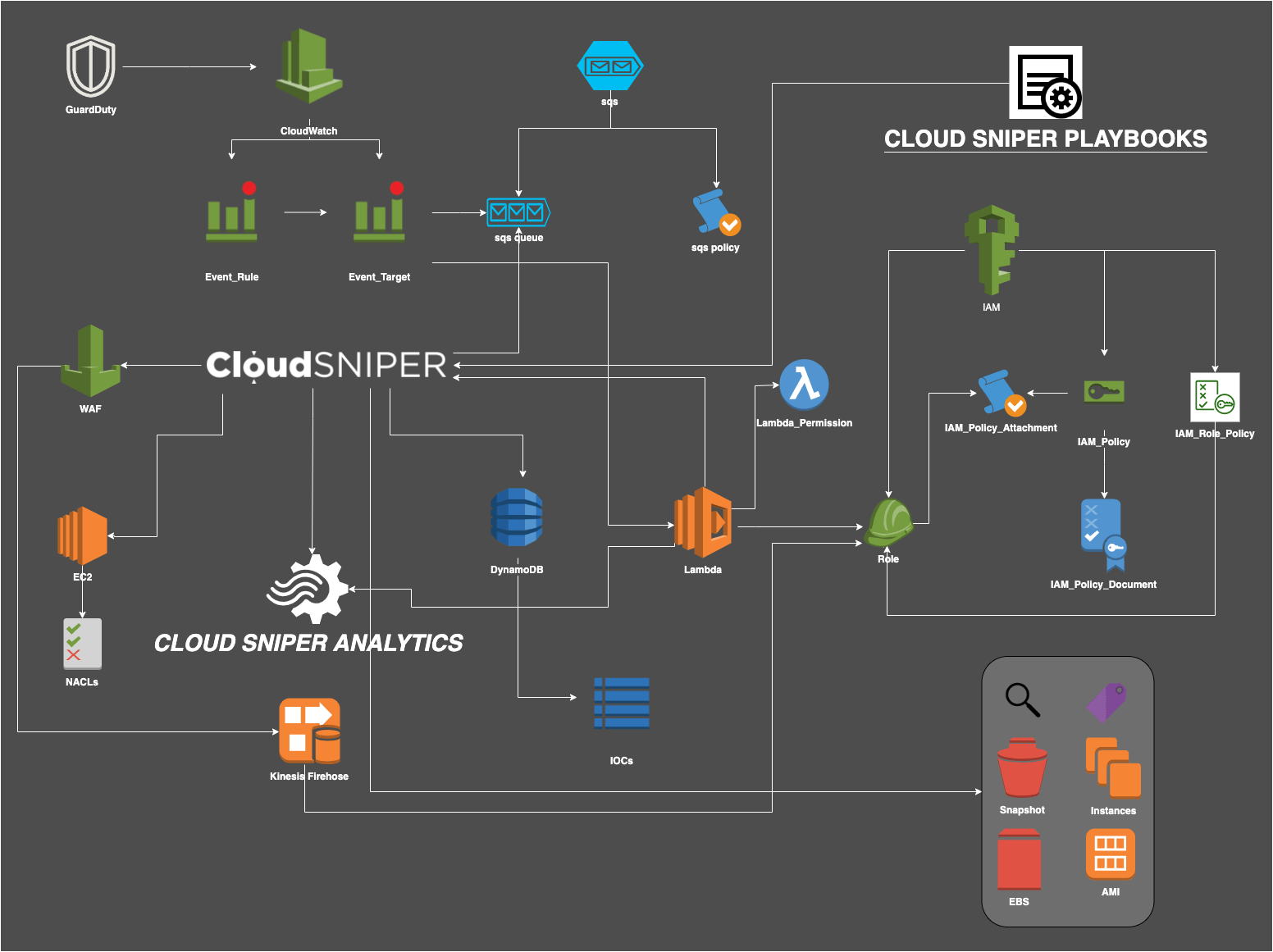
Cloud Sniper receives cloud-based or third-party feeds to take remediation actions in the cloud. Currently, the AWS native version, gets feeds from GuardDuty, a continuous security monitoring service that detects threats based on CloudTrial Logs/VPC Flow Logs/DNS Logs artifacts.
The GuardDuty security analysis is based on the Shared Responsibility Model of cloud environments, in which the provider has access to hidden information for the security analyst (such as DNS logs). GuardDuty provides findings, categorized in a pseudo MITRE’s TTP’s tagging.
Also Read: How To Configure Kali Linux on AWS Cloud
When GuardDuty detects an incident, Cloud Sniper automatically analyzes what actions are available to mitigate and remediate that threat. If layer 7/4/3 attacks are taking place, it blocks the corresponding sources, both in the WAF and in the Network Access Control Lists of the affected instances.
A knowledge database will be created to store the IOCs that affect the cloud environments and will build its own Threat Intelligence feeds to use in the future.
The Cloud Sniper Analytics module allows to analyze the flow logs of the entire network where an affected instance is deployed and obtain analytics on traffic behavior, looking for Command and Control (C2) activity.
Installation (for AWS)
Cloud Sniper uses Terraform to automatically deploy the entire infrastructure in the cloud. The core is programmed in python, so it can be extended according to the needs of each vSOC.
You must have:
1. AWS cli installed
2. A programmatic access key
3. AWS local profile configured
4. Terraform client installed
To deploy Cloud Sniper you must run:
1. ~$ git clone https://github.com/nicolasriverocorvalan/cloud-sniper.git
2. ~$ cd Cloud-Sniper
3. Set the environment variables corresponding to the account in the variables.tf file
4. Edit the main.tf file
provider “aws” {
region = “region”
shared_credentials_file = “/your-home/.aws/credentials”
profile = “your-profile”
}
5. ~/Cloud-Sniper$ terraform init
6. ~/Cloud-Sniper$ terraform plan
7. ~/Cloud-Sniper$ terraform apply [yes]
AWS artifacts integration:
The platform is integrated with the following cloud technologies:
1. GuardDuty findings
2. SQS
3. CloudWatch
4. WAF
5. EC2
6. VPC Flow Logs
7. DynamoDB
8. IAM
9. S3
10. Lambda
11. Kinesis Firehose
Upcoming Features and Integrations
1. Security playbooks for cloud-based environments
2. Security incidents centralized management for multiple accounts. Web Management UI
3. WAF analytics
4. Case management (automatic case creation)
5. IOCs enrichment and Threat Intelligence feeds
6. Automatic security reports based on well-known security standards (NIST)
7. Integration with third-party security tools (DFIR)