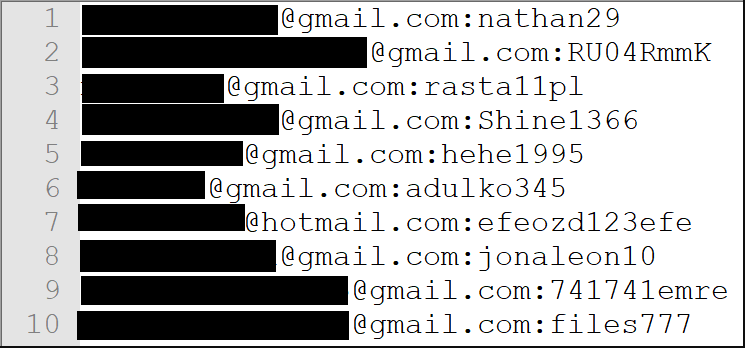
Yes, you heard it right, there are 42 Email ID and passwords uploaded on Free web hosting service Kayo.
According to the report, a collection of almost 42 million email address and plain text password pairs was uploaded to the anonymous file sharing service kayo.moe. The operator of the service contacted Have I Been Pwned (HIBP) to report the data which, upon further investigation, turned out to be a large credential stuffing list.
Kayo is a free and anonymous hosting service. The operator of Kayo reached out to TroyHunt for the report of a collection of files uploaded to the site. Hope you know about TroyHunt, he runs HaveIBeenPwned service, where a user can check their account that it has been compromised in a data breach or not.
So according to TroyHunt blog, Kayo sent the 1.8 GB data including 755 files to contain personal data breach with Email ID username and password in credential attacks. These attacks typically take data from multiple breaches then combine them into a single unified list so that they can be used in account takeover attempts on other services.
What is the Credential Stuffing Attack?
Credential stuffing is the automated injection of breached username/password pairs in order to fraudulently gain access to user accounts. This is a subset of the brute force attack category: large numbers of spilled credentials are automatically entered into websites until they are potentially matched to an existing account, which the attacker can then hijack for their own purposes.
Credential stuffing is a new form of attack to accomplish account takeover through automated web injection. Credential stuffing is related to the breaching of databases; both accomplish account takeover. Credential stuffing is an emerging threat.
Credential stuffing is one of the most common techniques used to take-over user accounts.
Credential stuffing is dangerous to both consumers and enterprises because of the ripple effects of these breaches. For more information on this please reference the Examples section showing the connected chain of events from one breach to another through credential stuffing.
What are the contents in leaked data?
There are a variety of files with logs, credit cards data and some Spotify details.
Spotify details? don’t worry it doesn’t indicate a Spotify breach. So, all the data is a combination of sources intended to be used for malicious purpose.
Troy determined that 89 percent of passwords are already in Have I Been Pwned (HIBP) collection. The filenames in the database do not point to a particular source because there is no single pattern for the breaches they appeared in. Also the data showed 91 percent of the passwords were already in Pwned Passwords, here you can check yours.
Protection
- The database trading is highly activated by cyber-criminals. HOC recommends you to generate unique passwords for each site you signup.
- Do not keep the same password, use different passwords for different accounts.
- Always use two-factor authentication, it helps to protect such kinds of attacks.
Also, HIBP service partnered with Mozilla browser. Firefox Monitor will be integrating with HIBP and also partnered with 1Password service.
Troy had announced in March 2018 that he would partner with 1Password. It is password manager which provides a place for users to store various passwords in one place. In the blog, he said, users can search HIBP directly from 1Password watchtower feature in the web version.
1Password is using Have I Been Pwned (HIBP) to find compromise accounts based on E-mail address. It works without sharing your E-mail address with others.