ZERO-DAY Vulnerability in Microsoft Windows 10 is Vulnerable To Gain Local System Privileges [UNPATCHED]
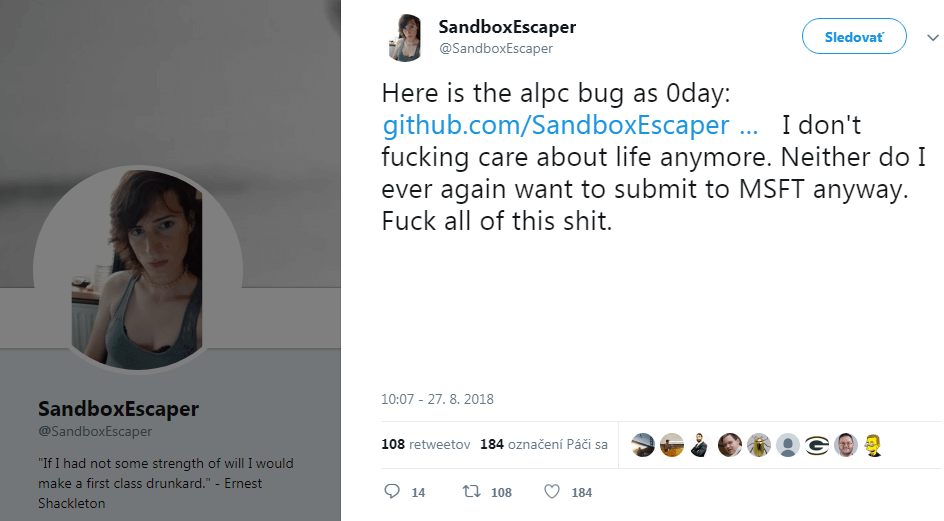
A security researcher has published a Windows Zero-day vulnerability on Twitter, that allows an attacker to gain system privileges on an affected computer. After that Twitter removed the status and suspended the account.
"https://twitter.com/SandboxEscaper/status/1034125195148255235"
What is Privilege Escalation Vulnerability?
Privilege escalation is the act of exploiting a bug, design flaw or configuration oversight in an operating system or software application to gain elevated access to resources that are normally protected from an application or user.
CERT Advisory published the details,
“Microsoft Windows task scheduler contains a local privilege escalation vulnerability in the Advanced Local Procedure Call (ALPC) interface, which can allow a local user to obtain SYSTEM privileges.
Microsoft Windows task scheduler contains a vulnerability in the handling of ALPC, which can allow a local user to gain SYSTEM privileges.”
The Patch is not available Yet. Zero-Day Works on fully patched Windows 10 operating system.
Will Dormann, the Vulnerability Analyst at the CERT/CC tweeted
I’ve confirmed that this works well in a fully-patched 64-bit Windows 10 system.
LPE right to SYSTEM! https://t.co/My1IevbWbz— Will Dormann (@wdormann) August 27, 2018
According to Register, The Microsoft said that the vulnerability would be fixed on upcoming Tuesday, which takes place on 11th September 2018.
It means all Windows 10 versions are still Vulnerable and affected including updated versions, until it is not fully patched by Microsoft.
What can we do?
Currently, Windows 10 users are recommended not to install any files coming from untrust sources. Otherwise, your System can be targeted to the local privilege escalation.
Microsoft offers Up to $250,000 USD in their Bug Bounty programs.