[Update]
Telegram blames China for DDOS Attack during HongKong Protests.
On Wednesday, Telegram received major cyber attack on its platform.
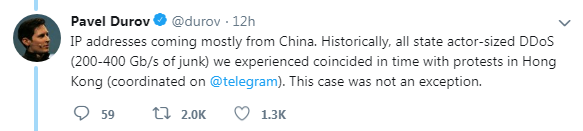
Pavel Durov, the Telegram CEO claims and reply in Tweet that.
“IP Addresses coming mostly from China. Historically, all state actor-sized DDOS (200-499 Gb/s of kunk) We experienced coincoded in time with protests in Hong Kong (coordinated on telegram). This case was not an exception.”
Breaking- Telegram Messaging App Faces DDOS Attack
“We’re currently experiencing a powerful DDoS attack, Telegram users in the Americas and some users from other countries may experience connection issues.”
Telegram gives update on Twitter
We’re currently experiencing a powerful DDoS attack, Telegram users in the Americas and some users from other countries may experience connection issues.
— Telegram Messenger (@telegram) June 12, 2019
“A DDoS is a “Distributed Denial of Service attack”: your servers get GADZILLIONS of garbage requests which stop them from processing legitimate requests. Imagine that an army of lemmings just jumped the queue at McDonald’s in front of you – and each is ordering a whopper.”
“The server is busy telling the whopper lemmings they came to the wrong place – but there are so many of them that the server can’t even see you to try and take your order.”
“To generate these garbage requests, bad guys use “botnets” made up of computers of unsuspecting users which were infected with malware at some point in the past. This makes a DDoS similar to the zombie apocalypse: one of the whopper lemmings just might be your grandpa.” Telegram tweeted.
For the moment, things seem to have stabilized.
— Telegram Messenger (@telegram) June 12, 2019
Telegram is a cloud-based instant messaging and voice over IP service. Telegram client apps are available for Android, iOS, Windows Phone, Windows NT, macOS and Linux. Users can send messages and exchange photos, videos, stickers, audio and files of any type.
In a distributed denial-of-service attack (DDoS attack), the incoming traffic flooding the victim originates from many different sources. This effectively makes it impossible to stop the attack simply by blocking a single source.











