The security researcher found a vulnerabilities in D-Link routers.
The cyber security research team of Digital Defense found three critical vulnerabilities and reported to D-Link.
The security team submitted a report accusing the DSR-250 Hardware Revision A1 using firmware v3.17 or older Authenticated remote command execution unauthenticated vulnerabilities. Since this product shares firmware with other models in the DSR Family, DSR-150 / DSR-250 / DSR-500 / DSR-1000AC will require updates to patch these issues.
The two vulnerabilities were confirmed, and patches are under development. One of the reported vulnerabilities is how the device functionally works, and D-Link will not correct it on this generation of products.
Reported Vulnerabilities as follow
Issue 1: Unauthenticated Remote LAN/WAN Root Command Injection
Impact: Unauthenticated users with access to the “Unified Services Router” web interface, either on LAN or WAN, can inject arbitrary commands via crafted requests, which will be executed with root privileges.
Details: The following lua cgi actions, which are accessible without authentication, execute a lua library function which passes user-supplied data to a call to os.popen() as part of a command intended to calculate a hash: /platform.cgi?action=duaAuth, /platform.cgi?action=duaLogout
Fix: Under Development Estimated Release Mid-December 2020
Issue 2: Authenticated Root Command Injection
Impact: Authenticated users with access to the “Unified Services Router” web interface, either on LAN or WAN, can inject arbitrary commands via crafted requests, which will be executed with root privileges.
Details: The Lua CGI, which handles requests from the “Package Management” form in the “Unified Services Router” web interface, has no server-side filtering for the multi-part POST parameters payload, which are passed to os. execute () functions intended to move the uploaded file to another directory.
Fix: Under Development Estimated Release Mid-December 2020
Issue 3: Authenticated Crontab Injection
Impact: Authenticated users with access to the “Unified Services Router” web interface, either on LAN or WAN, can inject arbitrary CRON entries, which will be executed as root by modifying a downloaded router configuration file, updating the CRC, and reuploading the resulting crafted configuration file.
Details: The configuration file’s mechanism is authenticated upon upload is trivially bypassed by a malicious user creating a crafted configuration file that adds new cron entries to execute arbitrary commands as root.
Response: D-Link declined recognition of this report. For this generation of product, the device uses a plain text config, which is the design to directly edit and upload the config to the same DSR devices accordingly. If D-Link mitigates issue #1 and #2, as well as other, recently reported issues, the malicious user would need to engineer a way of gaining access to the device to upload a configuration file, so we understand the report but classify the report as low-threat once the patched firmware is available.
Affected Devices
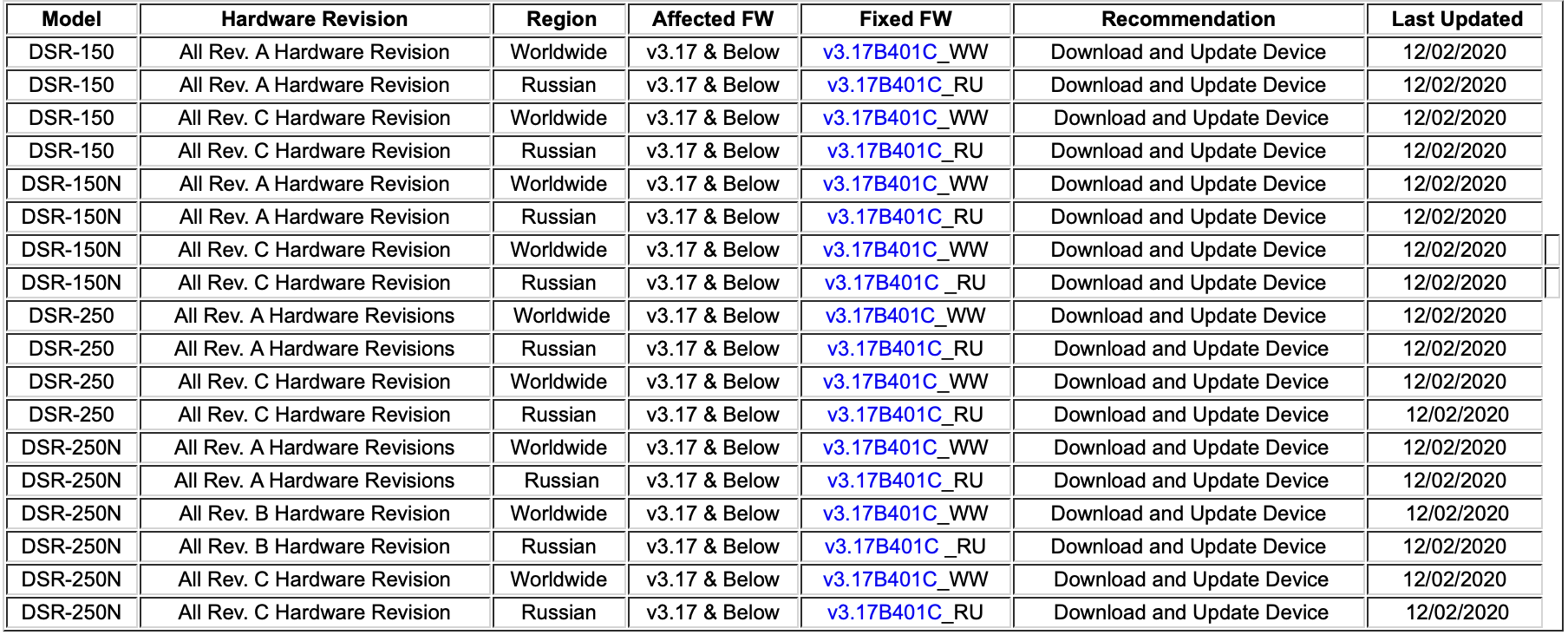
Security patch for your D-Link Devices
Firmware updates address the security vulnerabilities in affected D-Link devices. D-Link will update this continually and we strongly recommend all users to install the relevant updates.