Red Balloon Security developed and launches OFRAK at DefCon in Las Vegas.
OFRAK (Open Firmware Reverse Analysis Konsole) is a binary analysis and modification platform that combines the ability unpack, analyze, modify, and repack binaries.
It is an open source Reverse Engineering framework.
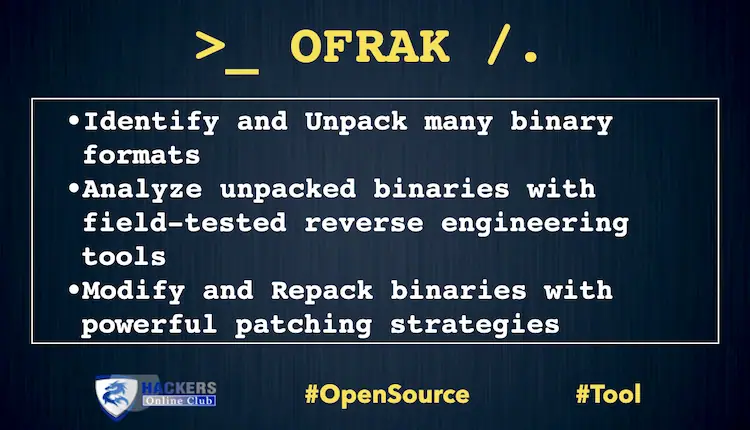
OFRAK combines the ability to:
- Identify and Unpack many binary formats
- Analyze unpacked binaries with field-tested reverse engineering tools
- Modify and Repack binaries with powerful patching strategies
OFRAK supports a range of embedded firmware file formats beyond userspace executables, including:
- Compressed filesystems
- Compressed & checksummed firmware
- Bootloaders
- RTOS/OS kernels
OFRAK equips users with:
- A Graphical User Interface (GUI) for interactive exploration and visualization of binaries.
- A Python API for readable and reproducible scripts that can be applied to entire classes of binaries, rather than just one specific binary.
- Recursive identification, unpacking, and repacking of many file formats, from ELF executables, to filesystem archives, to compressed and checksummed firmware formats.
- Built-in, extensible integration with powerful analysis backends (angr, Binary Ninja, Ghidra, IDA Pro).
- Extensibility by design via a common interface to easily write additional OFRAK components and add support for a new file format or binary patching operation.
GUI Frontend
The GUI view provides a navigable resource tree, and for the selected resource: metadata, hex navigation, and an entropy / byteclass / magnitude map sidebar. The GUI also allows for actions normally available through the python API like commenting, unpacking, analysis, modification and packing of resources.
Getting Started
See INSTALL.md for instructions on how to install OFRAK.
OFRAK uses Git LFS. This means that you must have Git LFS installed before you clone the repository! Install Git LFS by following the instructions here. If you accidentally cloned the repository before installing Git LFS, cd into the repository and run git lfs pull.
Tutorial
The best way to get started with OFRAK is to go through the interactive tutorial.
Run it with the following commands:
make tutorial-image # create the Docker image for the tutorial make tutorial-run
It takes a minute for the notebook to start up. The jupyter notebook URL and token will finally print on the terminal. Once running, you can access the tutorial from localhost:8888 with your web browser. Have fun!
GUI
OFRAK comes with a web-based GUI frontend for visualizing and manipulating binary targets. To activate the GUI from the OFRAK tutorial container, run:
docker exec -it ofrak-tutorial \ bash -c "nginx; python /ofrak_server.py 0.0.0.0 8877"
Once running, access localhost:80 and start by dropping anything you’d like into it!
Note that for now, the frontend only supports the ofrak_ghidra and ofrak_binary_ninja analyzer backends.
Docs
The official documentation for the most up-to-date OFRAK lives at https://ofrak.com/docs/.
If you would like to generate the docs yourself for offline viewing, you can serve them from the OFRAK container:
docker exec -it ofrak-tutorial \ mkdocs serve --dev-addr 0.0.0.0:8000
The offline docs can then be referenced via web browser at localhost:8080.
Guides and Examples
Once you’ve completed the tutorial, you’ll be interested in the following resources (which you can see on the left of this page):
More details about how OFRAK works and how to use it: User Guide and Contributor Guide;
References: Examples, covering common tasks you might want to perform with OFRAK, and the Code Reference.
Download OFRAK