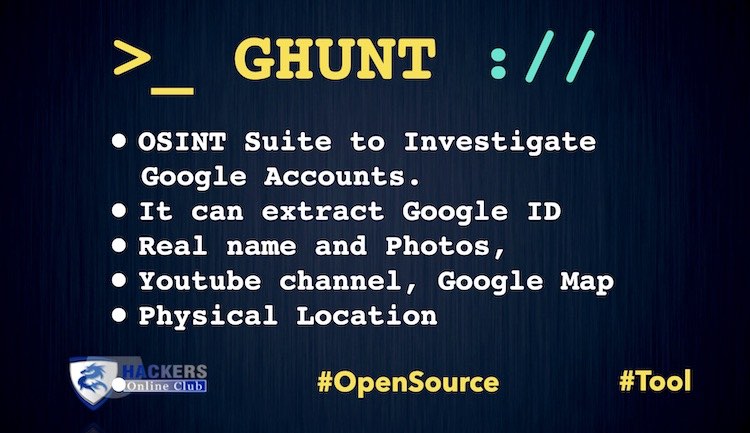
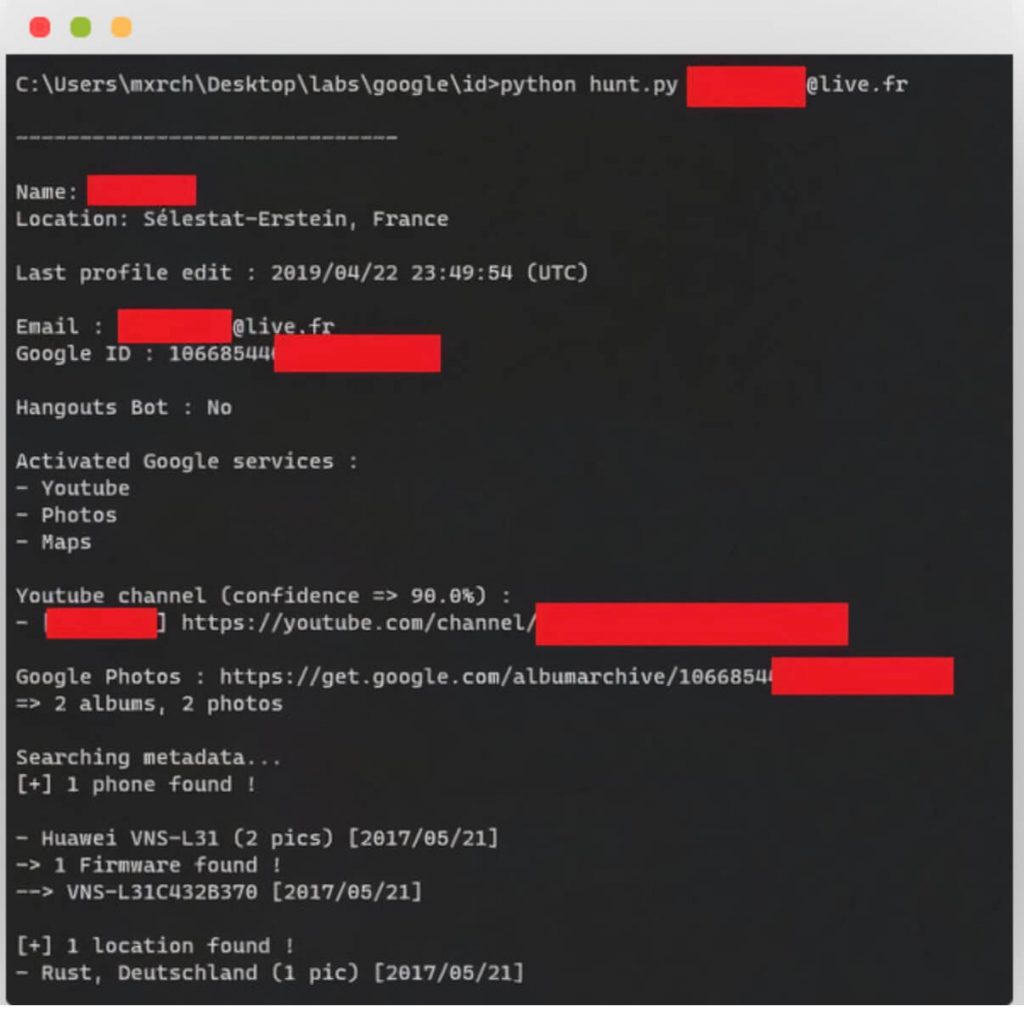
GHunt is an OSINT suite to extract information from any Google Account using an email.
It also helps to Investigate Google Accounts to find their real name, photos, location, Youtube channel.
What can GHunt find ?
Email module:
- Owner’s name
- Gaia ID
- Last time the profile was edited
- Profile picture (+ detect custom picture)
- If the account is a Hangouts Bot
- Activated Google services (YouTube, Photos, Maps, News360, Hangouts, etc.)
- Possible YouTube channel
- Possible other usernames
- Google Maps reviews (M)
- Possible physical location (M)
- Events from Google Calendar (C)
- Organizations (work & education) (A)
- Contact emails (A)
- Contact phones (A)
- Addresses (A)
- Public photos (P)
- Phones models (P)
- Phones firmwares (P)
- Installed softwares (P)
Document module:
- Owner’s name
- Owner’s Gaia ID
- Owner’s profile picture (+ detect custom picture)
- Creation date
- Last time the document was edited
- Public permissions
- Your permissions
Youtube module:
- Owner’s Gaia ID (through Wayback Machine)
- Detect if the email is visible
- Country
- Description
- Total views
- Joined date
- Primary links (social networks)
- All infos accessible by the Gaia module
Gaia module:
- Owner’s name
- Profile picture (+ detect custom picture)
- Possible YouTube channel
- Possible other usernames
- Google Maps reviews (M)
- Possible physical location (M)
- Organizations (work & education) (A)
- Contact emails (A)
- Contact phones (A)
- Addresses (A)
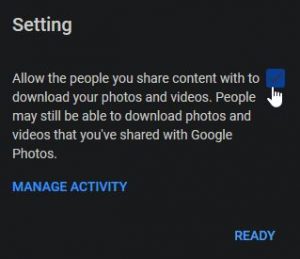
👉 The features marked with a (P) require the target account to have the default setting of Allow the people you share content with to download your photos and videos on the Google AlbumArchive, or if the target has ever used Picasa linked to their Google account. More info here.
👉 Those marked with a (M) require the Google Maps reviews of the target to be public (they are by default).
👉 Those marked with a (C) require user to have Google Calendar set on public (default it is closed).
👉 Those marked with a (A) require user to have the additional info set on profile with privacy option “Anyone” enabled.
Installation
Manual installation
Make sure you have Python 3.8+ installed. (I developed it with Python 3.8.1)
Some Python modules are required which are contained in requirements.txt and will be installed below.
1. Chromedriver & Google Chrome
This project uses Selenium and automatically downloads the correct driver for your Chrome version.
So just make sure to have Google Chrome installed.
2. Cloning
Open your terminal, and execute the following commands :
git clone https://github.com/mxrch/ghunt cd ghunt
3. Requirements
In the GHunt folder, run:
python3 -m pip install -r requirements.txt
Adapt the command to your operating system if needed.
Docker
The Docker image is automatically built and pushed to Dockerhub after each push on this repo.
You can pull the Docker image with:
docker pull ghcr.io/mxrch/ghunt
Then, you can use the docker_check_and_gen.sh and docker_hunt.sh to invoke GHunt through Docker, or you can use these commands :
docker run -v ghunt-resources:/usr/src/app/resources -ti ghcr.io/mxrch/ghunt check_and_gen.py docker run -v ghunt-resources:/usr/src/app/resources -ti ghcr.io/mxrch/ghunt ghunt.py
Usage
For the first run and sometime after, you’ll need to check the validity of your cookies.
To do this, run
check_and_gen.py.
If you don’t have cookies stored (ex: first launch), you will be asked for the required cookies. If they are valid, it will generate the Authentication token and the Google Docs & Hangouts tokens.
Then, you can run the suite like this:
python3 ghunt.py email larry@google.com python3 ghunt.py doc https://docs.google.com/spreadsheets/d/1BxiMVs0XRA5nFMdKvBdBZjgmUUqptlbs74OgvE2upms
Note: I suggest you make an empty account just for this or use an account where you never login because depending on your browser/location, re-logging in into the Google Account used for the cookies can deauthorize them.
Also See: How To Do Web Cookies Work In Browser?
Where I get these cookies ?
You can download the GHunt Companion extension that will automate the cookies extraction in 1-click !
You just need to launch the check_and_gen.py file and choose the extraction mode you want to use, between putting GHunt in listening mode, or copy/paste the encoded cookies in base64.
Manual
- Be logged-in to myaccount.google.com
- After that, open the Dev Tools window and navigate to the Network tab
- If you don’t know how to open it, just right-click anywhere and click “Inspect Element”.
- Go to myaccount.google.com, and in the browser requests, select the GET on “accounts.google.com” that gives a 302 redirect
- Then you’ll find every cookie you need in the “cookies” section.

How To Protecting Yourself?
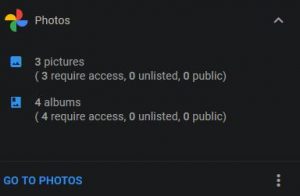
Regarding the collection of metadata from your Google Photos account:
Given that Google shows “X require access” on your Google Account Dashboard, you might imagine that you had to explicitly authorize another account in order for it to access your pictures; but this is not the case.
Any account can access your AlbumArchive (by default):
Here’s how to check and fix the fact that you’re vulnerable (which you most likely are):
Go to https://get.google.com/albumarchive/ while logged in with your Google account. You will be automatically redirected to your correct albumarchive URL (https://get.google.com/albumarchive/YOUR-GOOGLE-ID-HERE). After that, click the three dots on the top left corner, and click on setting
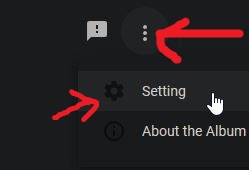
Then, uncheck the only option there:
On another note, the target account will also be vulnerable if they have ever used Picasa linked to their Google account in any way, shape or form.
For now, the only (known) solution to this is to delete the Picasa albums from your AlbumArchive.