Browsing Category
Vulnerability
95 posts
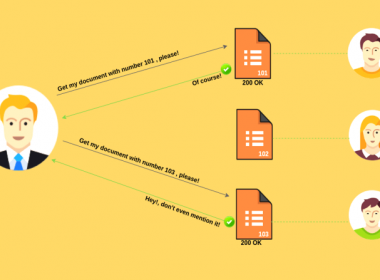
Insecure Direct Object References (IDOR)
Insecure Direct Object References (IDOR) Vulnerability allows attackers to bypass authorization and access resources directly by modifying the…
November 25, 2019
Four Major Fears That Software Developers Face
Four Major Fears That Software Developers Face Developers face plenty of challenges in today’s IT landscape. They’re required…
October 29, 2019
Untethered Jailbreak For iOS Devices Upto iPhone X Available
Untethered Jailbreak Available For All iOS Devices Till iPhone X Hacker Publicly release open source Jailbreak for iOS…
September 27, 2019
Intel CPUs Hit By NetCat Attack Vulnerability
Intel CPUs Vulnerable to NetCat Attack, which can leak the data remotely. The vulnerability affected in Intel products…
September 12, 2019
Twitter CEO Jack Dorsey Account Hacked
Oops! Twitter CEO Jack Dorsey Account Hacked. Yes, you heard right. Hackers group posted offensive tweets with @Jack…
August 31, 2019
Apple Disabled Walkie-Talkie APP Due to Eavesdrop
Apple has temporarily disabled its Watch Walkie Talkie App due to critical flaw found. What is the Bug…
July 12, 2019
Hardware Security Module Vulnerability – Researchers Unveiled
There are two security researchers from Hardware wallet maker ‘Ledger’ have unveiled the vulnerabilities in Hardware Security Module…
June 10, 2019
OS Command Injection Vulnerability Found In WordPress Backup Plugin
OS Command Injection Vulnerability In WordPress Database Backup Plugin. The originally disclosed vulnerability present in WP Database Backup…
May 29, 2019
Two Microsoft Zero-Day Exploit Available [Unpatch]
The Hacker group Sanboxscraper has Published Two More Microsoft Zero-Day Vulnerability, which remains Unpatch. Microsoft patched CVE-2019-0841 in…
May 23, 2019
Titan Security Keys Could Be Exploited- Google
Google Titan Security Key is Vulnerable. Titan Security Keys Could Be Hacked through Bluetooth pairing. In July 2018,…
May 16, 2019