Browsing Category
Tutorials
112 posts
Stack Based Buffer Overflow PCMAN FTP Server Tutorial
Stack-based buffer overflows, which are more common among attackers, exploit applications and programs by using what is known…
June 25, 2019
What is Stack Based Buffer Overflow?
A buffer is a temporary area for data storage. When a program or system process places more data more than…
June 23, 2019
USB Data Recovery- How To Restore Deleted Files
USB Data Recovery- Restore deleted files from USB database. Have you deleted an important file from your USB…
June 19, 2019
6 Email Marketing Hacks – That Will Help You Stand Out from Your Competition
There are many tactics used by online businesses to reach customers. Today, you can find avenues like print…
June 18, 2019
Insights From Exam-labs: The Most Popular VMware Certifications
A VMware certificate looks great on your resume. It is a symbol of achievement and something to be…
June 17, 2019
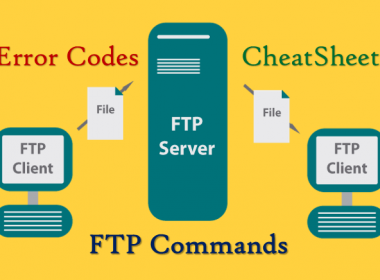
FTP Server Commands And Error Codes Cheatsheet
FTP- The File Transfer Protocol is a standard network protocol used for the transfer of computer files between…
June 14, 2019
Cisco CCNA Routing and Switching Certification Made Easier with PrepAway
Cisco CCNA Routing and Switching (R&S) Certification- One thing that no one can run away from, is the…
May 22, 2019
How To Remove Your Phone Number From TrueCaller?
To Remove Your Phone Number from TrueCaller following the steps. Want to delete your Truecaller profile from the…
May 9, 2019
Examsnap Build Your Career with Certifications From Cisco
Want to build a successful career in the IT industry? Well, then you need a credential from a…
May 7, 2019
QRLJacking- Hack Accounts Login With QR code
QRLJacking or Quick Response Code Login Jacking is a simple social engineering attack vector capable of session hijacking…
April 19, 2019