Browsing Category
Security
490 posts
Defining, Understanding, and Applying Cybersecurity Auditing: A Comprehensive Guide
The cybersecurity field is growing more complex by the day. Businesses both big and small are constantly striving…
September 14, 2022
Vulnerability Scanning Network: Importance, Steps, and Differences
What is vulnerability scanning for networks? Why are vulnerability scanning network important? The answer to these questions is…
September 14, 2022
PassKeys – Apple New Generation Password Authentication
Apple’s PassKeys – A New Generation Password Authentication. Using passkeys for account authentication is far simpler and more secure…
September 7, 2022
4 Best Practices Of Cloud Access Control
Cloud access control allows business people and other professionals to remotely control and manage gates and doors through…
September 5, 2022
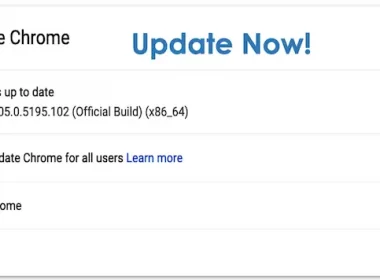
Google Fixes Chrome Browser Zero-Day Bugs – Update Now
Google releases security updates for Chrome Browser, and fixes zero-day vulnerability. The Chrome browser stable channel has been…
September 3, 2022
Top 3 Biggest Security Holes in Your Business
Cyber security threats pose a serious threat to businesses today. With the increasing automation of attacks by attackers,…
September 1, 2022
What Is EDR Security, and How Does It Protect Remote Workers?
Regardless of how tired we all are of discussing the pandemic, one thing is certain — it has…
August 30, 2022
DuckDuckGo Offers Email Protection Service @duck.com
DuckDuckGo announces Email protection service to all users. Using Email Protection, you will receive a free “@duck.com” email address…
August 26, 2022
Apple Fixes Zero-Days Flaws – Update iOS, iPadOS, macOS and Safari
Apple fixes two zero-day vulnerabilities and security updates for iOS, iPadOS, macOS platforms. However, it is likely that…
August 19, 2022
Kali Linux 2022.3 – Added Bruteshark And Test Lab Environment
Offensive Security has released Kali Linux 2022.3 with major updates. It is a popular platform for ethical hackers…
August 10, 2022