Browsing Category
Security
490 posts
LABRAT Campaign Strikes: GitLab Flaw Exploited For Cryptojacking and Proxyjacking
A new campaign called LABRAT is targeting GitLab with cryptojacking and proxyjacking. LABRAT, a financially motivated operation, has…
August 18, 2023
Unmasking The Rising Malware Threat in MacOS – Report
Macs are not invulnerable! Confuse? The Report Unmasking a Malware threat in MacOS Malware Targeting MacOS is a…
August 10, 2023
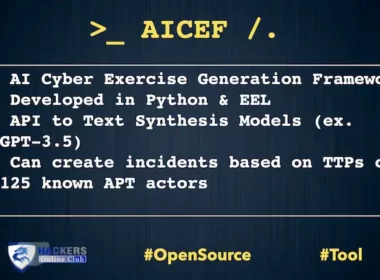
AiCEF AI CyberSecurity Exercise Framework
AiCEF (AI Cybersecurity Exercise Generation Framework) is a suite implementing the accompanying framework to harness the intelligence available…
August 8, 2023
U.S. Officials Announces Cyber Trust Mark For IoT Security
The United States has officially launched its much-anticipated cybersecurity labelling program Cyber Trust for Internet of Things (IoT)…
July 20, 2023
Incorporating IT And Security Systems In Healthcare
In the rapidly evolving world of healthcare, integrating Information Technology (IT) and security systems has become more than…
July 20, 2023
Empowering Secure And Reliable Data Collection With Backconnect Proxies
With e-commerce booming and digital marketing becoming the dominant mode of building customer engagement, more and more companies…
June 29, 2023
CashApp Glitch Or Issue? Users Reported
The CashApp allows users to easily transfer money to one another using its app. What is CashApp? Cash…
June 27, 2023
How To Deal With The Consequences of A Data Breach?
In today’s interconnected world, the prevalence of data breaches has become a pressing concern for individuals and organizations…
June 26, 2023
Deep Dive Into Deep Packet Inspection: Enhancing Performance And Privacy In The Connected World
It has come to everyone’s notice how the world is transforming at an exponential rate due to this…
June 22, 2023
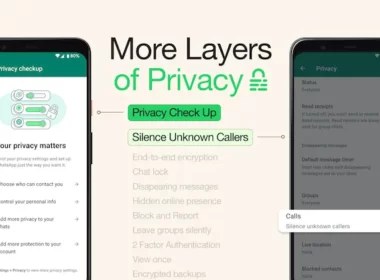
WhatsApp Added Silence Unknown Callers And Privacy Checkup Feature
Meta introduces new features, “Silence Unknown Calls,” and “Privacy Checkup” in WhatsApp. What is Silence Unknown Callers? Silence…
June 20, 2023