Priyanshu Sahay
1017 posts
Priyanshu Sahay is a cybersecurity expert with a passion for protecting individuals and organizations from the cyber threats. Avid learner and stays up-to-date with the latest trends and technologies in cybersecurity. 10 years of experience in the field, including being listed on bug bounty platforms and receiving rewards from various companies like Microsoft, IBM, Slaesforce, Splunk and more for identifying and reporting vulnerabilities.
Unleash The Power of a Free Vulnerability Scanner
Unleash the Power of a Free Vulnerability Scanner Are you looking to keep your systems secure? Look no…
September 11, 2023
APPLE Devices Emergency Security Patch For Pegasus Spyware
Apple released emergency security patch for its operating systems on Thursday to fix two zero-day flaws exploited in…
September 8, 2023
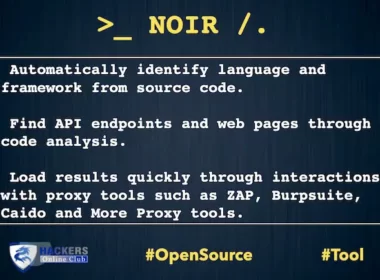
NOIR Network Attack Surface Detector From Source Code
Noir An Network Attack Surface Detect and Analysis From Source Code Key Features Automatically identify language and framework…
September 7, 2023
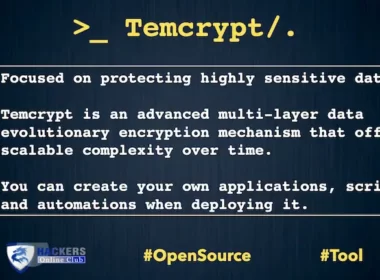
Temcrypt – Evolutionary Encryption Framework
Temcrypt – Evolutionary Encryption Framework Based On Scalable Complexity Over Time temcrypt SDK Focused on protecting highly sensitive…
September 6, 2023
How To Remove A Video Uploaded by Someone Else on TikTok
TikTok is a popular platform for sharing short videos. However, some users may upload videos without the user…
September 1, 2023
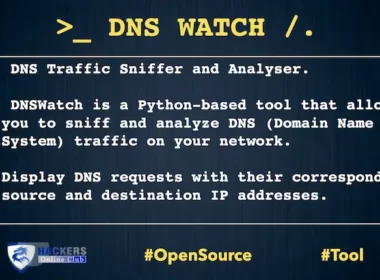
DNSWatch – DNS Traffic Sniffer And Analyzer
DNSWatch is a Python-based tool that allows you to sniff and analyze DNS (Domain Name System) on your…
September 1, 2023
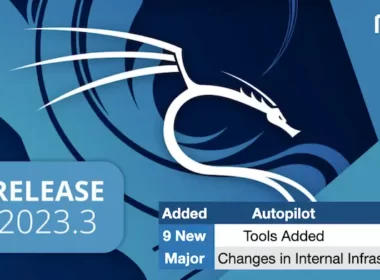
Kali Linux 2023.3 Releases With Autopilot and Redesign
Introducing new Kali 2023.3 with new packages, tools, and updates, alongside significant behind-the-scenes changes for improved performance and…
August 24, 2023
RedEye To Manage Data During Pentest Operation
This project was built by pentesters for pentesters. Redeye is a open source suite to help you manage…
August 22, 2023
LABRAT Campaign Strikes: GitLab Flaw Exploited For Cryptojacking and Proxyjacking
A new campaign called LABRAT is targeting GitLab with cryptojacking and proxyjacking. LABRAT, a financially motivated operation, has…
August 18, 2023
TestSSL To Test TLS/SSL Encryption On Any Port
Testing TLS/SSL encryption anywhere on any port. testssl.sh is a free command line tool, which checks a server’s…
August 14, 2023