Introducing new Kali 2023.3 with new packages, tools, and updates, alongside significant behind-the-scenes changes for improved performance and user experience.
-
Internal Infrastructure – Major stack changes are underway
-
Kali Autopilot – The automation attack framework has had a major overhaul
-
New Tools – 9 new tools added
Kali Linux is a Linux-based operating system that is designed for digital forensics and penetration testing. The development of Kali Linux is handled by Offensive Security. Kali Linux is a platform, not just an operating system or set of tools. It aims to make pentesting easier and can be installed on any Linux system.
Internal Infrastructure
After Debian 12 was released this summer, This release redesigned and re-architected the Kali Linux infrastructure.
- OS version (Debian 12)
- CDN/WAF (Cloudflare)
- Web server service (Nginx)
- Infrastructure as Code (Ansible)
Kali Autopilot
With the release of Kali 2023.1, Kali Autopilot debuted. It has undergone significant changes, featuring a redesigned GUI and numerous new features.
Kali Autopilot is an automated attack framework that follows pre-defined “attack scenarios.” It was originally developed for the defensive side of Kali.
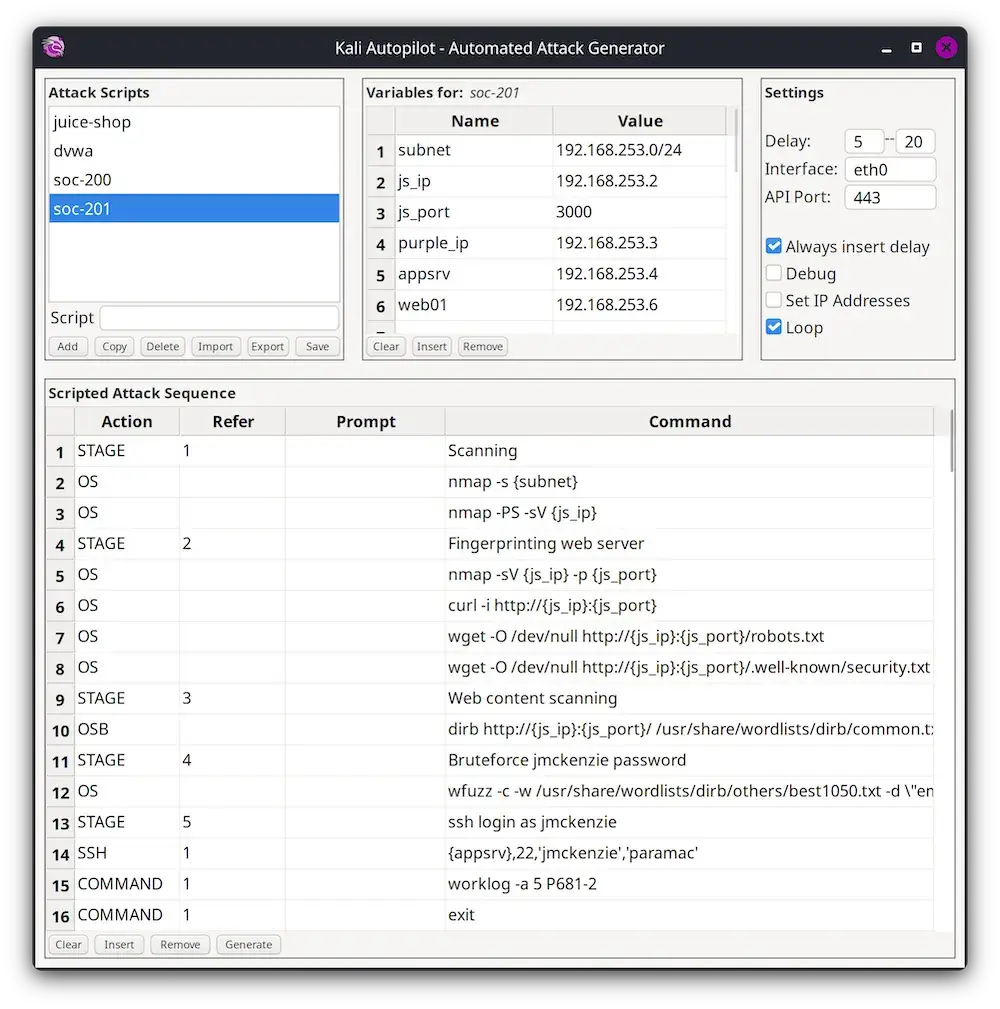
Demonstrating Kali’s offensive side is much easier, especially when the shells pop up. But when it comes to the defensive side, how do you know if you have set things up?
You start to ask questions:
- Are the Intrusion Detection System (IDS) and the Web Application Firewall (WAF) detecting malicious activities?
- Is the Security information and event management (SIEM) ingesting the right logs?
- Are the dashboards and alerts tuned to detect attacks?
- Are the analysts trained to find the needle in the haystack?
- Has it been tested? How can you test?
Kali Autopilot includes a GUI tool for designing attacks and generating attack scripts. It can be used manually or as a service and has a web API interface for remote control.
New Tools in Kali Added
We will kick it off with what’s new (to the network repositories):
- Calico – Cloud-native networking and network security
- cri-tools – CLI and validation tools for Kubelet Container Runtime Interface
- Hubble – Network, Service & Security Observability for Kubernetes using eBPF
- ImHex – A Hex Editor for reverse engineers, programmers, and people who value their retinas when working at 3 AM
- kustomize – Customization of kubernetes YAML configurations
- Rekono – Automation platform that combines different hacking tools to complete pentesting processes
- rz-ghidra – Deep ghidra decompiler and sleigh disassembler integration for rizin
- unblob – Extract files from any container formats
- Villain – C2 framework that can handle multiple reverse shells, enhance their functionality, and share them among instances.
Kali NetHunter Updates
We are excited to announce the launch of the newly redesigned Kali NetHunter app, which includes a brand new NetHunter Terminal. Additionally, we have added a SELinux disabler due to popular demand.

Kali NetHunter kernel side, there are numerous updates:
- LG V20 for Lineage 19.1
- Nexus 6P for Android 8.0 (Oreo)
- Nothing Phone (1) for Android 12 (Snowcone) and 13 (Tiramisu) (new)
- Pixel 3/XL for Android 13 (Tiramisu)
- Samsung Galaxy A7 for LineageOS 18.1 (latest)
- Xiaomi Mi A3 for Lineage 20
- Xiaomi Redmi 4/4X for VoltageOS 2.5
How To Get or Update Kali Linux 2023.3
┌──(kali㉿kali)-[~] └─$ echo "deb http://http.kali.org/kali kali-rolling main contrib non-free non-free-firmware" | sudo tee /etc/apt/sources.list [...] ┌──(kali㉿kali)-[~] └─$ sudo apt update && sudo apt -y full-upgrade [...] ┌──(kali㉿kali)-[~] └─$ cp -vrbi /etc/skel/. ~/ [...] ┌──(kali㉿kali)-[~] └─$ [ -f /var/run/reboot-required ] && sudo reboot -f
You should now be on Kali Linux 2023.3. We can do a quick check by doing the following:
┌──(kali㉿kali)-[~] └─$ grep VERSION /etc/os-release VERSION= "2023.3" VERSION_ID= "2023.3" VERSION_CODENAME= "kali-rolling" ┌──(kali㉿kali)-[~] └─$ uname -v #1 SMP PREEMPT_DYNAMIC Debian 6.3.7-1kali1 (2023-06-29) ┌──(kali㉿kali)-[~] └─$ uname -r 6.3.0-kali1-amd64
Note: Uname- r output may differ depending on the system architecture.