The Arp-scan network discovery command is designed to map physical (MAC) addresses to logical (IP) addresses. The Address Resolution Protocol (ARP) uses a simple message format containing one address resolution request or response.
The size of the ARP message depends on the upper layer and lower layer address sizes, which are given by the type of networking protocol (usually IPv4) in use and the type of hardware or virtual link layer that the upper layer protocol is running on. The message header specifies these types, as well as the size of addresses of each.
The message header is completed with the operation code for request (1) and reply (2). The payload of the packet consists of four addresses, the hardware and protocol address of the sender and receiver hosts.
The Arp-scan command uses the Address Resolution Protocol (ARP) to identify all active network assets that may not typically be recognised by network scanning devices.
The main purpose of the Arp-scan is to discover all the active devices within an IPv4 range, even those that are protected by a firewall that is created to hide the device’s presence. Whether using WIFI or ethernet, the IPv4 devices on your local-area network (LAN) are required to respond or they are unable to communicate.
The ARP Scan (also called ARP Sweep or MAC Scanner) is a very fast ARP packet scanner that shows every active IPv4 device on your Subnet. Since ARP is non-routable, this type of scanner only works on the local LAN (local subnet or network segment).
The ARP Scan shows all active devices even if they have firewalls. Devices cannot hide from ARP packets like they can hide from Ping. To find active IP addresses outside your subnet, use the Ping Scan.
The Arp-scan network discovery command is an essential piece that every IT and Cyber Security professional should know and understand. Every ethical hacker must have a strong understanding of fundamental networking protocols, of which ARP is at the top of the list. Without this protocol, LANs would no longer function, which means that users must be competent when checking the contents of their ARP cache and also have a solid understanding of performing ARP scanning.
Network scanning is one of the steps of penetration testing. There are different and popular commands to scan network line masscan, nmap etc. Arp-scan is a specifically designed to scan network with layer 2 or mac or Ethernet ARP packets.
INSTALL
We can install arp-scan with the following command.
$ sudo apt install arp-scan -y
HELP
We can print help information with the -h option.
$ arp-scan -h
SYNTAX
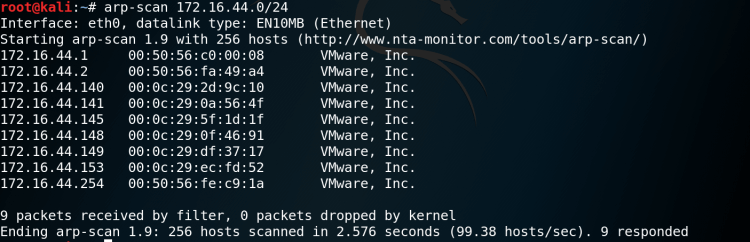
arp-scan being used to scan the network 172.16.44.0/24.
$arp-scan [host IP with subnet]
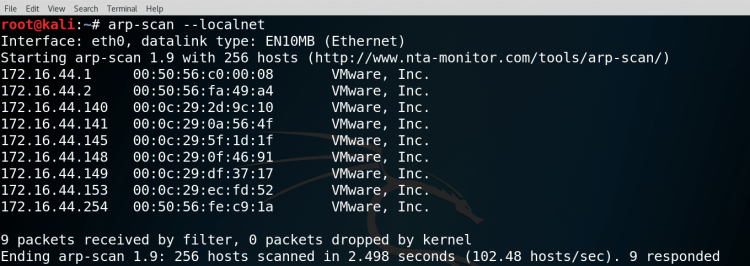
arp-scan is scanning local network with a single options named –localnet or -L .
This will scan whole local network with ARP packets. While using arp-scan we need root privileges.
$arp-scan --localnet
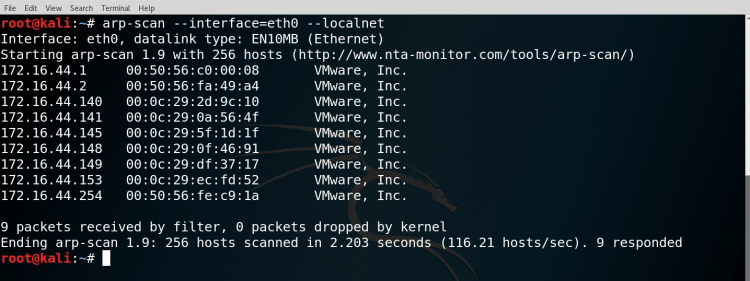
Enterprise environments requires more than one network interface for backup, load balancing etc. In this situations we need to specify network interface. We will use -i option.
In the example we will use network interface named eth0.
$ arp-scan --interface=eth0 --localnet
During the scan process our exisiting mac address will be used. This may create some clue about the scan. We can change the source mac address during scan. This will make all sent packets have different mac address than our hardware mac address. We will use –destaddr or -T option.
$ arp-scan -T aa:bb:cc:dd:ee:ff
Another useful option is setting destination mac address with –srcaddr or -S option
$arp-scan -S aa:bb:cc:dd:ee:ff
At the end I would conclude that it is a very simple yet a very powerful command. Once you’ve found the MAC address, you can find more info about that device by matching that MAC address to it’s vendor.
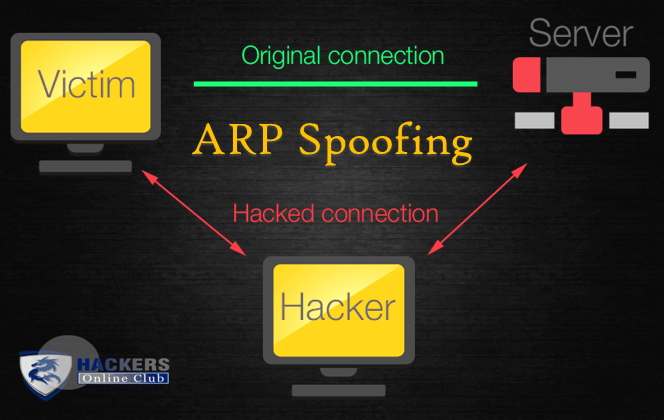
It is important to understand ARP/MAC responses for penetration tester and it is used heavily for ArpSpoof and Man-In-The-Middle Attack.
It also helps in cases when someone is spoofing IP address and DoS-ing your server. You can however spoof MAC address easily to evade trace.
So try to use arp-scan and use various other commands using the help menu.