Zero-day vulnerabilities are not uncommon for now. An unpatched zero-day vulnerability is a security flaw unknown to the software vendor, that leave the software vulnerable to hackers.
As a result, these vulnerabilities can be extremely dangerous and can compromise sensitive data and personal information.
Apple Fixes Zero-Day
Apple released updates for iOS, macOS and Safari that included a WebKit zero-day vulnerability.
WebKit – CVE-2023-23529
- Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, iPad mini 5th generation and later
- Impact: Processing maliciously crafted web content may lead to arbitrary code execution. Apple is aware of a report that this issue may have been actively exploited.
- Description: A type confusion issue was addressed with improved checks.
Kernel – CVE-2023-23514
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: An app may be able to execute arbitrary code with kernel privileges
Description: A use after free issue was addressed with improved memory management.
You can check lists security updates for Apple software here. Millions of users could be affected by this vulnerability.
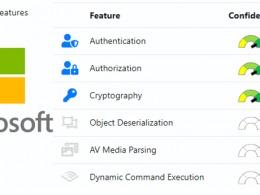
Microsoft patches 75 Vulnerabilities.
There are 75 Vulnerabilities have fixed by Microsoft with the Average CVSS Score 7.8 severity.
Following CVE’s impact Zero Day Vulnerabilities
- CVE-2023-21715 – Microsoft Office Security Feature Bypass Vulnerability with CVSS score: 7.3
- CVE-2023-21823 – Windows Graphics Component Elevation of Privilege Vulnerability with CVSS score: 7.8
- CVE-2023-23376 – Windows Common Log File System (CLFS) Driver Elevation of Privilege Vulnerability CVSS score: 7.8
“An authenticated attacker could exploit the vulnerability by convincing a victim, through social engineering, to download and open a specially crafted file from a website which could lead to a local attack on the victim computer.”
“The attack itself is carried out locally by a user with authentication to the targeted system,” Microsoft said in advisory for CVE-2023-21715.
“The Windows Common Log File System Driver is a component of the Windows operating system that manages and maintains a high-performance, transaction-based log file system,” Immersive Labs’ Nikolas Cemerikic said.
“It is an essential component of the Windows operating system, and any vulnerabilities in this driver could have significant implications for the security and reliability of the system.”
Apple and Microsoft have patched this vulnerability. To keep your system protected, make sure you install the latest updates.