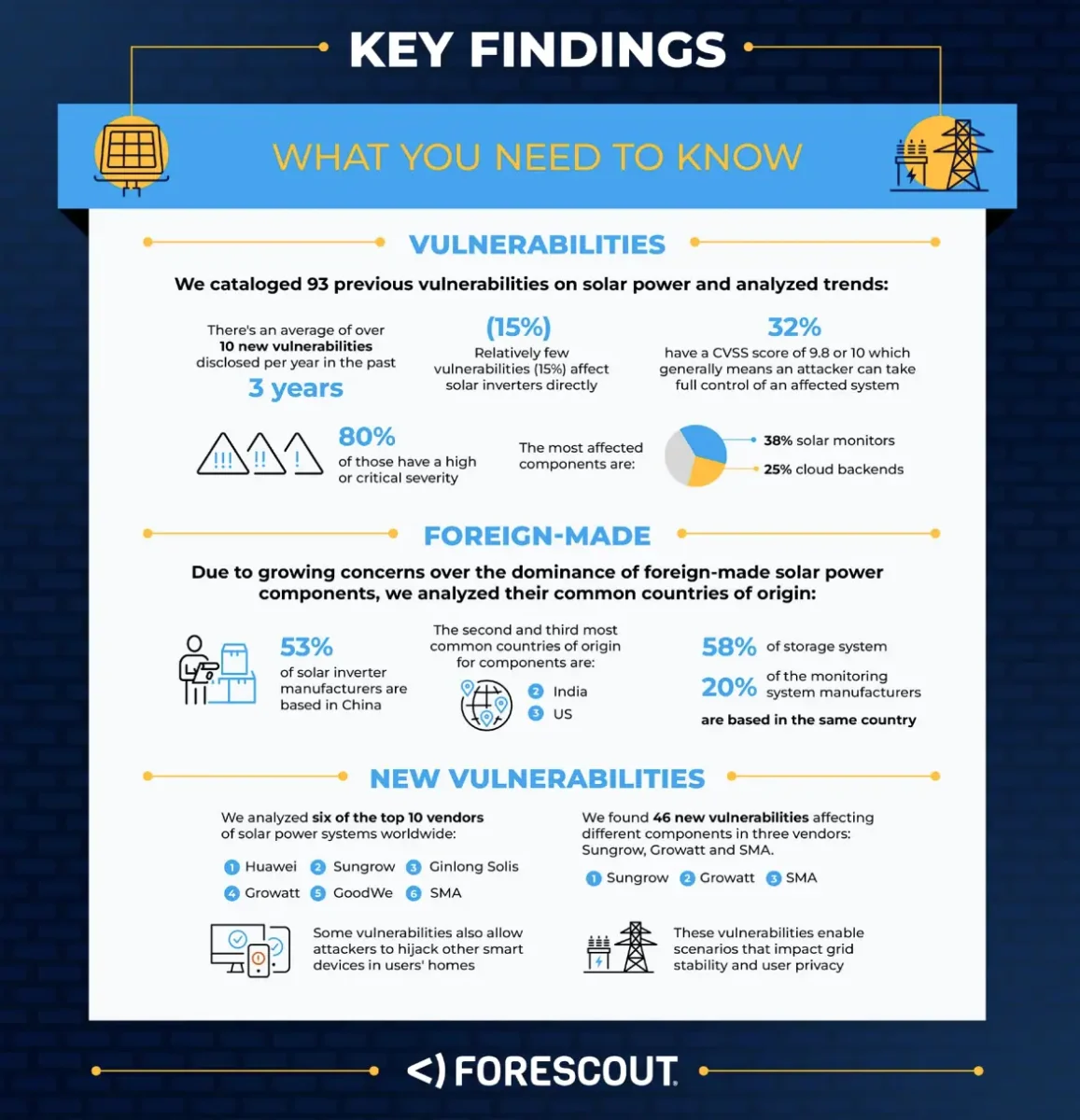
San Jose, CA – A new report by Forescout’s Vedere Labs has uncovered critical vulnerabilities in solar energy devices, potentially exposing millions of systems worldwide to cyberattacks. The “Sun Down” report reveals that devices from multiple manufacturers, including solar inverters and charge controllers, contain severe security flaws that could allow malicious actors to disrupt power grids, steal sensitive data, and even cause physical damage.
Key Findings and Impacts:
- Widespread Vulnerabilities: The research identified vulnerabilities in devices from leading vendors, indicating a systemic issue across the solar energy sector.
- Remote Code Execution (RCE): Many devices are susceptible to RCE attacks, allowing attackers to take complete control of the system. This could lead to manipulation of power output, grid destabilization, and even physical damage to connected equipment.
- Lack of Basic Security: The report highlights the absence of fundamental security measures, such as strong authentication, secure communication protocols, and regular firmware updates.
- Impact on Critical Infrastructure: Solar energy systems are increasingly integrated into critical infrastructure, making them attractive targets for cyberattacks. A successful attack could disrupt power supply, causing widespread blackouts and economic damage.
- Data Exposure: Some devices store sensitive data, including user credentials and configuration settings, which could be stolen by attackers.
- Supply Chain Risks: Vulnerabilities within the supply chain of these devices are a major concern, as they can be exploited to compromise numerous systems.
- Potential for Botnets: compromised devices can be used to form botnets, and used to conduct DDOS attacks, or other malicious activity.
Inventory and Assessment: Organizations should conduct a thorough inventory of their solar energy devices and assess their vulnerability to the identified flaws.
Firmware Updates: Apply firmware updates from vendors as soon as they become available. If updates are unavailable, isolate the devices from critical networks.
Network Segmentation: Implement network segmentation to isolate solar energy devices from other critical systems, reducing the potential impact of a successful attack.
Strong Authentication: Enforce strong authentication measures, including multi-factor authentication, to prevent unauthorized access.
Secure Communication: Use secure communication protocols, such1 as TLS/SSL, to protect data transmitted between devices and control systems. Monitoring and Detection: Implement continuous monitoring and intrusion detection systems to identify and respond to suspicious activity.
Vendor Communication: Engage with vendors to demand timely security updates and improved security practices.
Cybersecurity Best Practices: Follow industry best practices for cybersecurity, including regular security assessments, penetration testing, and employee training.
Regulation and standards: Governments and Industry need to create and enforce stricter cybersecurity standards for IoT and OT devices, especially those connected to critical infrastructure.
The Urgent Need for Action:
The “Sun Down” report underscores the urgent need to address the security vulnerabilities in solar energy devices. As the world transitions to renewable energy sources, it is crucial to ensure that these systems are secure and resilient against cyberattacks. Failure to do so could have severe consequences for critical infrastructure and public safety.
This report serves as a wake-up call for the solar energy industry and organizations that rely on these systems. Proactive measures are essential to mitigate the risks and protect against potential cyberattacks.