You don’t have to remember complex passwords anymore. Biometric security, the cutting-edge technology using your unique physical or behavioral characteristics for identification and authentication, is taking center stage. Imagine unlocking your phone with a glance, accessing your bank account with your heartbeat, or securing your office with your gait!
But what exactly is Biometric security?
Instead of relying on external tokens or memorized information, biometric security leverages your inherent physiological or behavioral traits as the ultimate key.
Think of it like a high-tech lock that only recognizes your fingerprint, iris pattern, or even the way you walk. No two people are exactly alike, making these biological and behavioral markers incredibly secure and difficult to fake.
Also Read | The Future of Data Security is Biometrics Not Passwords
How Does it Work?
Biometric systems generally follow these steps:
- Capture: Specialized sensors or scanners capture your biometric data. This could involve scanning your fingerprint, taking an iris photo, or recording your voice.
- Analysis: The captured data is processed and converted into a digital template, essentially a unique code representing your biometric feature.
- Matching: When you attempt to gain access, the system compares your new biometric data to the stored template. If they match, you’re granted access. If not, the system triggers an alert.
Types of Biometric Security:
Biometrics comes in many flavors, each with its strengths and weaknesses.
Here are some common types:
- Fingerprint recognition: The most widely used, relying on the unique patterns of your fingerprints.
- Iris recognition: Highly accurate, scanning the intricate details of your colored eye ring.
- Facial recognition: Analyzing your facial features and geometry for identification.
- Voice recognition: Identifying individuals based on their unique vocal patterns.
- Retinal scan: A more secure but invasive method, reading the blood vessel patterns in your retina.
- Gait analysis: Capturing the rhythm and style of your walk for identification.
Benefits of Biometric Security:
- Enhanced security: Biometrics are more difficult to forge or steal than traditional methods like passwords or tokens.
- Convenience: No more remembering complex passwords or carrying keys. Simply be yourself to gain access.
- Accuracy: Most biometric systems offer high accuracy rates, minimizing the risk of unauthorized access.
- Improved user experience: Biometric authentication is often faster and more seamless than traditional methods.
The Future of Biometric Security:
As technology advances, we can expect even more innovative and sophisticated biometric solutions. Emerging trends include:
- Multi-factor authentication: Combining biometrics with other security layers for even greater protection.
- Continuous monitoring: Using biometrics for ongoing identity verification, not just at initial access points.
- Behavioral biometrics: Analyzing user behavior patterns, such as typing rhythm or mouse movement, for additional security layers.
Biometric security holds immense potential to revolutionize the way we secure our lives and data. However, it’s essential to consider ethical concerns and data privacy issues as we embrace this powerful technology.
In 2019, 27 Million Biometric System Data Breached

7 Biometric Security Techniques That Are Beyond Fingerprints:
Iris Scan:
- How it works: A high-resolution camera captures intricate details of your iris, including its texture, color, and unique patterns. Imagine zooming in on a snowflake – that’s how detailed it gets!
- Benefits: Super-high accuracy, even identical twins have different iris patterns. Difficult to fake or forge, resistant to masks and even contact lenses.
- Use cases: High-security facilities, border control, financial transactions.
Vein Recognition:
- How it works: Infrared scanners detect the heat patterns of your veins just below the skin’s surface. Your unique “veiny roadmap” becomes your personalized security key.
- Benefits: Extremely difficult to fool, as veins lie deeper than fingerprints and are harder to replicate. Works even with scars or injuries.
- Use cases: Secure access to personal devices, ATMs, and potentially future smartphones with built-in scanners.
Gait Analysis:
- How it works: Sensors track your movements as you walk, capturing the rhythm, stride length, and swing of your arms. It’s like your own personal “walk ID”!
- Benefits: Can be done unobtrusively at a distance, making it ideal for public spaces or surveillance. Less susceptible to changes in appearance like weight gain or aging.
- Use cases: Access control in buildings, continuous identity verification for secure areas, potentially future fitness trackers with gait analysis features.
Heartbeat Rhythm:
- How it works: Advanced sensors pick up on the subtle variations in your heartbeat, creating a unique biometric signature like a musical fingerprint.
- Benefits: Highly accurate and personal, as your heart rhythm is influenced by factors like genetics, fitness level, and even emotions. Difficult to fake or alter.
- Use cases: Potential for high-security applications like military installations or nuclear facilities. Could also be used for personalized health monitoring and early disease detection.
Brainwaves Mapping:
- How it works: Electroencephalography (EEG) measures the electrical activity of your brain, creating a unique pattern of “brainwaves” as individual as your personality.
- Benefits: Offers the ultimate in security, as brainwaves are deeply personal and nearly impossible to replicate. Could be combined with other biometrics for multi-factor authentication.
- Use cases: Still in early research stages, but could have potential for highly secure access control or even lie detection applications.
DNA Authentication:
- How it works: A tiny DNA sample, often obtained through a cheek swab, is analyzed to create a genetic fingerprint that is truly you. No two people (except identical twins) share the same DNA.
- Benefits: The ultimate “proof of identity,” offering extreme accuracy and security. Can be used for everything from immigration control to paternity testing.
- Use cases: High-security applications like government databases or sensitive medical records. Potential for personalized medicine and targeted therapies based on your unique genetic makeup.
Sweat Analysis:
- How it works: Sensors detect the unique chemical composition of your sweat, which is influenced by your diet, health, and even emotional state. It’s like a personalized biochemical signature!
- Benefits: Non-invasive and potentially continuous monitoring, as sweat is constantly produced. Offers additional security layers beyond traditional biometrics.
- Use cases: Potential for personalized fitness tracking, health monitoring, and even security applications where emotional state analysis could be relevant.
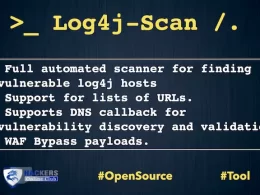
Are Biometric Scanners Safe?
According to Kaspersky report, the challenge is that biometric scanners, including facial recognition systems, can be tricked. Researchers at the University of North Carolina at Chapel Hill downloaded photos of 20 volunteers from social media and used them to construct 3-D models of their faces. The researchers successfully breached four of the five security systems they tested.
Examples of fingerprint cloning are everywhere. One example from the Black Hat cybersecurity conference demonstrated that a fingerprint can be cloned reliably in about 40 minutes with $10 worth of material, simply by making a fingerprint impression in molding plastic or candle wax, research added.
Remember, with all these amazing technologies, ethical considerations and data privacy remain crucial. Choose wisely and keep security your top priority!