Apple AirDrop Vulnerability – Phone Number and Email Address Could be Leakage.
The Cybersecurity researchers have discovered security flaws in Apple’s wireless file-sharing protocol that could allow user’s private contact information, including phone numbers and emails, to be exposed.
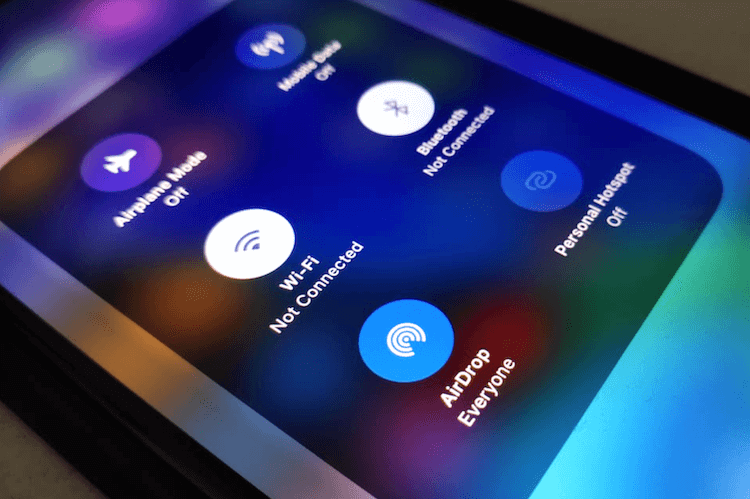
Apple AirDrop is a file-sharing service integrated into more than 1.5 billion end-user devices worldwide, including iPhone, iPad, and Mac systems.
What is in AirDrop Vulnerability?
“As an attacker, it is possible to learn the phone numbers and email addresses of AirDrop users – even as a complete stranger,” said a team of academics from the Technical University of Darmstadt, Germany. “All they require is a Wi-Fi-capable device and physical proximity to a target that initiates the discovery process by opening the sharing pane on an iOS or macOS device.”
In the research paper, the security researchers consider an adversary that wants to learn contact identifiers (phone numbers and email addresses) from non-contact AirDrop devices in proximity. They might then use these identifiers for fraudulent activities such as (spear) phishing attacks or making a profit by selling personal data. Specifically, the adversary must be in physical proximity of its targets and have access to a device with an off-the-shelf Wi-Fi card to communicate via AWDL.
“When an AirDrop connection is attempted between a sender and a receiver, the sender transmits over the air a message containing a hash, or digital fingerprint, of its user’s email address or phone number as part of an authentication handshake,” as explained in the research paper. “In response, if the sender is recognized, the receiver transmits back its hash.”
Researchers concluded that the root cause of the problem is Apple’s use of hash functions during the discovery process to hide the exchanged contact identifiers — phone numbers and email addresses during research.
Solution by security researcher –
PrivateDrop: Practical Privacy-Preserving Authentication for Apple AirDrop
As per responsible disclosure, “we informed Apple about the privacy issues in May 2019 via responsible disclosure and shared our PrivateDrop solution in October 2020. As of April 20, 2021, Apple has not indicated that they are working on a solution.”
This means Apple users are still vulnerable to the outlined privacy attacks. They can only protect themselves by disabling AirDrop discovery in the system settings and by refraining from opening the sharing pane.
“We developed a solution named PrivateDrop to replace the flawed original AirDrop design. PrivateDrop is based on optimized cryptographic private set intersection protocols that can securely perform the contact discovery process between two users without exchanging vulnerable hash values. Our prototype implementation of PrivateDrop on iOS/macOS shows that our privacy-friendly mutual authentication approach is efficient enough to preserve AirDrop’s exemplary user experience with an authentication delay well below one second.”
The implementation of PrivateDrop is publicly available on GitHub.