Microsoft removes Cryptojacking Apps From Its App Store.
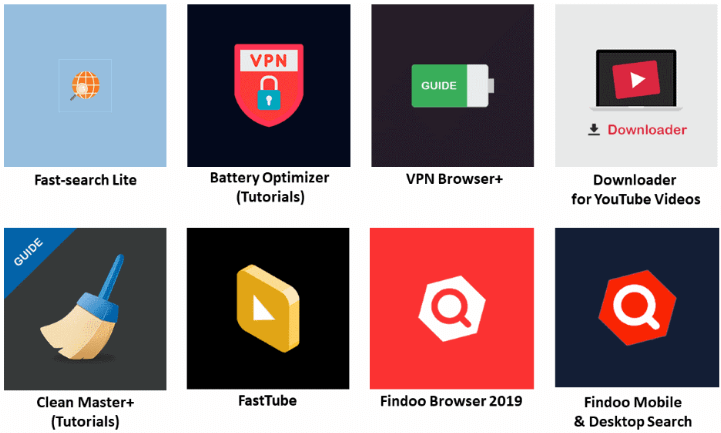
The malicious apps found by Symantec security researchers.
The apps which included those for computer and battery optimization tutorial, internet search, web browsers, and video viewing and download—came from three developers: DigiDream, 1clean, and Findoo.
CryptoJacking is a technique using by cyber attackers to mine the cryptocurrencies.
In total, Symantec has discovered eight apps from these developers that shared the same risky behavior. After further investigation, we believe that all these apps were likely developed by the same person or group.
When each app is launched, the domain is silently visited in the background and triggers GTM with the key GTM-PRFLJPX, which is shared across all eight applications. GTM is a legitimate tool that allows developers to inject JavaScript dynamically into their applications.
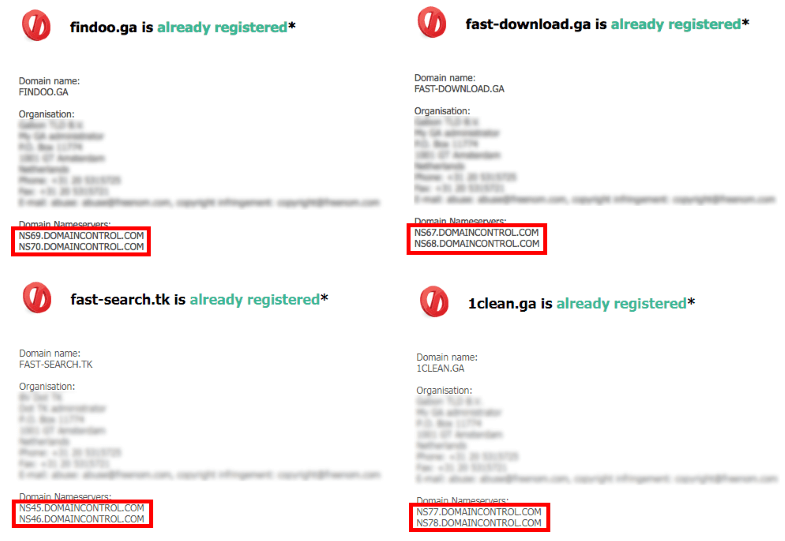
From the apps’ network traffic, Symantec found the hosting server for each app. Through a Whois query, we found that all of these servers actually have the same origin. Therefore, these apps were most likely published by the same developers using different names.
“These apps fall under the category of Progressive Web Applications, which are installed as a Windows 10 app running independently from the browser, in a standalone (WWAHost. exe process) window,” Symantec experts said in their report, explaining how these apps were able to run the Coinhive JavaScript code, to begin with.
“A malicious URL with mining script was detected, and we backtracked to find these applications,” Tommy Dong, Senior Principal Security Engineer at Symantec, told ZDNet. “Symantec AV can convict generic JS-based cryptocurrency mining disregarding any domain.”
“There is no throttling which means it uses up 100% of user’s CPU time. Opening the app will cause a detectable spike in CPU usage,” said Dong.
How to Stay protected from online threats.
- Keep your software up to date.
- Do not download apps from unknown sites.
- Only install apps from trusted sources.
- Pay close attention to the permissions requested by apps.
- Pay close attention to CPU and memory usage of your computer or device.
- Make frequent backups of important data.
Image source- Symantec