iPhone Hack – Through iOS Mail App Zero-Day Bug: Research
Security researchers of Zecops, found iOS vulnerability, which is attacking iOS Devices through MobileMail/Maild.
It can be exploited remotely by an attacker sending email, and it can use a large amount of RAM from the device. First it slow down your iPhone and then force to crash.
The attack’s scope consists of sending a specially crafted email to a victim’s mailbox enabling it to trigger the vulnerability in the context of iOS MobileMail application on iOS 12 or maild on iOS 13. Based on ZecOps Research and Threat Intelligence, we surmise with high confidence that these vulnerabilities – in particular, the remote heap overflow – are widely exploited in the wild in targeted attacks by an advanced threat operator(s).
Heap Overflow Bug
A heap overflow or heap overrun is a type of buffer overflow that occurs in the heap data area. Heap overflows are exploitable in a different manner to that of stack-based overflows. Memory on the heap is dynamically allocated at runtime and typically contains program data.
What is the Vulnerability?
The suspicious events included strings commonly used by hackers (e.g. 414141…4141). After verifying that it wasn’t a red-team exercise, we validated that these strings were provided by the email-sender. Noteworthy, although the data confirms that the exploit emails were received and processed by victims’ iOS devices, corresponding emails that should have been received and stored on the mail-server were missing. Therefore, we infer that these emails were deleted intentionally as part of attack’s operational security cleanup measures.
The researchers believe that these attacks are correlative with at least one nation-state threat operator or a nation-state that purchased the exploit from a third-party researcher in a Proof of Concept (POC) grade and used ‘as-is’ or with minor modifications (hence the 4141..41 strings).
Zecops researcher said,
We are aware of multiple attacks that happened starting from Jan 2018, on iOS 11.2.2. It is likely that the same threat operators are actively abusing these vulnerabilities presently. It is possible that the attacker(s) were using this vulnerability even earlier.
Vulnerability Details
ZecOps found that the implementation of MFMutableData in the MIME library lacks error checking for system call ftruncate() which leads to the Out-Of-Bounds write. We also found a way to trigger the OOB-Write without waiting for the failure of the system call ftruncate. In addition, we found a heap-overflow that can be triggered remotely.
We are aware of remote triggers of both vulnerabilities in the wild in targeted attacks.
Both the OOB Write bug, and the Heap-Overflow bug, occurred due to the same problem: not handling the return value of the system calls correctly.
The remote bug can be triggered while processing the downloaded email, in such scenario, the email won’t get fully downloaded to the device as a result.
Affected Library: /System/Library/PrivateFrameworks/MIME.framework/MIME Vulnerable function: -[MFMutableData appendBytes:length:]
What Happen Once it Exploited
Abnormal behavior once the vulnerabilities are exploited. Besides a temporary slowdown of mobile mail application, users should not observe any other anomalous behavior. Following an exploit attempt (both successful / unsuccessful) on iOS 12 – users may notice a sudden crash of the Mail application.
On iOS13, besides a temporary slowdown, it would not be noticeable. Failed attacks would not be noticeable on iOS 13 if another attack is carried afterwards and deletes the email.
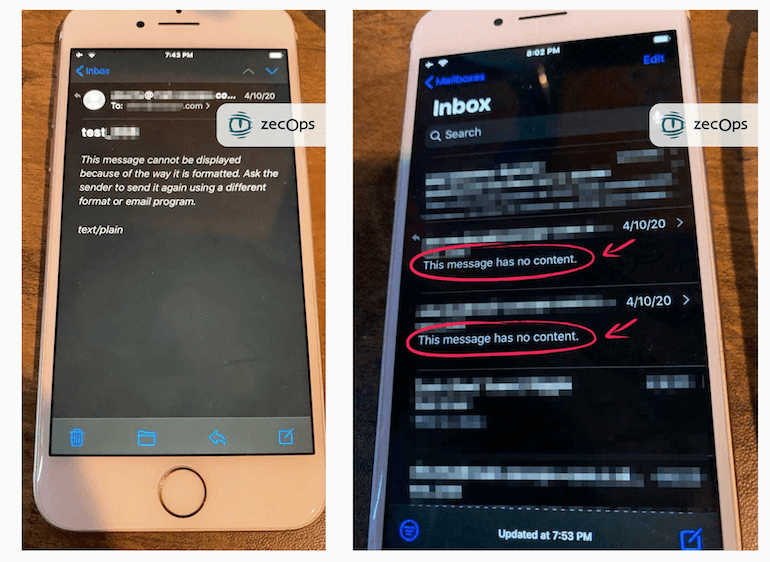
In failed attacks, the emails that would be sent by the attacker would show the message: “This message has no content.”.. As seen in the following picture below:
Vulnerability Impact:
- The vulnerability allows remote code execution capabilities and enables an attacker to remotely infect a device by sending emails that consume significant amount of memory
- The vulnerability does not necessarily require a large email – a regular email which is able to consume enough RAM would be sufficient. There are many ways to achieve such resource exhaustion including RTF, multi-part, and other methods
- The heap overflow vulnerability is exploited in the wild
- The vulnerability can be triggered before the entire email is downloaded, hence the email content won’t necessarily remain on the device
- We are not dismissing the possibility that the attackers deleted any remaining emails following a successful attack, said Zecops.
Patch
Apple patched both vulnerabilities in iOS 13.4.5 beta version, it will be released in public soon.











