Browsing Category
Tutorials
110 posts
iOS Penetration Testing- Frida And Objection- Part 3
iOS Penetration Testing Part 3 This post is part 3 of a series giving an overview of the…
April 2, 2019
Wireshark Commands Cheatsheet
Wireshark is a free and open-source packet analyzer. It is used for network troubleshooting, analysis, software and communications…
April 1, 2019
CRLF Injection Define
CRLF Injection defines as CR (Carriage Return) and LF (Line Feed). CRLF Injection is a one of types…
March 29, 2019
iOS Penetration Testing- Cycript A Runtime Manipulation- Part 2
Previously we have posted iOS Penetration Testing App Decryption And Jailbreaking- Part 1 Now, this post is part…
March 23, 2019
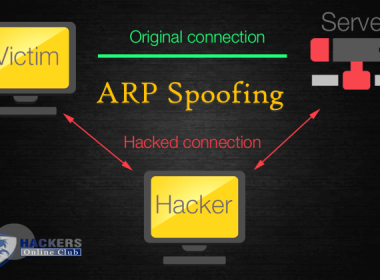
Address Resolution Protocol ARP Spoofing- Detection And Prevention
The Address Resolution Protocol (ARP) spoofing is a type of cyber attack wherein attackers send malicious ARP Packets…
March 20, 2019
iOS Penetration Testing- App Decryption And Jailbreaking- Part 1
iOS Penetration Testing- App Decryption, Class-dump and Jailbreak – Part 1 Security researcher Allyson O’Malley shared iOS Pentesting…
March 19, 2019
How Security Researcher Found Stored XSS in Outlook And Got 1000 USD Bounty
Bug Bounty- $1,000 USD In 5 Minutes For Stored XSS In OUTLOOK.COM Security researcher Omar Espino got the…
March 18, 2019
Command Injection Cheatsheet
Command injection is an attack in which the goal is execution of arbitrary commands on the host operating…
March 9, 2019
After Ransomware and CryptoJacking The New Form of Cyber Threat is “FormJacking”
Earlier we had talked about Ransomwares and CryptoJacking, but now security researchers have found new Cyber threat known…
February 21, 2019
How To Fix Windows 10 Update Issue
Fix Windows 10 Update Issue by Google Public DNS By updating a Windows device it is quite problem…
February 2, 2019