Browsing Category
Security
475 posts
Understanding Infosec Isolation Solutions: Fortress Walls for Your Digital Assets
Information security (Infosec) is paramount in today’s ever-evolving digital landscape. Infosec isolation solutions are crucial for defense. Let’s…
April 8, 2024
Hackers Target macOS Users with Malicious Ads: A Deeper Look
A recent research highlights a concerning trend: hackers targeting macOS users with malicious advertisements, and can say Malvertising.…
April 1, 2024
Cyber Flashing: A Digital Intrusion
Cyber flashing, a relatively new term, describes the act of sending unsolicited explicit images or videos to someone…
March 20, 2024
6 Benefits of Vulnerability Management
Vulnerability management is an ongoing process that helps identify, evaluate, remediate, and mitigate computer and software system vulnerabilities.…
March 12, 2024
Microsoft Unveiled Cyberattack By Russian Group Midnight Blizzard Targets Email
In a recent Microsoft security update, Microsoft unveiled, a cyberattack by a Russia-affiliated threat actor as Midnight Blizzard,…
March 9, 2024
INDIA Fights Cybercrime with Two New Initiatives: Digital Intelligence Platform (DIP) And Chakshu
India has taken a significant step towards curbing cybercrime and financial fraud with the launch of two new…
March 7, 2024
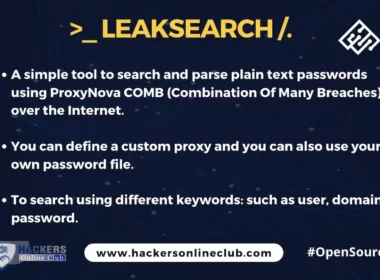
Leaksearch – To Search and Parse Plain Text Passwords Using ProxyNova
LeakSearch is a simple tool to search and parse plain text passwords using ProxyNova COMB (Combination Of Many…
March 5, 2024
AT&T Cell Service Outage in United States – Analysis Report
On February 22, 2024, AT&T, one of the major telecommunications providers, experienced a significant cell service outage, impacting…
February 22, 2024
Google Magika: Open-Sourcing AI-Powered File Type Identification
Google has announced the open-sourcing of Magika, an AI-powered file type identification system. This move aims to empower…
February 21, 2024
Alert: iPhone Push Notifications Exploited Users Data – Security Research
Mysk Security Reveals – iPhone Push Notifications Exploited by Malicious Players for Sneaky Data Harvesting! The security researcher…
January 27, 2024