From a security point, a CI/CD pipeline is a highvalue attack surface—a trusted automation system that builds, tests, and deploys code across your entire software ecosystem. If compromised, attackers gain automated, privileged access to your production environments, source code, secrets, and customer data.
Critical Insight: A CI/CD pipeline isn’t just a productivity tool—it’s a crown jewel asset. Securing it is as important as protecting your production servers or domain controllers.
Core Security Definition:
A secure CI/CD pipeline ensures that every code change is authenticated, authorized, integrity verified, and auditable from commit to deployment—preventing malicious actors from injecting backdoors, stealing secrets, or hijacking release processes.
Why CI/CD Pipelines Are Prime Cyber Targets
Threat Vector | Why It’s Dangerous | Real-World Example |
|---|---|---|
Compromised Credentials | CI runners often hold cloud IAM keys, API tokens, or SSH access | CodeCov breach (2021): Attackers stole credentials via modified Bash Uploader |
Malicious Dependency Injection | Attackers poison open-source libraries to execute code during build | event-stream npm package (2018): Cryptocurrency theft via compromised dependency |
Pipeline Configuration Abuse | Misconfigured YAML workflows can be exploited for crypto-mining or data exfiltration | GitHub Actions misconfigurations leading to container escapes |
Artifact Tampering | Unsigned or unverified build artifacts enable supply chain attacks | SolarWinds SUNBURST: Backdoored update signed with legitimate certificate |
Secrets Leakage in Logs | Debug logs or error traces may expose tokens, passwords, or keys | Multiple incidents where CI logs leaked AWS credentials to public repositories |
Insider/Contributor Threat | Malicious actors with commit access can inject code that bypasses reviews | 3CX Desktop App (2023): Compromised build pipeline distributed trojanized software |
2026 Threat Intelligence:
- 74% of organizations experienced at least one CI/CD security incident in the past 12 months (Sonatype, 2025)
- Average dwell time for pipeline compromises: 47 days (vs. 9 days for direct infrastructure attacks)
- 61% of breaches involved stolen or misused CI/CD credentials (Ponemon Institute)
CI/CD Attack Kill Chain: How Hackers Exploit Pipelines
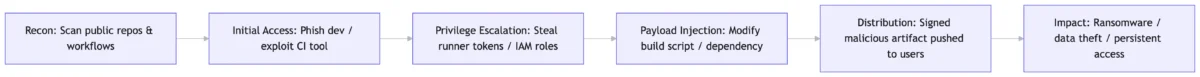
StagebyStage Breakdown:
1. Reconnaissance
- Scan GitHub/GitLab for public workflows, exposed secrets, or outdated dependencies
- Identify highvalue targets: fintech, healthcare, government contractors
2. Initial Compromise
- Phish a developer with pipeline writeaccess
- Exploit unpatched CI server (e.g., Jenkins RCE vulnerabilities)
- Abuse OAuth misconfigurations in GitHub Actions
3. Persistence & Lateral Movement
- Inject malicious steps into `.github/workflows/.yml`
- Steal runner environment variables containing cloud credentials
- Move from CI runner to production via deployed artifacts
4. Payload Delivery
- Insert backdoor into compiled binary or container image
- Modify dependency versions to pull malicious packages
- Disable security scans via conditional logic in pipeline scripts
5. Impact Execution
- Deploy ransomware via “legitimate” update channel
- Exfiltrate source code, customer PII, or API keys
- Establish C2 communication through approved egress paths
Securing Your CI/CD Pipeline: DevSecOps Best Practices
1. Adopt Zero Trust for Pipeline Identity
- Use shortlived, workloadspecific credentials (e.g., GitHub OIDC → AWS IAM)
- Never store longlived secrets in environment variables or config files
- Enforce justintime access for approvers via PAM solutions
2. Enforce Artifact Integrity & Provenance
- Sign all build artifacts with Cosign/Sigstore or GPG
- Generate and verify SLSAcompliant provenance attestations
- Block deployment of unsigned or unverified artifacts via policyascode (OPA/Conftest)
3. Shift Security Left: Automated Scanning Gates
Scan Type | When to Run | Tools |
|---|---|---|
Secret Detection | Pre-commit & build | TruffleHog, GitGuardian, gitleaks |
SAST | On pull request | Semgrep, CodeQL, SonarQube |
SCA / SBOM | Dependency install & build | Syft, Grype, Snyk, Dependabot |
IaC Security | Terraform/CloudFormation linting | Checkov, tfsec, cfn-nag |
Container Scanning | Post-build, pre-deploy | Trivy, Clair, Docker Scout |
DAST / API Testing | Staging environment | OWASP ZAP, Burp Suite, k6 |
4. Harden Pipeline Infrastructure
- Run CI jobs in ephemeral, isolated containers (no persistent state)
- Apply network policies to restrict runner egress (block unknown domains)
- Enable audit logging for all pipeline executions and secret accesses
- Use private runners for sensitive workflows (avoid public cloud shared runners)
5. Implement PolicyasCode & Compliance Guardrails
yaml
Example: OPA policy blocking critical CVEs
deny[msg] {
input.vulnerabilities[cve].severity == "CRITICAL"
msg := sprintf("Deployment blocked: Critical CVE %v detected", [cve])
}Enforce rules like:
- “No deployment without SBOM”
- “Block dependencies with known malicious indicators”
- “Require 2person approval for production releases”
- “Mandate SLSA Level 3 provenance for all artifacts”
6. Monitor, Detect & Respond to Pipeline Anomalies
Alert on:
- Unusual build durations or resource spikes
- New/unapproved workflow files merged to main
- Secret access from unexpected geolocations or IPs
- Artifact signature verification failures
Integrate pipeline logs into your SIEM/SOAR (Splunk, Sentinel, Chronicle)
Maintain a CI/CDspecific incident response playbook with rollback procedures
Compliance Frameworks & Standards (2026)
Framework | Relevance to CI/CD Security |
|---|---|
SLSA Framework (Google) | Provides graduated levels (1-4) for build integrity, provenance, and supply chain security |
NIST SSDF (SP 800-218) | Secure Software Development Practices: “Protect pipelines” is a core requirement |
ISO/IEC 27001:2022 | Controls A.8.28 (Secure development), A.8.33 (Logging), A.5.23 (Cloud security) |
EU Cyber Resilience Act (Effective 2026) | Mandates SBOMs, vulnerability handling, and secure-by-default development for commercial software |
CISA Secure by Design | Requires vendors to publish SBOMs, enable auto-updates, and reduce exploitability |
Pro Tip: Map your pipeline controls to these frameworks early—compliance becomes evidence, not an afterthought.
Security Tools for CI/CD (2026 Stack)
Category | Recommended Tools |
|---|---|
Secrets Management | HashiCorp Vault, AWS Secrets Manager, Doppler, GitGuardian |
Artifact Signing | Sigstore/Cosign, Notary, GPG, in-toto |
Pipeline Security | StepSecurity, Chainguard Enforce, Snyk Code, GitHub Advanced Security |
SBOM & Dependency Tracking | Syft + Grype, Dependency-Track, Microsoft SBOM Tool |
Policy Enforcement | Open Policy Agent (OPA), Kyverno, Conftest, HashiCorp Sentinel |
Runtime Protection | Falco, Tetragon, Aqua Security, Wiz Runtime |
Emerging Trend (2026): AIpowered pipeline anomaly detection—using behavioral baselines to flag suspicious workflow changes or build patterns in real time.
Incident Response: If Your Pipeline Is Compromised
1. Isolate: Immediately pause all pipeline executions and revoke runner tokens
2. Contain: Rotate all credentials accessed by the compromised pipeline (cloud keys, API tokens, SSH keys)
3. Investigate: Audit workflow history, artifact logs, and deployment records for malicious changes
4. Eradicate: Remove malicious code, rebuild from trusted source, resign artifacts
5. Recover: Restore services from verified clean artifacts; monitor for postcompromise activity
6. Learn: Conduct blameless postmortem; update pipeline policies and detection rules
PrePrepare: Maintain a “breakglass” runbook with preapproved emergency procedures for pipeline lockdown.
CI/CD Security Checklist (Quick Reference)
- All pipeline definitions stored in version control with PR reviews
- Secrets managed via dedicated vault—never hardcoded or in repo
- Build artifacts signed and verified before deployment
- SBOM generated and scanned for every build
- Critical CVEs block pipeline progression (policyascode enforced)
- CI runners run as nonroot, with minimal IAM permissions
- Audit logs shipped to SIEM with alerting on anomalies
- Regular redteam exercises targeting pipeline infrastructure
- Developer training on secure workflow authoring and secret hygiene
- Vendor risk assessments for thirdparty CI/CD tools and actions
FAQ: CI/CD Security
Q: What is the 1 CI/CD security mistake teams make?
A: Storing longlived secrets (API keys, cloud credentials) in environment variables or config files. Always use shortlived, workloadidentity federation (e.g., GitHub OIDC → AWS IAM).
Q: How do I prevent malicious dependencies from entering my pipeline?
A: Pin dependency versions, enable automated SCA scanning (Snyk, Dependabot), generate SBOMs, and enforce policies that block packages with known malicious indicators or poor maintenance signals.
Q: Is opensource CI/CD tooling (like GitHub Actions) less secure than selfhosted?
A: Not inherently—but each has different risk profiles. Public runners offer isolation but shared infrastructure risks; selfhosted runners give control but require rigorous hardening. Focus on configuration, not just tool choice.
Q: How often should we audit our CI/CD pipeline security?
A: Continuously. Automate policy checks on every commit. Conduct manual architecture reviews quarterly and redteam exercises biannually.
Q: Can we achieve “secure by default” CI/CD?
A: Yes—by templating secure workflows (e.g., preconfigured with signing, scanning, leastprivilege), enforcing organizationwide policies, and onboarding projects via secure scaffolding tools.