What Is a Supply Chain Attack?
A supply chain attack is a cybersecurity breach where attackers compromise a trusted third-party vendor, software library, service provider, or hardware manufacturer to indirectly infiltrate their customers or users. Instead of attacking the final target directly, hackers exploit the trust, access, or update mechanisms built into the supply chain.
Think of it like poisoning a city’s water supply instead of breaking into individual homes. Once the source is tainted, everyone connected to it is affected.
These attacks target:
- Software dependencies & open-source packages
- SaaS & cloud service providers
- Hardware/firmware manufacturers
- Managed service providers (MSPs)
- CI/CD pipelines & code repositories
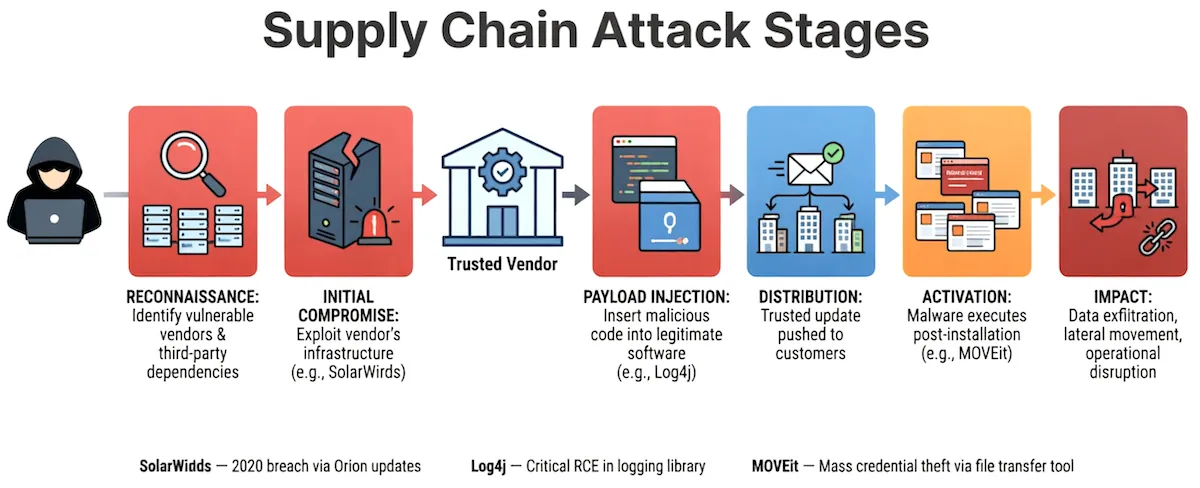
How Supply Chain Attacks Actually Work (Step-by-Step)
- Reconnaissance – Attackers map third-party vendors, open-source projects, or update servers used by high-value targets.
- Initial Compromise – They breach a vendor via phishing, credential stuffing, zero-day exploits, or insider access.
- Payload Injection – Malicious code, backdoors, or vulnerable dependencies are inserted into software updates, libraries, or service configurations.
- Distribution – The compromised asset is signed, packaged, and pushed to customers as a “trusted” update.
- Activation & Lateral Movement – Once installed, the payload executes, often with elevated privileges, bypassing perimeter defenses.
- Data Exfiltration – Attackers steal data, deploy ransomware, or maintain long-term access across multiple organizations.
Real-World Impact
Supply chain attacks bypass traditional security controls because they arrive through trusted channels. The ripple effects include:
Impact Area | Consequences |
|---|---|
Security | Bypassed firewalls, EDR, and MFA; privileged access granted natively |
Financial | Average breach cost exceeds $5M; regulatory fines, lawsuits, lost contracts |
Operational | Weeks of downtime, forced patching, vendor replacement, service disruption |
Reputational | Loss of customer trust, brand damage, partner relationship strain |
Compliance | Violations of GDPR, HIPAA, PCI-DSS, SEC disclosure rules, EU Cyber Resilience Act |
Industry Insight (2025–2026):
Over 62% of enterprises report at least one third-party security incident annually. Supply chain breaches take 3–5x longer to detect than direct attacks.
Examples (With Practical Breakdowns)
1. SolarWinds Orion (2020)
- How it happened: Attackers infiltrated SolarWinds’ build system, injected SUNBURST backdoor into a legitimate software update.
- Impact: 18,000+ organizations downloaded the update; U.S. government agencies and Fortune 500 companies compromised.
- Practical Takeaway: Code signing ≠ security. Always verify build environment integrity and monitor update behavior.
2. Log4Shell / Log4j (2021)
- How it happened: A single, widely used Java logging library contained a remote code execution flaw.
- Impact: Millions of applications globally exposed; patching took months due to nested dependencies.
- Practical Takeaway: Open-source is free, not risk-free. Maintain a Software Bill of Materials (SBOM) and automate dependency scanning.
3. MOVEit Transfer (2023)
- How it happened: Clop ransomware gang exploited a zero-day in Progress Software’s file-transfer platform.
- Impact: 2,500+ organizations breached; 80M+ personal records exposed across payroll, healthcare, and logistics sectors.
- Practical Takeaway: SaaS/MSP tools centralize risk. Enforce vendor SLAs for vulnerability disclosure and test incident playbooks.
4. 3CX Desktop App (2023)
- How it happened: Attackers compromised a third-party library in 3CX’s macOS/Windows build pipeline, shipping trojanized installers.
- Impact: Enterprise VoIP systems globally infected; attackers gained network persistence via legitimate app traffic.
- Practical Takeaway: Secure your CI/CD pipeline. Isolate build environments, enforce strict dependency pinning, and verify installer hashes.
Key Red Flags & Why They’re Hard to Detect
- Legitimate certificates – Attackers abuse or steal code-signing keys.
- Normal update behavior – Malware hides in routine patch cycles.
- Delayed activation – Payloads lie dormant for weeks/months.
- Shared infrastructure – Multi-tenant SaaS masks malicious activity.
- Over-trusted permissions – Third-party apps often request broad OAuth/scopes.
Detection Tip: Monitor for unusual outbound traffic from vendor processes, unexpected privilege escalations, and anomalous dependency version changes.
How to Prevent & Defend Against Supply Chain Attacks
1. Implement Software Bill of Materials (SBOM)
- Use standards like SPDX or CycloneDX.
- Automate generation via CI/CD tools (Syft, Trivy, Dependency-Track).
- Validate against known CVEs and policy rules before deployment.
2. Adopt Zero Trust for Third Parties
- Enforce least-privilege access for vendors.
- Use short-lived credentials, MFA, and network microsegmentation.
- Continuously validate vendor identity and posture.
3. Secure Your CI/CD Pipeline
- Isolate build runners, sign artifacts, and verify checksums.
- Implement provenance standards (SLSA Framework Level 3+).
- Block unsigned or unverified dependencies.
4. Vendor Risk Management (VRM)
- Assess vendors before onboarding (security questionnaires, pentest reports, compliance certs).
- Require breach notification SLAs (<72 hrs) and right-to-audit clauses.
- Maintain a risk-tiered vendor inventory.
5. Runtime & Behavioral Monitoring
- Deploy EDR/XDR with supply chain-specific detection rules.
- Monitor for abnormal API calls, unusual data egress, and process lineage anomalies.
- Use threat intelligence feeds tracking compromised packages/vendors.
6. Incident Response & Recovery
- Maintain a supply chain-specific IR playbook.
Pre-approve rollback procedures for vendor updates.
Conduct tabletop exercises simulating third-party compromise.
Role-Based Action Plan
Role | Immediate Actions |
|---|---|
CISO / Leadership | Mandate SBOM adoption, fund VRM program, align with SEC/EU disclosure rules |
Developers / DevOps | Pin dependencies, enable dependency scanning, enforce signed commits & build provenance |
Procurement / Legal | Add cybersecurity clauses to contracts, require breach reporting, audit vendor certs |
SOC / IR Teams | Tune detection rules for vendor traffic, maintain blocklists, run simulation drills |
What’s Next? 2025–2026 Supply Chain Threat Trends
- AI-Generated Dependencies: Attackers publish malicious packages with AI-optimized code that bypasses static scanners.
- SaaS Supply Chain Fragility: Over-reliance on interconnected APIs creates cascade failure risks.
- Hardware/Firmware Attacks: Compromised BIOS, TPM, or IoT chiplets enter enterprise networks pre-installed.
- Regulatory Enforcement: EU Cyber Resilience Act (fully active 2026), U.S. EO 14028 updates, and SEC rules mandate transparency and accountability.
- Automated SBOM Validation: AI-driven policy engines will auto-block non-compliant dependencies at merge time.
FAQ
What is a supply chain attack in cybersecurity?
A supply chain attack occurs when hackers compromise a trusted vendor, software library, or service provider to indirectly breach their customers through legitimate updates or integrations.
How can I tell if my organization is at risk?
If you use third-party software, SaaS platforms, open-source libraries, MSPs, or cloud services, you’re exposed. Risk increases with poor vendor vetting, untracked dependencies, and overly permissive integrations.
Are open-source libraries safe to use?
Yes, but they require active management. Always pin versions, scan for vulnerabilities, maintain an SBOM, and monitor for abandoned or suspicious packages.
What’s the difference between supply chain and third-party risk?
Third-party risk is the broad category of vendor-related exposures. Supply chain attacks are a specific, high-impact subset where attackers weaponize trusted software, updates, or services to infiltrate multiple organizations.
How long does it take to detect a supply chain breach?
Industry averages range from 90 to 210 days. Delayed detection is common because malicious traffic originates from trusted, signed, and approved sources.
Final Thoughts: Trust, But Verify
Supply chain attacks exploit the very foundation of modern technology: collaboration, reuse, and trust. You can’t eliminate third-party dependencies, but you can architect for verification.