Cyber Security analysts at Malwarebytes and Have I Been Pwned suggest this data was actually “scraped”—harvested via an API vulnerability—dating back to 2024. However, the data is being actively traded now, leading to a sudden surge in unauthorized login attempts.
What was leaked?
The dataset allegedly contains highly sensitive personally identifiable information (PII), including:
- Full Names and Usernames
- Verified Email Addresses
- International Phone Numbers
- Partial Physical Addresses
- User IDs and Location Data

Current Threat: The “Reset Link” Wave
Many users are reporting a flurry of unsolicited password reset emails.
The Hackers’ Strategy: They use the leaked emails and phone numbers to trigger legitimate password reset requests from Instagram.
The Trap: They hope you will panic, click the link, and accidentally hand over control or be redirected to a fake “support” page designed to steal your Two-Factor Authentication (2FA) codes.
17.5 Million Instagram “Leak”. Meta (Instagram’s parent company) has officially denied that their core systems were breached.
Instagram update status.
We fixed an issue that let an external party request password reset emails for some people. There was no breach of our systems and your Instagram accounts are secure.
You can ignore those emails — sorry for any confusion.
The Controversy: Is it New?
There is a major debate between security researchers and Meta (Instagram’s parent company):
- The “New” Theory: Some reports suggest this is a fresh leak from an API vulnerability discovered in late 2024 or early 2025.
- The “Recycled” Theory: Other researchers argue this data was actually scraped years ago (between 2017 and 2022) and is simply being re-packaged and sold as “new” to increase its value on the dark web.
- Meta’s Stance: Meta has largely denied a new breach of their systems. They attributed the recent wave of unsolicited “password reset” emails to a technical bug or external parties trying to trigger notifications, rather than a direct hack of their servers.
Why You Should Be Concerned
Even if the data is “old,” its public resurgence has triggered a wave of active attacks.
- Password Reset Flooding: Millions of users reported receiving legitimate-looking password reset emails they didn’t request. Hackers use these to confuse you or trick you into clicking a phishing link that steals your actual login.
- Phishing & Social Engineering: With your phone number and email, scammers can send “urgent” texts or calls pretending to be Instagram Support to “verify” your account, eventually asking for your 2FA code.
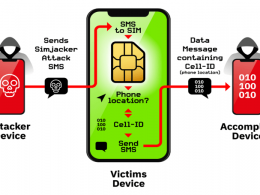
- SIM Swapping: Exposed phone numbers are the first step for hackers to take over your mobile carrier account and intercept SMS-based security codes.
How to Protect Your Account Now?
Whether you think you’re part of the 17.5 million or not, take these steps immediately:
- Don’t Click: If you get a password reset email you didn’t ask for, ignore it. Do not click any links inside.
- Enable App-Based 2FA: Switch from SMS-based two-factor authentication to an app like Google Authenticator or Duo. SMS codes are too easy to intercept.
- Update Your Password: If you haven’t changed your password in the last year, now is a good time—manually, through the official app settings.
- Review Logged-In Devices: Go to Settings > Accounts Center > Password and Security > Where you’re logged in and log out of any device you don’t recognize.
- Check Insta page here if your account were compromised.